All You Need to Know About the OSI Model
The networking world is full of models. Don’t get too excited, the models we are talking about are OSI and TCP/IP models and not Gisele Bundchen or Cindy Crawford. However, to be completely honest the networking types of models can be just as interesting to someone as interested in networking as a beautiful runway model. That is exactly what we are going to go over today, the OSI Model. Something you must be familiar with if you have any desire to be a networking professional or obtain your CompTIA Network+ or CCNA certification.
In 1978 the International Organization for Standarization (ISO) began working on the Open Systems Interconnection model (OSI model). The model is a method for separating a communication system into multiple layers. The OSI model is made up of the following seven layers: Physical, Data Link, Network, Transport, Session, Presentation, and Application. Here is a visual representation of the OSI model:
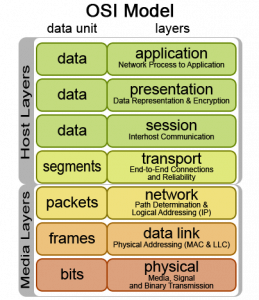
Now we will go over what each layer of the OSI model is responsible for.
Physical Layer
The Physical Layer is the first layer of the OSI model and defines the physical and electrical specifications for devices. More specifically, it describes the connection between a device and physical cable such as fiber optics. The specifications includes several things, like network adapters, layout of pins, cable specifications and more. The Physical Layer’s primary concern is the interaction between a single device and the method for which data is transmitted.
- The three major functions of the Physical Layer are to:
- Establish and Terminate a connection to a connection medium.
- Participate in the process of sharing communication resources across multiple users, such as flow control (the process of managing the rate at which data transmitted to avoid a fast sender from outrunning a slow receiver).
Modulate between digital data in user equipment and the corresponding signals being transmitted over a communications channel.
Data Link Layer
The Data Link layer is typically referred to as Layer 2 and performs the functional and procedural means to transfer data between network devices and detect and possibly correct errors that could occur in the Physical Layer. If you ever hear someone referring to a “Layer 2 address” they are referring to a MAC address. The following devices operated at the Data Link Layer: L3 bridges, switches, cable modems, wireless access points, and more.
Four major specifications that run at the Data Link Layer are:
- Ethernet
- HDLC (High Data Link Control)
- PPP (Point-to-Point Protocol)
- Frame Relay
Network Layer
The Network Layer is the third layer in the OSI model. This is sometimes called the “Routing Layer” because routers operate at this layer. The Network Layer is responsible for finding the best paths to take to the destination from the router and which path is optimal.
Three sub-layers make up the Network Layer, these are: Subnetwork Access, Subnetwork Dependent Convergence, and Subnetwork Independent Convergence.
There are a several layer management protocals within the Network layer. Some of these include multicast group management, Network Layer address assignment, routing protocols, and more.
Transport Layer
The fourth layer of the OSI model is the Transport Layer. It is responsible for establishing a logical end-to-end connection between two network devices to provide transparent data transmission. The Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) operate within this layer even though they were not developed under the OSI model.
The Transport Layer uses several techniques such as Cyclic Redundancy Check, acknowlegements, and windowing to check for data transmission errors. The retransmission of data to recover those errors or lost data occurs with the software managing the Transport Layer.
Session Layer
The Session Layer is the fourth layer of the OSI model and is responsible for the two-way communication between remote hosts. This layer handles the creation, maintenance, and teardown of communication between these hosts. It is called the Session Layer because the communication is referred to as a “session”. Sessions are used to track individual connections to remote servers. An example of a session would be your web browser or FTP application.
The Session Layer is performs these functions:
- Communication with layer five or the Presentation Layer.
- Manage single or multiple connections between hosts.
- Communication with the Transport Layer below.
Presentation Layer
The fifth layer of the OSI model is the Presentation Layer. This layer manages the conversion of data between platform independent or standards based formats to a format that can be processed by a local machine. An example of this function is the conversion of a .wav file to a .MP3. Some other examples of file types used at the Presentation Layer are JPEG, ASCII, MIDI, and MPEG.
There are four primary tasks performed by this layer:
- Ensures commpatibility with the operating system.
- Proper encapsulation of data for network transmission.
- Data formatting
- Data encryption, which includes translation and compression.
Application Layer
The Application Layer is the seventh layer of the OSI model. This is where the user interacts with the network. Authentication services run at this layer. The Application Layer makes sure that a remote connection is available, communication resources exist, and that both devices agree on processes involving data integrity, privacy, and error recovery.
Protocols that operate at the Application layer include SMTP, POP3, HTTP, FTP, Telnet, and SNMP to name a few.
Conclusion
As you can probably tell the OSI model is much more rigidly defined then the TCP/IP model we went over last week. Howevery both of these models are very important for aspiring networking professionals to familiarize themselves with.
We hope that you have enjoyed this article and have learned a great deal about the OSI model. If you have any questions or opinions please post them in the comments. We look forward to reading them.

