Exam Code: FCP_FGT_AD-7.6
Exam Name: FCP - FortiGate 7.6 Administrator
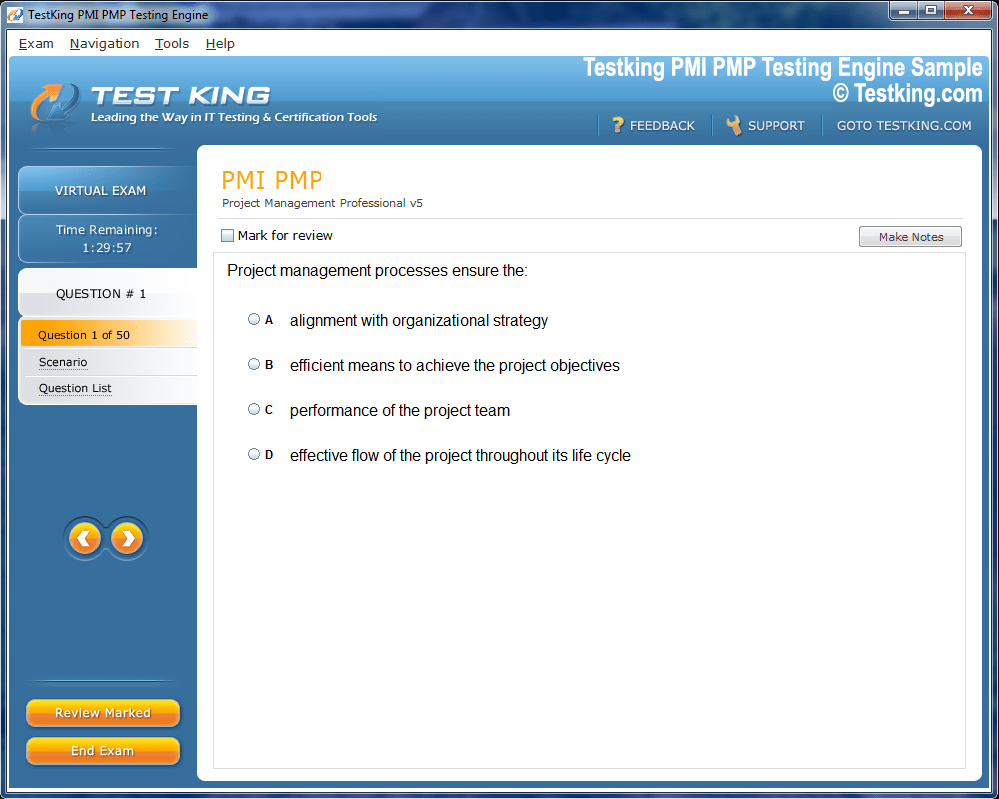
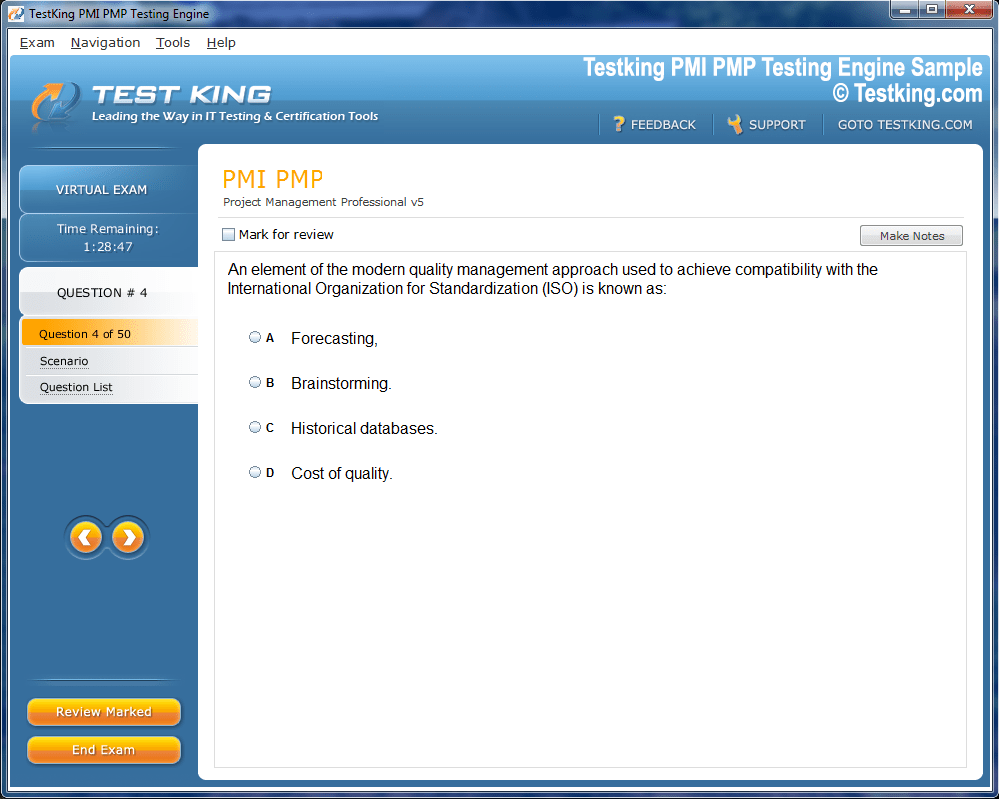
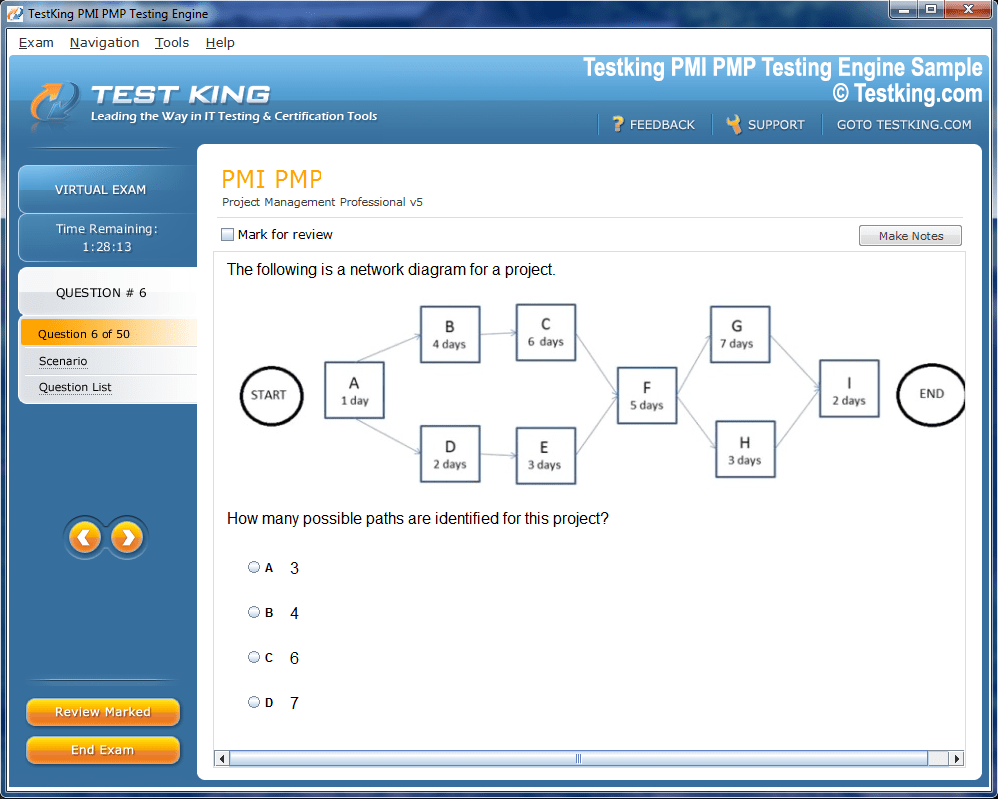
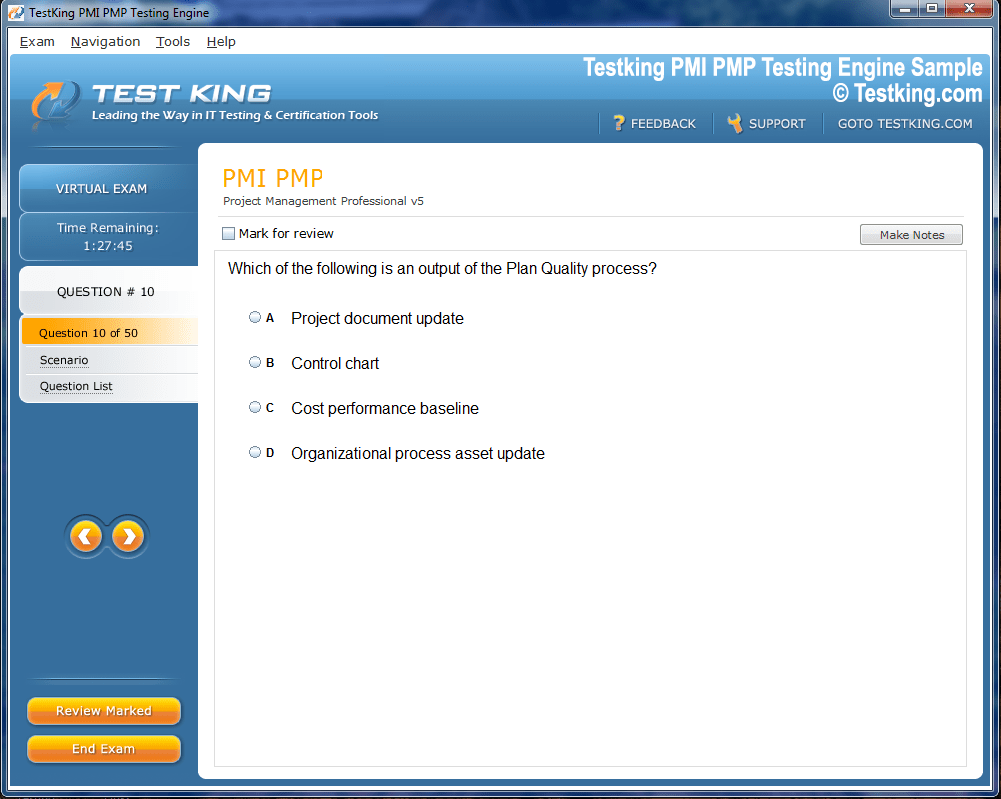
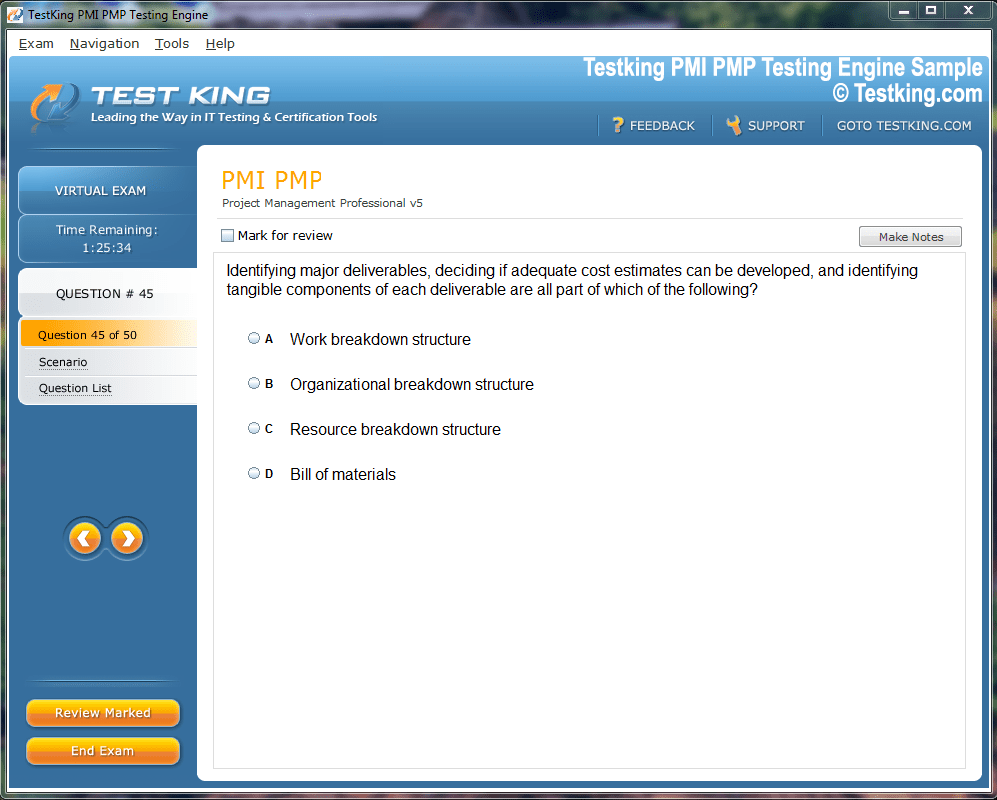
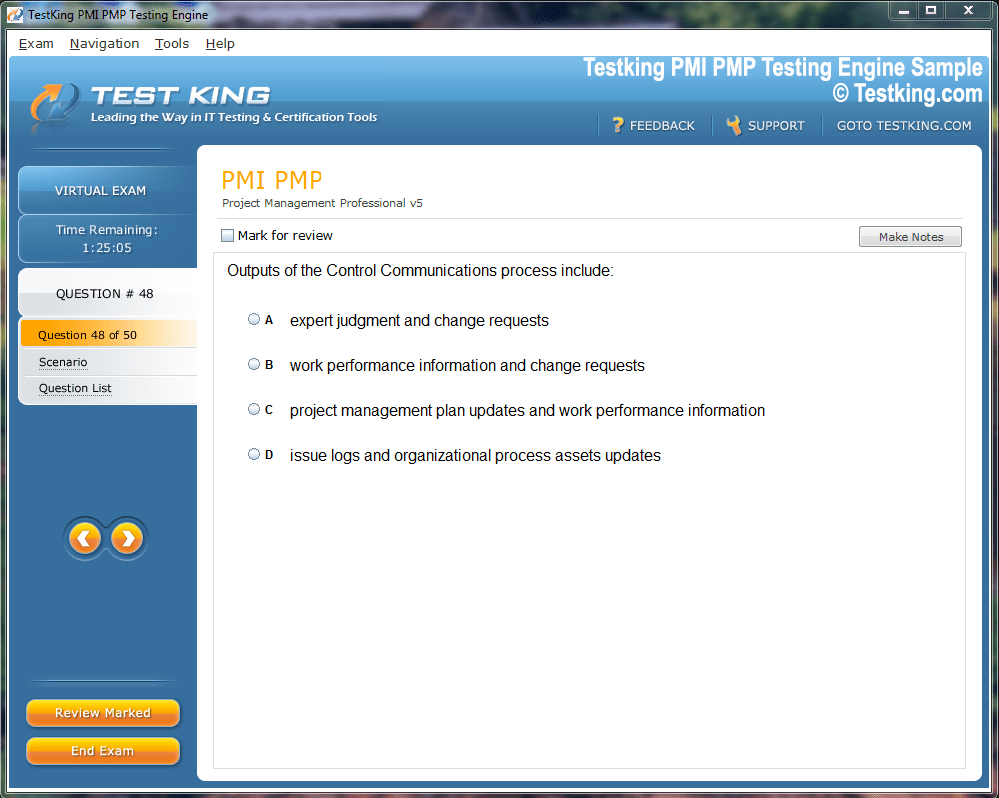
Product Screenshots
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our FCP_FGT_AD-7.6 testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.
Top Fortinet Exams
- NSE4_FGT_AD-7.6 - Fortinet NSE 4 - FortiOS 7.6 Administrator
- FCSS_EFW_AD-7.6 - NSE 7 - Enterprise Firewall 7.6 Administrator
- FCSS_NST_SE-7.6 - Fortinet NSE 6 - Network Security 7.6 Support Engineer
- FCP_FMG_AD-7.6 - Fortinet NSE 5 - FortiManager 7.6 Administrator
- FCP_FGT_AD-7.6 - FCP - FortiGate 7.6 Administrator
- FCSS_LED_AR-7.6 - Fortinet NSE 6 - LAN Edge 7.6 Architect
- FCP_FAZ_AN-7.6 - Fortinet NSE 5 - FortiAnalyzer 7.6 Analyst
- NSE5_SSE_AD-7.6 - Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator
- FCP_FCT_AD-7.4 - Fortinet NSE 6 - FortiClient EMS 7.4 Administrator
- NSE5_FSW_AD-7.6 - Fortinet NSE 5 - FortiSwitch 7.6 Administrator
- FCP_FWF_AD-7.4 - FCP - Secure Wireless LAN 7.4 Administrator
- NSE6_SDW_AD-7.6 - Fortinet NSE 6 - SD-WAN 7.6 Enterprise Administrator
- FCSS_SASE_AD-25 - FCSS - FortiSASE 25 Administrator
- NSE7_SSE_AD-25 - Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator
- FCP_FWB_AD-7.4 - FCP - FortiWeb 7.4 Administrator
- FCP_FSM_AN-7.2 - FCP - FortiSIEM 7.2 Analyst
- NSE7_SOC_AR-7.6 - Fortinet NSE 7 - Security Operations 7.6 Architect
- FCSS_CDS_AR-7.6 - FCSS - Public Cloud Security 7.6 Architect
- NSE5_FNC_AD-7.6 - Fortinet NSE 5 - FortiNAC-F 7.6 Administrator
- NSE6_OTS_AR-7.6 - Fortinet NSE 6 - OT Security 7.6 Architect
- NSE6_FSR-7.3 - Fortinet NSE 6 - FortiSOAR 7.3 Administrator
- FCP_FML_AD-7.4 - FCP - FortiMail 7.4 Administrator
- NSE4_FGT-7.0 - Fortinet NSE 4 - FortiOS 7.0
- FCSS_EFW_AD-7.4 - FCSS - Enterprise Firewall 7.4 Administrator
- FCSS_SDW_AR-7.6 - FCSS - SD-WAN 7.6 Architect
- NSE6_FSW-7.2 - Fortinet NSE 6 - FortiSwitch 7.2
- FCP_FGT_AD-7.4 - FCP - FortiGate 7.4 Administrator
- NSE6_FWF-6.4 - Fortinet NSE 6 - Secure Wireless LAN 6.4
- NSE6_EDR_AD-7.0 - Fortinet NSE 6 - FortiEDR 7.0 Administrator
- NSE5_FMG-7.2 - Fortinet NSE 5 - FortiManager 7.2
- FCSS_SDW_AR-7.4 - FCSS - SD-WAN 7.4 Architect
- FCP_FCT_AD-7.2 - FCP - Forti Client EMS 7.2 Administrator
- NSE7_OTS-7.2 - Fortinet NSE 7 - OT Security 7.2
- FCSS_NST_SE-7.4 - FCSS - Network Security 7.4 Support Engineer
- FCP_FAZ_AN-7.4 - FCP - FortiAnalyzer 7.4 Analyst
- NSE4_FGT-6.4 - Fortinet NSE 4 - FortiOS 6.4
A Complete Guide to Fortinet FCP_FGT_AD-7.6 Certification Success
The Fortinet FCP_FGT_AD-7.6 exam, officially known as the Fortinet Certified Professional — FortiGate Administrator exam, is one of the most respected and sought-after credentials in the network security industry today. It validates your ability to deploy, manage, and troubleshoot FortiGate next-generation firewalls running FortiOS 7.6. For anyone working in network security administration or planning to build a career in cybersecurity infrastructure, this certification carries genuine weight with employers across every major industry sector.
Earning this credential tells the world that you are not just familiar with Fortinet products in a surface-level way. It demonstrates that you can handle real-world administrative tasks, configure complex security policies, manage VPN tunnels, implement antivirus and web filtering, and respond to network threats effectively. Organizations running Fortinet infrastructure actively look for professionals holding this certification because it reduces the time and cost of onboarding and ensures consistent quality in their security operations.
Breaking Down the Exam Domains and What Each Section Truly Tests
The FCP_FGT_AD-7.6 exam covers a wide range of technical domains, and understanding their scope before you begin studying is essential for building an efficient preparation strategy. The exam tests candidates on system configuration and initial setup, firewall policy management, routing protocols, network address translation, SSL and IPsec VPN configuration, security profiles including antivirus and intrusion prevention systems, web filtering, application control, authentication mechanisms, logging and monitoring, and high availability configurations.
Each of these domains requires not just theoretical knowledge but also hands-on understanding. You cannot simply memorize definitions and expect to pass. Fortinet designs its exams to evaluate whether candidates can apply their knowledge in realistic scenarios. Questions are often scenario-based, requiring you to identify the correct configuration steps or troubleshoot a described problem. This makes practical lab experience an absolutely non-negotiable part of your preparation journey rather than an optional supplement.
Setting Up a Realistic and Structured Study Timeline Before You Register
One of the biggest mistakes candidates make when approaching the FCP_FGT_AD-7.6 exam is registering without first establishing a clear and realistic study timeline. Depending on your existing familiarity with Fortinet products and network security concepts in general, your preparation window should range from six weeks at minimum to three months for those newer to the platform.
Begin by honestly assessing your current skill level. If you have worked with FortiGate firewalls in a professional environment for at least a year, your timeline can be compressed. If you are transitioning from another vendor's platform or coming from a purely theoretical background, give yourself additional weeks to build foundational comfort with the FortiGate interface and its unique configuration logic. Create a weekly study plan that dedicates specific days to specific domains, leaving the final two weeks exclusively for review, practice exams, and lab reinforcement.
Choosing the Right Study Resources That Actually Align With the Exam Objectives
The quality of your study materials directly affects the quality of your preparation. Fortinet provides official training courses, and the NSE training portal at training.fortinet.com is your primary starting point. The FortiGate Administrator course available through this portal is specifically designed to cover the exam objectives and is frequently updated to reflect the current FortiOS version being tested.
Beyond official Fortinet training, you should explore the FortiOS 7.6 Administration Guide, which is freely available and covers every feature and configuration option in remarkable depth. This document is not light reading, but investing time in the sections most heavily weighted in the exam will give you a significant advantage. Supplement these with community resources such as the Fortinet forums, Reddit communities focused on network security, and YouTube channels run by certified Fortinet professionals who walk through configurations visually.
Building Hands-On Lab Skills With FortiGate Without Spending a Fortune
Practical experience is the single most differentiating factor between candidates who pass on their first attempt and those who do not. The good news is that you do not need expensive physical hardware to build meaningful lab skills. Fortinet offers a free virtual machine version of FortiGate called FortiGate-VM, which you can run on platforms like VMware Workstation, VirtualBox, or even on cloud providers with a trial license.
Setting up a basic lab environment with a FortiGate-VM, a few virtual client machines, and a simulated internet segment will allow you to practice virtually every exam topic. Configure firewall policies from scratch. Set up a site-to-site IPsec VPN between two virtual FortiGate instances. Implement web filtering profiles and apply them to different user groups. Practice creating security fabric connections and reviewing logs in FortiView. Each of these hands-on activities reinforces the conceptual knowledge from your reading and builds the muscle memory that carries you through scenario-based exam questions.
Mastering Firewall Policy Configuration and the Logic Behind Traffic Flow
Firewall policy configuration is one of the most heavily tested areas in the FCP_FGT_AD-7.6 exam, and it deserves focused attention in your study plan. Understanding how FortiGate processes traffic through its policy table, from top to bottom, matching the first applicable policy, is fundamental. Many exam questions are built around this logic, asking candidates to predict what happens when specific traffic hits a firewall with a given policy configuration.
Practice creating policies with different source and destination interfaces, address objects, service objects, and action types. Understand the difference between accepting traffic with security profiles applied versus accepting traffic without inspection. Learn how to use policy-based routing when the standard routing table does not serve specific traffic requirements. Explore the use of virtual IPs for destination NAT and IP pools for source NAT, as these topics appear consistently across exam iterations and require clear conceptual understanding combined with practical configuration experience.
Navigating VPN Configurations With Confidence Across Both IPsec and SSL Options
VPN configuration is another domain where candidates frequently struggle, not because the concepts are inherently difficult, but because the number of parameters involved can feel overwhelming without proper structure. The FCP_FGT_AD-7.6 exam tests both IPsec VPN and SSL VPN, and you need to be comfortable with both in policy-based and route-based implementations.
For IPsec VPN, focus on understanding Phase 1 and Phase 2 parameters, the role of proposals and encryption algorithms, the difference between main mode and aggressive mode, and how to troubleshoot connectivity issues using the FortiGate diagnostics tools. For SSL VPN, practice configuring both web mode and tunnel mode, setting up realms, applying firewall policies to control SSL VPN traffic, and configuring split tunneling. The exam will test your ability to identify configuration errors in described scenarios, so understanding why certain configurations fail is just as important as knowing how to set them up correctly.
Understanding Security Profiles and How They Integrate Into Traffic Inspection
Security profiles form a critical layer of the FortiGate's defense capabilities, and the exam tests your ability to configure and apply antivirus profiles, web filter profiles, DNS filter profiles, application control profiles, and intrusion prevention system profiles correctly. Understanding how these profiles work together within a firewall policy, and how traffic inspection works in both flow-based and proxy-based modes, is essential knowledge for the exam.
Pay particular attention to the difference between flow-based and proxy-based inspection modes, as this is a conceptually rich area that generates many exam questions. Flow-based inspection processes traffic in a streaming fashion with lower latency, while proxy-based inspection buffers content entirely before scanning, allowing more thorough analysis at the cost of additional delay. Understanding when to use each mode, and how each mode affects the behavior of individual security profiles, will help you answer configuration and troubleshooting questions accurately.
Exploring Authentication Methods and User Identity Integration on FortiGate
Authentication is a topic that bridges technical configuration with organizational security policy, and the FCP_FGT_AD-7.6 exam tests it at a meaningful depth. You need to understand local user accounts, user groups, LDAP integration with Active Directory, RADIUS authentication, and the use of FortiAuthenticator in environments that require more sophisticated identity management.
Practice configuring LDAP servers within the FortiGate management interface and linking them to firewall policies that enforce identity-based access control. Understand how captive portals work for guest user authentication and how to configure two-factor authentication for both management access and VPN users. The exam may present scenarios where a specific authentication method is malfunctioning and ask you to identify the most likely cause, so your troubleshooting instincts in this area need to be sharp.
High Availability Architecture and What Candidates Frequently Overlook in This Domain
High availability is a topic that many candidates underestimate in their preparation, often spending less time on it because it feels abstract compared to more tangible topics like policy configuration or VPN setup. However, the FCP_FGT_AD-7.6 exam includes meaningful coverage of HA concepts, and understanding them well can be the difference between a passing and failing score.
Study the difference between active-passive and active-active high availability modes, understanding the traffic distribution implications of each. Learn how session synchronization works between cluster members and what happens during a failover event. Understand the role of the heartbeat interface, how cluster members communicate health status to each other, and how to configure HA priority settings to control which device becomes the primary unit. Practice interpreting HA status output from both the GUI and the command line interface, as the exam may present CLI output and ask you to draw conclusions from it.
Logging, Monitoring, and FortiView as Tools for Operational Visibility
Effective security administration requires not just correct configuration but also the ability to see what is happening in your environment. The FCP_FGT_AD-7.6 exam tests your knowledge of FortiGate's logging capabilities, including log types, log severity levels, log destinations, and the use of FortiView for real-time and historical traffic analysis.
Understand the difference between local logging, logging to FortiAnalyzer, and logging to FortiCloud. Know how to configure logging per firewall policy and per security profile. Practice using FortiView to analyze top sources, destinations, applications, and threats in a lab environment. The exam will likely present scenarios where you need to identify what log information would help diagnose a described problem, or where you need to configure logging appropriately to meet a described operational requirement.
Using Practice Exams Strategically Rather Than Just Accumulating Question Counts
Practice exams are a valuable preparation tool, but only when used with the right mindset and strategy. Many candidates make the mistake of taking practice tests repeatedly without analyzing their wrong answers in depth, treating the process as a numbers game rather than a diagnostic exercise. This approach produces diminishing returns and gives a false sense of readiness.
After each practice exam session, review every question you answered incorrectly and understand precisely why your chosen answer was wrong and why the correct answer is right. If you cannot explain the reasoning behind a correct answer in your own words, return to your study materials and spend more time on that topic before attempting more practice questions. Use practice exams to identify weak domains, then address those domains through targeted study and hands-on lab work before testing yourself again. This feedback-driven approach accelerates genuine comprehension far more effectively than volume-based repetition.
Preparing Mentally and Logistically for Exam Day Itself
The technical preparation phase is where most candidates focus, but the logistical and psychological dimensions of exam day deserve equal attention. The FCP_FGT_AD-7.6 exam is delivered through Pearson VUE, and you can take it either at an authorized testing center or through an online proctored format. Both options have their advantages, and choosing the one that best suits your personal testing environment is worth considering carefully.
If you choose the online proctored format, ensure your testing space is clean, quiet, and free of unauthorized materials well before the scheduled exam time. Test your computer hardware, webcam, and internet connection thoroughly at least a day in advance. On exam day itself, arrive at the testing center or log into the proctoring system early to avoid unnecessary stress. Maintain a steady pace during the exam, answering questions you feel confident about first and flagging others for review. Avoid spending disproportionate time on any single question, as the exam is time-limited and every question carries weight.
Leveraging the Fortinet Community and Study Groups for Deeper Understanding
Studying in isolation is effective for some people but limiting for others. The Fortinet community offers genuine value for candidates preparing for the FCP_FGT_AD-7.6 exam, particularly through forums where experienced administrators discuss real-world configurations, share troubleshooting insights, and occasionally discuss exam experiences within the limits of non-disclosure agreements.
Joining study groups, whether formal or informal, can expose you to questions and perspectives you would not encounter studying alone. Explaining concepts to others is also one of the most powerful learning techniques available, because teaching forces you to identify gaps in your own understanding. If you can explain how FortiGate processes a firewall policy, how a site-to-site IPsec VPN negotiation works, or how HA failover happens in active-passive mode clearly enough for a fellow candidate to understand, you have reached the level of comprehension the exam rewards.
Continuing Your Certification Journey After Passing the FCP_FGT_AD-7.6 Exam
Passing the FCP_FGT_AD-7.6 exam is a meaningful achievement, but it also opens the door to a broader certification journey within the Fortinet ecosystem. The Fortinet Certified Professional designation sits within the larger Fortinet NSE certification framework, and many professionals use it as a stepping stone toward more advanced credentials such as the NSE 7 level specialist exams or the NSE 8 expert-level certification.
Beyond formal certifications, the knowledge and habits you build during your FCP_FGT_AD-7.6 preparation will continue paying dividends in your daily work. The discipline of understanding traffic flow logic, the attention to detail required in VPN configuration, and the analytical thinking developed through troubleshooting practice all translate directly into higher quality security administration in real environments. Let your certification success be the beginning of ongoing professional development rather than a destination in itself.
Conclusion
The Fortinet FCP_FGT_AD-7.6 certification is a rigorous but genuinely rewarding credential for network security professionals. Success requires a balanced approach that combines structured theoretical study, consistent hands-on lab practice, strategic use of practice exams, and honest self-assessment throughout the preparation process. By understanding the exam domains deeply, building real configuration skills in a virtual lab environment, and approaching each study session with clear objectives, you give yourself the strongest possible foundation for passing on your first attempt. The effort you invest in this certification not only earns you a respected credential but also sharpens the practical skills that make you a more capable and confident security administrator every single day.