Exam Code: SSE-Engineer
Exam Name: Palo Alto Networks Security Service Edge Engineer
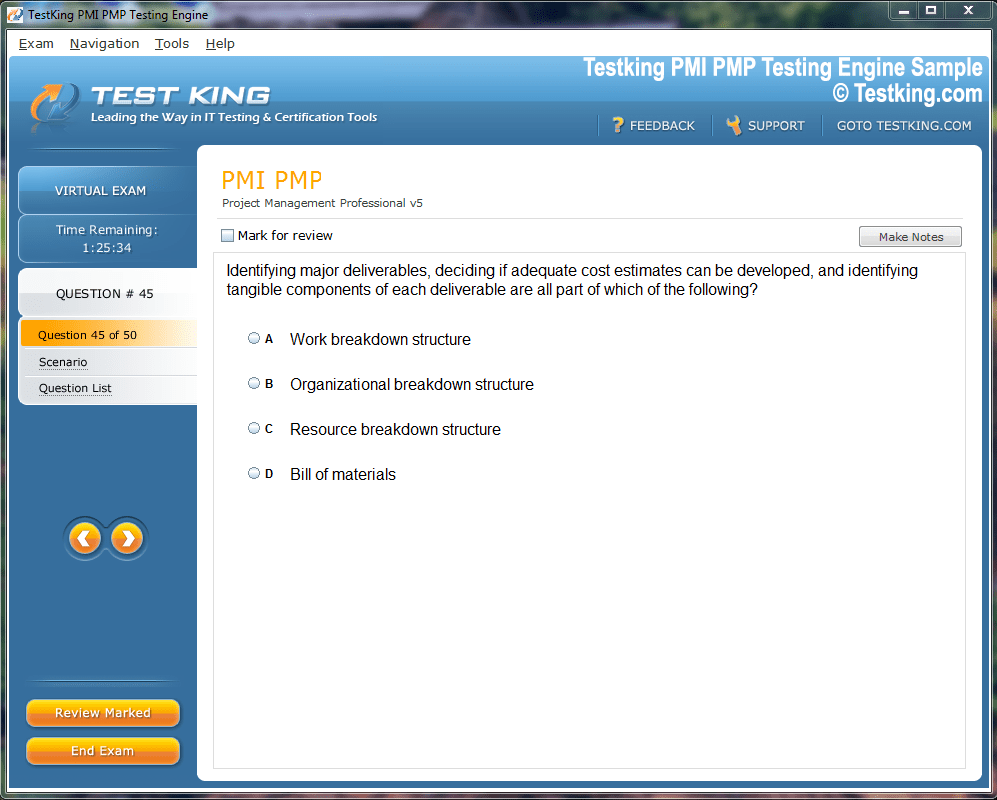
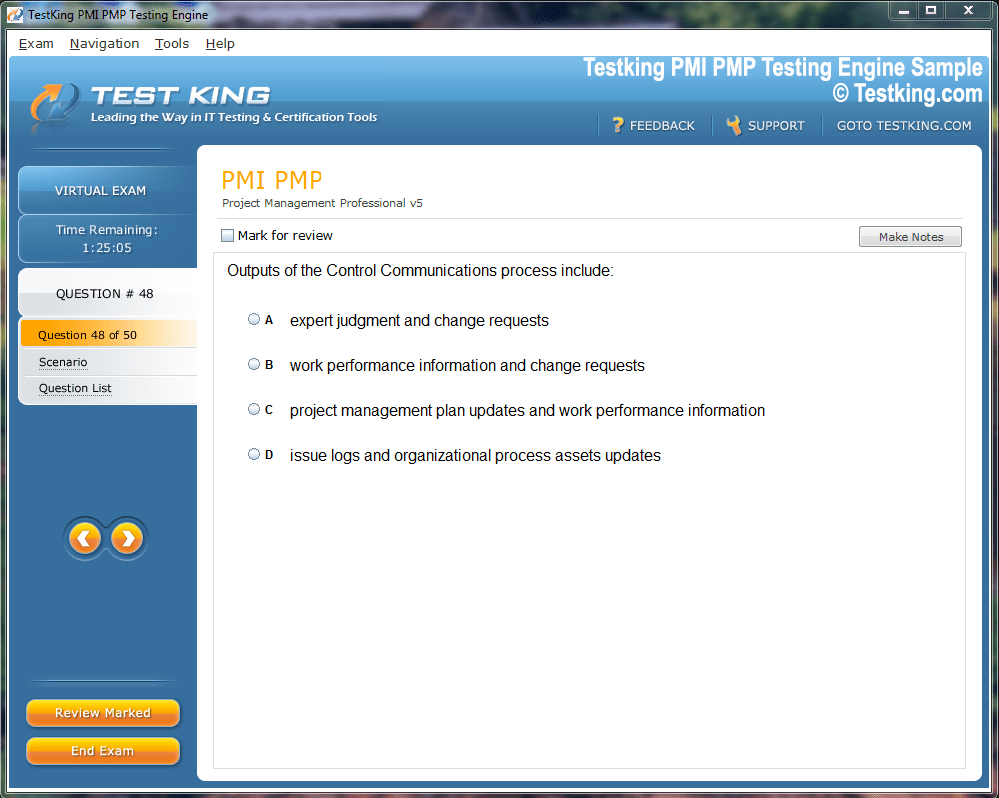
Product Screenshots
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our SSE-Engineer testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.
Top Palo Alto Networks Exams
- NGFW-Engineer - Palo Alto Networks Certified Next-Generation Firewall Engineer
- NetSec-Pro - Palo Alto Networks Certified Network Security Professional
- SecOps-Pro - Palo Alto Networks Security Operations Professional
- NetSec-Analyst - Palo Alto Networks Certified Network Security Analyst
- SSE-Engineer - Palo Alto Networks Security Service Edge Engineer
- XSIAM-Engineer - Palo Alto Networks XSIAM Engineer
- NetSec-Architect - Palo Alto Networks Network Security Architect
- XSIAM-Analyst - Palo Alto Networks Certified XSIAM Analyst
- SD-WAN-Engineer - Palo Alto Networks SD-WAN Engineer
- PCNSE - Palo Alto Networks Certified Network Security Engineer
- XSOAR-Engineer - Palo Alto Networks XSOAR Engineer
- PCNSA - Palo Alto Networks Certified Network Security Administrator
- PCCP - Palo Alto Networks Cybersecurity Practitioner
- PSE Strata - Palo Alto Networks System Engineer Professional - Strata
- PCDRA - Palo Alto Networks Certified Detection and Remediation Analyst
- PSE-SASE - Palo Alto Networks System Engineer Professional - SASE
- NetSec-Generalist - Palo Alto Networks - Network Security Generalist
- PCCSE - Prisma Certified Cloud Security Engineer
- Apprentice - Palo Alto Networks Cybersecurity Apprentice
Exploring Modern Security Challenges with Palo Alto Networks SSE-Engineer
The Security Service Edge represents a transformative approach to network security that converges comprehensive security capabilities delivered from the cloud. Organizations face increasingly distributed workforces, multi-cloud environments, and sophisticated threat actors that traditional perimeter-based security models cannot adequately address. The SSE framework consolidates services including secure web gateways, cloud access security brokers, zero trust network access, and data loss prevention into a unified cloud-native architecture. Palo Alto Networks positions SSE as a critical component of their Secure Access Service Edge vision, enabling organizations to protect users regardless of their location or the applications they access. The SSE-Engineer certification validates expertise in designing, implementing, and managing these integrated security services. Professionals pursuing this credential develop proficiency in modern container and VM architectures that underpin cloud-native security deployments and distributed application protection strategies.
Examining Zero Trust Network Access Principles
Zero trust architecture fundamentally challenges traditional network security assumptions by eliminating implicit trust based on network location. Every access request requires authentication, authorization, and continuous verification regardless of whether the request originates inside or outside the traditional network perimeter. This principle aligns with modern work patterns where employees access corporate resources from diverse locations using various devices. Palo Alto Networks implements zero trust through Prisma Access, which provides granular application access controls based on user identity, device posture, and contextual factors. SSE engineers configure policies that enforce least-privilege access while maintaining user productivity and experience. Organizations transitioning to zero trust models benefit from professionals who understand both security requirements and operational realities, similar to how VMware certification journeys require balancing technical depth with practical implementation knowledge.
Deploying Secure Web Gateway Capabilities
Secure web gateways provide comprehensive URL filtering, malware protection, and data loss prevention for web traffic regardless of user location. Traditional on-premises web proxies struggle to protect remote workers effectively, creating security gaps and performance bottlenecks. Cloud-delivered SWG services inspect all web traffic using distributed points of presence that minimize latency while maximizing security coverage. Palo Alto Networks integrates advanced threat prevention, SSL/TLS decryption, and granular policy controls within their SWG offering. Engineers configure category-based filtering, custom URL lists, and threat intelligence feeds that block access to malicious or inappropriate sites. The platform supports both inline and API-based deployment models to accommodate diverse network architectures. Professionals implementing these solutions draw on experiences similar to those documented in VMware Cloud Foundation deployments where architectural decisions significantly impact performance and security outcomes.
Implementing Cloud Access Security Broker Functions
CASB technology provides visibility and control over cloud application usage, protecting sensitive data stored in sanctioned and unsanctioned SaaS applications. Organizations struggle to maintain security governance as employees adopt cloud services outside IT oversight. CASB solutions discover shadow IT, enforce data security policies, and detect anomalous user behavior across cloud applications. The Palo Alto Networks CASB integrates with major SaaS platforms to provide inline and out-of-band security controls. Engineers configure data loss prevention policies that prevent sensitive information from being uploaded to unapproved services or shared inappropriately. User and entity behavior analytics identify compromised accounts or insider threats based on unusual access patterns. Understanding how cookies function in web privacy helps engineers appreciate the data collection mechanisms they must secure within cloud applications.
Architecting Data Loss Prevention Strategies
Data loss prevention capabilities prevent sensitive information from leaving organizational control through various channels including email, web uploads, and cloud storage. Effective DLP requires accurate data classification, comprehensive policy coverage, and minimal false positives that could disrupt legitimate business activities. Modern DLP extends beyond traditional network boundaries to protect data wherever it travels. SSE engineers configure content inspection patterns, contextual analysis rules, and machine learning-based classification to identify sensitive data automatically. Policies can block, quarantine, or encrypt data based on classification and intended destination. Integration with cloud applications ensures consistent protection regardless of how users access corporate resources. The systematic approach to blue-green deployment strategies parallels how DLP policies must be carefully tested and rolled out to avoid business disruption.
Configuring Advanced Threat Prevention Mechanisms
Advanced threat prevention combines signature-based detection, behavioral analysis, and machine learning to identify and block sophisticated attacks. Traditional antivirus solutions cannot detect zero-day threats or polymorphic malware that evades signature matching. Modern threat prevention requires inline inspection, sandboxing capabilities, and threat intelligence integration. Palo Alto Networks employs WildFire malware analysis to detonate suspicious files in a cloud-based sandbox environment and share threat intelligence across all customer deployments. Engineers configure file blocking policies, antivirus profiles, and anti-spyware settings that balance security and performance. DNS security features prevent communication with malicious domains used for command-and-control or data exfiltration. Understanding how DNS functions in internet communication provides essential context for implementing effective DNS-based security controls.
Managing User Identity and Authentication Integration
Identity-based security policies require integration with corporate identity providers including Active Directory, Azure AD, and other SAML-based authentication systems. User and group membership information enables granular access controls that adapt to organizational changes automatically. Multi-factor authentication adds critical protection against credential theft and phishing attacks. SSE engineers configure identity source connections, attribute mapping, and authentication policies that support diverse user populations including employees, contractors, and partners. Single sign-on integration improves user experience while maintaining security. Device posture assessment ensures only compliant endpoints can access sensitive resources. Professionals implementing these identity frameworks should develop expertise comparable to data privacy officers who must understand authentication, authorization, and audit requirements.
Establishing Security Policy Frameworks and Governance
Comprehensive security policies define acceptable use, access controls, and threat response across the SSE environment. Policy frameworks must balance security requirements with business enablement, avoiding overly restrictive controls that drive shadow IT adoption. Effective governance includes policy lifecycle management, regular reviews, and stakeholder engagement. Engineers organize policies using hierarchical structures that separate global defaults from location-specific or department-specific rules. Change control processes prevent unauthorized modifications and maintain audit trails for compliance purposes. Policy testing validates expected behavior before production deployment. The importance of data privacy in modern environments underscores why security policies must address both threat protection and privacy preservation.
Optimizing SSL/TLS Decryption and Inspection
Encrypted traffic inspection presents technical and policy challenges as most web traffic now uses HTTPS encryption. Malware and data exfiltration can hide within encrypted sessions, creating blind spots for security controls. SSL/TLS decryption enables inspection of encrypted traffic while raising privacy concerns that must be carefully managed. Palo Alto Networks supports flexible decryption policies that can exclude sensitive categories like healthcare or financial services based on organizational privacy requirements. Certificate management ensures trusted decryption without browser warnings or application compatibility issues. Performance optimization techniques including hardware acceleration maintain acceptable latency during decryption operations. Security teams implementing these capabilities draw on principles similar to secure coding practices where security must be balanced with functionality.
Integrating Threat Intelligence and Security Analytics
Threat intelligence enriches security decisions by providing context about emerging threats, attacker tactics, and indicators of compromise. External intelligence feeds combined with internal security telemetry create comprehensive threat awareness. Security analytics transform raw logs into actionable insights that prioritize investigation and response activities. The Palo Alto Networks platform consumes threat intelligence from multiple sources including WildFire, Unit 42 research, and third-party feeds. Engineers configure automated threat signatures, correlation rules, and reporting dashboards that highlight security trends. Machine learning algorithms identify anomalies that may indicate emerging threats or policy violations. Organizations managing operational technology environments face similar challenges integrating security intelligence across IT and OT domains.
Designing High Availability and Disaster Recovery
Business continuity requirements demand resilient SSE architectures that maintain security services during infrastructure failures or maintenance windows. High availability designs eliminate single points of failure through redundant components and automated failover mechanisms. Disaster recovery planning ensures rapid restoration of security services following major incidents. Cloud-delivered SSE services inherently provide geographic redundancy and elastic scalability that traditional on-premises solutions cannot match. Engineers configure active-active or active-passive architectures based on performance and cost requirements. Backup and restore procedures protect configuration data and security policies. Testing validates recovery procedures before actual disasters occur. Professionals preparing for ISO 27001 auditor responsibilities develop similar skills in assessing business continuity and disaster recovery controls.
Monitoring Performance Metrics and Capacity Planning
Effective SSE operations require continuous monitoring of performance indicators including latency, throughput, and resource utilization. Baseline metrics establish normal operating parameters against which anomalies can be detected. Capacity planning ensures infrastructure scales appropriately as user populations grow and traffic volumes increase. Palo Alto Networks provides comprehensive logging and monitoring capabilities through Panorama and cloud-delivered management services. Engineers configure alerting thresholds for performance degradation, license consumption, and security events requiring investigation. Trend analysis identifies growth patterns that inform infrastructure expansion decisions. The analytical approaches used in Python and R data analysis translate effectively to security metrics analysis and performance optimization.
Conducting Security Assessments and Risk Analysis
Regular security assessments evaluate SSE effectiveness against evolving threats and changing business requirements. Risk analysis identifies vulnerabilities, prioritizes remediation efforts, and demonstrates security investment value to executive stakeholders. Assessment methodologies include vulnerability scanning, penetration testing, and configuration reviews. Engineers perform policy audits to identify overly permissive rules, unused configurations, or inconsistent security controls. Compliance assessments validate adherence to regulatory requirements and industry frameworks. Gap analysis compares current state against security best practices and identifies improvement opportunities. Organizations embracing data-driven decision making apply similar analytical rigor to security investment prioritization.
Automating Security Operations and Orchestration
Security automation reduces manual effort, accelerates incident response, and improves consistency across security operations. Orchestration platforms integrate multiple security tools and automate complex workflows spanning detection, investigation, and remediation. API-driven automation enables integration with broader IT service management and DevOps processes. Palo Alto Networks supports automation through comprehensive APIs, scripting interfaces, and integration with security orchestration platforms. Engineers develop automated playbooks for common scenarios like quarantining compromised devices, blocking malicious indicators, or updating security policies. Infrastructure-as-code practices apply security configurations consistently across environments. The strategic use of AI in budgeting processes demonstrates similar benefits of automation in complex decision-making domains.
Troubleshooting Common Implementation Challenges
SSE deployments encounter various technical challenges including application compatibility issues, performance bottlenecks, and policy conflicts. Effective troubleshooting requires systematic approaches that isolate root causes and validate solutions. Common issues include certificate trust problems, routing asymmetry, and authentication failures. Engineers utilize packet captures, detailed logging, and vendor support resources to diagnose complex problems. Documentation of known issues and resolutions builds organizational knowledge and reduces resolution times for recurring problems. Escalation procedures ensure critical issues receive appropriate attention and resources. Skills in transforming raw data to insights help engineers analyze security logs and performance data during troubleshooting activities.
Addressing Compliance and Regulatory Requirements
Organizations must align SSE implementations with various regulatory frameworks including GDPR, HIPAA, PCI DSS, and industry-specific mandates. Compliance requirements influence architecture decisions, data handling practices, and audit capabilities. Documentation demonstrates security controls and facilitates regulatory examinations. Engineers configure data residency controls, encryption requirements, and audit logging that satisfy compliance obligations. Privacy protection features prevent inadvertent exposure of personal information during security operations. Regular compliance assessments identify gaps requiring remediation before external audits. The systematic approach to sustainable supply chain management parallels how security compliance requires continuous monitoring and improvement.
Leveraging Reporting and Executive Communication
Security reporting translates technical metrics into business-relevant insights that inform executive decision-making and demonstrate program effectiveness. Executive dashboards highlight key risk indicators, incident trends, and security posture improvements. Detailed technical reports support security operations and incident investigation activities. Palo Alto Networks provides extensive reporting capabilities through Panorama and cloud-based analytics platforms. Engineers create custom reports addressing specific stakeholder needs including compliance auditors, business executives, and technical teams. Visualization techniques communicate complex security data effectively to non-technical audiences. The principles of effective Tableau reporting apply equally to security dashboards and executive presentations.
Pursuing Professional Development and Certification Preparation
The SSE-Engineer certification validates comprehensive knowledge of Palo Alto Networks SSE technologies and best practices. Preparation requires hands-on experience, formal training, and dedicated study of platform capabilities and configuration procedures. Practice examinations familiarize candidates with question formats and identify knowledge gaps requiring additional focus. Continuous learning maintains relevance as Palo Alto Networks introduces new features, threat actors evolve tactics, and security best practices advance. Professional communities, vendor events, and industry conferences provide networking opportunities and knowledge sharing. Career advancement follows demonstrated expertise through certifications, successful implementations, and thought leadership. Understanding Microsoft Azure certification paths illustrates how strategic credential selection accelerates professional growth.
Developing Hands-On Laboratory Experience
Practical experience in configuring and managing SSE components solidifies theoretical knowledge and builds troubleshooting skills. Laboratory environments enable experimentation with features and testing of configurations without impacting production systems. Scenario-based learning simulates real-world challenges that engineers encounter during implementations. Palo Alto Networks provides trial environments, demonstration platforms, and partner access to sandbox systems for learning purposes. Engineers should build home labs or leverage cloud resources to gain hands-on experience across the full SSE stack. Documented lab exercises reinforce learning and create reference materials for future use. The journey toward Microsoft certification excellence demonstrates similar benefits of combining theoretical knowledge with practical application.
Securing Organizational Support and Investment
SSE implementations require executive sponsorship, budget allocation, and organizational change management. Security leaders must articulate business value, quantify risk reduction, and demonstrate return on security investment. Building coalitions across IT, business units, and executive leadership ensures implementation success. Professionals seeking employer support for certification should demonstrate how enhanced skills benefit organizational security posture and operational capabilities. Business cases connect certification investment to improved incident response, reduced security incidents, or enhanced compliance capabilities. The approach to requesting Microsoft certification sponsorship provides templates applicable to Palo Alto Networks certification pursuits.
Implementing Granular Application Control Policies
Application control capabilities enable organizations to manage which applications users can access while enforcing appropriate usage policies. Traditional port-based firewalls cannot distinguish between applications sharing common protocols or ports. Modern application identification uses multiple techniques including protocol decoding, behavioral analysis, and SSL inspection to accurately classify traffic. Palo Alto Networks App-ID technology identifies thousands of applications regardless of port, protocol, or evasive tactics. Engineers create policies based on application characteristics, risk levels, and business requirements rather than simple allow or deny decisions. Bandwidth management ensures critical business applications receive priority over recreational traffic. Organizations developing comprehensive security strategies may explore Lenovo infrastructure solutions that integrate with advanced security platforms for end-to-end protection.
Enforcing Mobile Device Security and Management
Mobile devices present unique security challenges due to diverse operating systems, personal device usage, and constantly changing locations. Mobile threat defense capabilities protect against device-level threats, malicious applications, and network-based attacks targeting smartphones and tablets. Integration with mobile device management platforms enforces compliance requirements and device posture checks.SSE platforms assess device security status including operating system version, encryption status, and presence of security software before granting access to corporate resources. Per-app VPN capabilities protect corporate data without affecting personal applications on BYOD devices. Engineers configure policies that adapt to device type, ownership model, and security posture dynamically. Professionals seeking broader infrastructure expertise might pursue Linux Foundation certifications that complement security specializations.
Protecting Branch Office and Remote Locations
Branch offices require security services equivalent to headquarters while accommodating limited local IT resources and infrastructure. Traditional approaches of backhauling traffic to central data centers create latency and bandwidth constraints. SSE architectures deliver security directly from the cloud, eliminating traffic tromboning and improving application performance. Palo Alto Networks supports various deployment models including direct internet access from branches, SD-WAN integration, and hybrid approaches combining cloud and on-premises security. Engineers configure location-specific policies while maintaining centralized management and visibility. Bandwidth optimization techniques including caching and compression reduce WAN utilization. Contact center environments can leverage Avaya communication certifications alongside security expertise for comprehensive unified communications security.
Securing Internet of Things and Operational Technology
IoT devices and operational technology systems introduce security risks through weak authentication, unpatched vulnerabilities, and protocols designed for reliability rather than security. Visibility into IoT device inventory, behavior, and communications represents the first step toward securing these assets. Segmentation isolates IoT devices from corporate networks and limits potential attack propagation. SSE platforms identify IoT devices through fingerprinting techniques and create appropriate security policies based on device type and expected behavior. Anomaly detection identifies compromised IoT devices communicating with command-and-control infrastructure or exhibiting unusual traffic patterns. Engineers balance security controls with operational requirements that may limit device management capabilities. Industrial control systems professionals might pursue specialized Avaya certifications addressing communications infrastructure security.
Managing Multi-Cloud Security Posture
Organizations adopting multi-cloud strategies distribute workloads across AWS, Azure, Google Cloud, and other providers to optimize cost, performance, and resilience. Each cloud platform implements security differently, creating complexity and potential gaps in protection. Consistent security policies across environments prevent misconfigurations and ensure comprehensive threat protection. Palo Alto Networks Prisma Cloud provides unified visibility and security across multi-cloud deployments. Engineers configure cloud-native security controls, monitor compliance with security frameworks, and detect misconfigurations that could expose sensitive data. Integration with cloud provider APIs enables automated remediation of security findings. Organizations standardizing on specific platforms may explore Avaya networking paths for complementary infrastructure expertise.
Orchestrating Incident Response and Investigation
Effective incident response requires coordinated activities across detection, analysis, containment, eradication, and recovery phases. Security orchestration platforms automate response workflows and integrate disparate security tools. Forensic investigation capabilities preserve evidence, reconstruct attack timelines, and identify root causes. SSE platforms provide detailed logging and packet capture capabilities that support incident investigation. Engineers configure log forwarding to SIEM platforms, define incident severity classifications, and establish escalation procedures. Playbooks standardize response procedures for common incident types. Post-incident reviews identify lessons learned and drive security improvements. Professionals developing response capabilities might pursue Avaya collaboration credentials that enhance team coordination during security incidents.
Applying Microsegmentation and Network Isolation
Microsegmentation divides networks into smaller zones with granular security controls between segments. Traditional flat networks allow lateral movement once attackers compromise initial access. Zero trust microsegmentation limits blast radius by restricting communications to only explicitly allowed traffic flows. Engineers define segmentation strategies based on application dependencies, data sensitivity, and user access requirements. Identity-based segmentation adapts to users and devices moving between network segments. Application dependency mapping ensures segmentation policies do not disrupt legitimate business communications. Organizations implementing advanced segmentation may reference Avaya platform expertise for integrated communication and security architectures.
Detecting Insider Threats and Anomalous Behavior
Insider threats including malicious employees, compromised accounts, and negligent users pose significant risks that traditional perimeter defenses cannot address. User and entity behavior analytics establish baseline activity patterns and detect anomalies indicating potential threats. Detecting insider threats requires balancing security monitoring with employee privacy expectations. SSE platforms analyze user behavior including access patterns, data transfers, and application usage to identify suspicious activities. Machine learning algorithms adapt baselines to accommodate legitimate behavior changes while flagging genuine anomalies. Integration with HR systems enables correlation of security events with employment status changes. Security professionals might explore Avaya contact center credentials to understand communication patterns requiring monitoring.
Securing Software-as-a-Service Application Access
SaaS applications store critical business data outside traditional network boundaries, requiring new security approaches beyond simple authentication. API-based CASB integration provides visibility into SaaS usage, enforces data security policies, and detects account compromises. Inline CASB deployment enables real-time threat prevention and data loss prevention. Engineers configure integrations with major SaaS platforms including Microsoft 365, Salesforce, Box, and Google Workspace. Shadow IT discovery identifies unsanctioned cloud services requiring governance. OAuth application analysis detects risky third-party applications with excessive permissions. Organizations standardizing on specific platforms may use Avaya deployment certifications for comprehensive application ecosystem security.
Implementing Secure Access for Third-Party Users
Partner access, vendor relationships, and contractor engagements require providing external users with limited access to specific resources without compromising security. Third-party access presents heightened risk due to reduced control over user devices and security practices. Time-bound access and least-privilege principles minimize exposure. SSE platforms support guest user workflows, sponsor-based access approvals, and automated access revocation. Engineers configure separate authentication realms for external users and enforce stricter security policies. Session monitoring detects inappropriate activities by third-party users. Access reviews ensure permissions remain appropriate as business relationships evolve. Infrastructure designers might reference BICSI RCDD standards when planning comprehensive access control systems.
Defending Against Phishing and Social Engineering
Phishing attacks remain among the most successful initial access vectors despite widespread awareness training. URL filtering blocks access to known phishing sites, while advanced analysis detects newly created domains used in campaigns. Email security integration prevents phishing messages from reaching user inboxes. Credential phishing detection identifies fake login pages attempting to harvest usernames and passwords. Multi-factor authentication provides critical protection when credentials are compromised. User education programs combined with simulated phishing exercises improve human defenses against social engineering. Security teams might pursue CompTIA Linux+ credentials to strengthen their infrastructure security foundations supporting anti-phishing controls.
Addressing Shadow IT and Unsanctioned Applications
Employees adopt cloud services to improve productivity without IT approval, creating shadow IT that bypasses security controls. Cloud application discovery identifies all cloud services accessed from the corporate network. Risk scoring evaluates services based on security practices, compliance certifications, and business reputation. Engineers configure policies that block high-risk unsanctioned services while allowing approved alternatives with appropriate security controls. User notifications explain why certain services are blocked and direct them to sanctioned options. Engagement with business units identifies legitimate needs driving shadow IT adoption. Network professionals developing comprehensive security skills CompTIA Network+ certification as a foundation.
Preventing Data Exfiltration and Information Theft
Data exfiltration attempts exploit various channels including cloud storage, email, web uploads, and removable media. DLP policies identify sensitive data through content inspection, contextual analysis, and user behavior patterns. Prevention actions range from user warnings through complete blocking based on data sensitivity and business risk. Engineers configure fingerprinting for structured data, pattern matching for unstructured content, and machine learning classification for complex scenarios. Integration with data classification systems ensures consistent policy enforcement. Incident workflows enable security reviews of blocked transactions before allowing exceptions. Penetration testers CompTIA PenTest+ credentials develop skills in identifying and exploiting data exfiltration vectors.
Securing DevOps and Continuous Integration Pipelines
DevOps practices accelerate software delivery but can introduce security vulnerabilities through rapid changes and automated deployments. Securing CI/CD pipelines requires integrating security scanning, access controls, and configuration validation throughout development workflows. Container security addresses unique risks associated with containerized application deployments. SSE platforms integrate with DevOps tools to enforce security policies on cloud resources created through infrastructure-as-code. Engineers configure API security to protect microservices communications and implement secrets management for credentials and encryption keys. Security testing shifts left into development phases rather than occurring only before production deployment. Project managers coordinating security initiatives CompTIA Project+ certification to enhance delivery capabilities.
Maintaining Security During Digital Transformation
Digital transformation initiatives fundamentally change how organizations operate, often introducing new security challenges faster than traditional security programs can adapt. Cloud migration, application modernization, and workforce mobility require security architectures that enable rather than impede business objectives. Security must become embedded in transformation initiatives from inception. Engineers participate in architecture reviews, provide security requirements for new initiatives, and design controls that support business goals. Agile security approaches deliver incremental protection aligned with transformation timelines. Metrics demonstrate security program contribution to business outcomes rather than simply reporting vulnerabilities. Professionals building comprehensive security expertise should have CompTIA Security+ certification as a foundational credential.
Evaluating Emerging Threats and Attack Vectors
Threat landscapes evolve continuously as attackers develop new techniques and exploit emerging technologies. SSE engineers must stay informed about threat trends including ransomware variations, supply chain attacks, and cloud-specific threats. Threat intelligence integration ensures security controls adapt to emerging risks. Engineers participate in information sharing communities, monitor vendor threat advisories, and analyze attack campaigns targeting their industry. Proactive threat hunting identifies indicators of compromise before automated defenses trigger alerts. Red team exercises validate detection and response capabilities against realistic attack scenarios. Understanding emerging threats informs security roadmap priorities and technology evaluations.
Advancing Career Opportunities Through SSE Expertise
The SSE-Engineer certification differentiates security professionals in competitive job markets by validating specialized expertise in cloud-delivered security architectures. Organizations worldwide seek qualified engineers capable of designing, implementing, and operating modern security platforms. Career paths span consulting firms, enterprise security teams, managed security service providers, and vendor technical organizations. Certified professionals command premium compensation reflecting their specialized knowledge and practical implementation experience. Career progression leads to senior engineering roles, security architecture positions, and leadership responsibilities. Continuous learning maintains relevance as security technologies and threat landscapes evolve. Professionals pursuing diverse credentials might explore fundraising certification paths that demonstrate breadth beyond technical specializations.
Mastering Advanced Troubleshooting Methodologies
Complex SSE environments require systematic troubleshooting approaches that isolate issues across cloud services, network connectivity, and endpoint configurations. Advanced diagnostic techniques include packet analysis, API debugging, and correlation of events across multiple log sources. Vendor support escalation procedures ensure critical issues receive appropriate attention and resources. Engineers develop troubleshooting playbooks documenting common scenarios and resolution procedures. Root cause analysis prevents recurring issues by addressing underlying problems rather than symptoms. Knowledge bases preserve institutional learning and reduce resolution times. Collaboration with vendor technical support and community forums expands troubleshooting capabilities. Security professionals might pursue Check Point administrator credentials to develop complementary troubleshooting skills across security platforms.
Implementing Security for Mergers and Acquisitions
Merger and acquisition activities create urgent security integration requirements as organizations combine networks, applications, and user populations. Due diligence security assessments identify risks in target companies before acquisition completion. Integration planning addresses identity consolidation, policy harmonization, and architectural standardization. SSE platforms facilitate rapid integration by providing cloud-delivered security for acquired entities without physical infrastructure deployment. Engineers configure separate administrative domains that later merge as organizational integration progresses. Access controls prevent unauthorized cross-company access during transition periods. Security standardization establishes consistent protection across the combined organization. Firewall specialists might reference Check Point CCSA certification when integrating perimeter security architectures.
Securing Remote Access for Privileged Users
Privileged users including administrators, developers, and third-party support personnel require elevated access that presents heightened security risks. Privileged access management solutions provide session recording, just-in-time provisioning, and credential vaulting. Integration with SSE platforms ensures comprehensive protection for privileged sessions. Engineers configure step-up authentication requiring additional verification for privileged access requests. Session monitoring detects suspicious activities by privileged users including unusual commands or access to sensitive resources. Time-bound access automatically revokes privileges after specified durations. Approval workflows enforce management oversight for privileged access grants. Advanced firewall administrators pursuing Check Point certification paths develop similar privileged access security expertise.
Defending Against Distributed Denial of Service Attacks
DDoS attacks overwhelm targeted systems with traffic volumes exceeding capacity, disrupting business operations and customer access. Cloud-delivered DDoS protection absorbs attack traffic before reaching target infrastructure. Volumetric attacks, protocol attacks, and application-layer attacks require different mitigation techniques. SSE platforms integrate DDoS protection that activates automatically when attack traffic is detected. Engineers configure traffic baselines, mitigation thresholds, and notification procedures. Scrubbing centers filter malicious traffic while allowing legitimate requests to reach destinations. Post-attack analysis identifies attack vectors and refines protection strategies. Security engineers might explore updated Check Point credentials covering current threat mitigation techniques.
Enabling Secure Collaboration and Communication
Business collaboration platforms including video conferencing, messaging, and file sharing create productivity benefits while introducing security and compliance risks. DLP policies prevent sensitive information from being shared inappropriately through collaboration tools. Conditional access ensures only authorized users on compliant devices can access collaboration platforms. Engineers configure integration between SSE platforms and collaboration services to enforce security policies. Encryption protects data in transit and at rest within collaboration environments. Audit logging captures collaboration activities for compliance and investigation purposes. Guest access controls limit external participant capabilities while enabling business partnerships. Professionals seeking advanced expertise might pursue Check Point CCSE credentials covering comprehensive security engineering.
Protecting Against Ransomware and Extortion Attacks
Ransomware represents a critical threat that encrypts business data and demands payment for decryption keys. Modern ransomware variants also exfiltrate data before encryption to enable extortion threats. Prevention requires multiple security layers including endpoint protection, email filtering, network segmentation, and user awareness. SSE platforms detect ransomware communications with command-and-control infrastructure and block encryption attempts. Behavioral analysis identifies suspicious file modification patterns indicating ransomware activity. Backup integration ensures data recovery capabilities independent of ransom payment. Incident response procedures minimize business impact through rapid containment and restoration. Security engineers might reference advanced Check Point certifications when developing comprehensive anti-ransomware strategies.
Implementing Zero Trust for Hybrid Cloud Architectures
Hybrid cloud environments combine on-premises infrastructure with public cloud services, creating complex security requirements. Zero trust principles apply consistently across hybrid architectures regardless of workload location. Identity-based access controls replace network location assumptions in authorization decisions. Engineers configure secure interconnections between on-premises and cloud environments while maintaining consistent security policies. Workload segmentation prevents lateral movement across environment boundaries. Encrypted communications protect data transiting between environments. Unified management provides visibility and control across the hybrid architecture. Professionals pursuing comprehensive security credentials might explore Check Point expertise updates addressing hybrid security architectures.
Securing Application Programming Interfaces
APIs enable application integration and data exchange but introduce security vulnerabilities through authentication weaknesses, excessive permissions, and lack of input validation. API security requires authentication, authorization, rate limiting, and input validation. API gateways provide centralized security enforcement for API traffic. SSE platforms inspect API traffic to detect abuse, prevent data leakage, and enforce usage policies. Engineers configure API discovery to identify shadow APIs and undocumented endpoints. Schema validation ensures API requests conform to expected formats. Threat detection identifies credential stuffing, bot activity, and other API-targeted attacks. Security professionals might pursue Check Point cloud credentials to strengthen API protection capabilities.
Managing Security for Edge Computing Deployments
Edge computing places processing and data storage closer to users and IoT devices, improving performance while creating distributed security challenges. Edge locations often have limited security infrastructure and IT support. Centralized security management must accommodate edge deployment constraints including intermittent connectivity and resource limitations. SSE cloud delivery naturally supports edge computing security by providing protection without requiring local security infrastructure. Engineers configure policies appropriate for edge workloads and device populations. Lightweight agents on edge devices enforce security controls locally while reporting to central management. Secure tunnels protect communications between edge and cloud environments. Network security specialists might reference Check Point mobility credentials when securing edge deployments.
Orchestrating Security Across Multi-Vendor Environments
Enterprise security architectures typically include products from multiple vendors, creating integration challenges and management complexity. Security orchestration platforms integrate disparate tools through APIs and standardized protocols. Centralized visibility aggregates security data from multiple sources into unified dashboards. Engineers configure integrations between SSE platforms and existing security investments including SIEM, endpoint protection, and network security tools. Automated workflows span multiple security products to coordinate responses. Standards-based integration using protocols like STIX/TAXII enables threat intelligence sharing. Vendor-neutral skills allow engineers to optimize security architecture regardless of product selection. Check Point endpoint credentials for complementary endpoint security expertise.
Implementing Security for IoT and Connected Devices
IoT deployments introduce massive numbers of devices with varying security capabilities, creating visibility and management challenges. Device authentication prevents unauthorized devices from accessing networks. Network segmentation isolates IoT devices from critical systems and limits attack propagation. SSE platforms provide visibility into IoT device inventory, communications, and behavior patterns. Engineers configure security policies appropriate for different device categories based on function and risk. Anomaly detection identifies compromised IoT devices exhibiting unusual behaviors. Firmware vulnerability management ensures devices receive security updates. Security specialists Check Point threat prevention credentials covering comprehensive threat protection across diverse device types.
Ensuring Compliance with Privacy Regulations
Privacy regulations including GDPR, CCPA, and LGPD impose strict requirements on personal data handling, requiring technical and organizational controls. Data minimization limits collection to necessary information. Purpose limitation restricts usage to stated purposes. Data subject rights enable individuals to access, correct, or delete their personal data. Engineers configure DLP policies that detect and protect personal information across SSE platforms. Data residency controls ensure personal data remains in appropriate geographic locations. Audit logging demonstrates compliance with processing requirements. Privacy impact assessments evaluate security controls protecting personal data. Professionals developing comprehensive security skills might reference Check Point security credentials covering privacy protection techniques.
Protecting Intellectual Property and Trade Secrets
Intellectual property represents critical business assets requiring protection against theft, espionage, and inadvertent disclosure. Classification systems identify sensitive intellectual property and apply appropriate security controls. Access restrictions limit exposure to authorized personnel with business needs. SSE platforms prevent exfiltration of intellectual property through DLP policies, behavior analysis, and access controls. Engineers configure enhanced monitoring for users accessing sensitive intellectual property. Watermarking and rights management technologies track document usage and prevent unauthorized redistribution. Exit interviews and access reviews ensure departing employees no longer retain access to trade secrets. Security professionals might explore Check Point troubleshooting credentials to enhance their diagnostic capabilities protecting critical assets.
Developing Security Awareness Training Programs
User security awareness significantly impacts organizational risk posture by reducing susceptibility to phishing, social engineering, and unsafe practices. Effective training programs engage users through relevant scenarios, interactive content, and regular reinforcement. Simulated attacks measure training effectiveness and identify users requiring additional education. Engineers integrate security awareness into onboarding processes, annual training requirements, and just-in-time reminders based on risky behaviors. Gamification improves engagement and knowledge retention. Metrics track training completion, phishing simulation results, and security incident rates. Executive communications secure leadership support and resources for awareness programs. Continuous improvement refines content based on emerging threats and user feedback.
Evaluating and Selecting Security Technologies
Technology evaluation processes ensure organizations select solutions that address requirements effectively while integrating with existing architectures. Requirements definition captures functional needs, performance expectations, and operational constraints. Vendor evaluation assesses product capabilities, company viability, and support quality. Proof of concept testing validates vendor claims and reveals integration challenges before purchase commitments. Total cost of ownership analysis includes licensing, implementation, and ongoing operational costs. Reference checks with similar organizations provide insights into real-world experiences. Selection criteria balance technical capabilities, cost, vendor relationships, and strategic alignment. Engineers contribute technical expertise to evaluation processes while collaborating with stakeholders on requirements and priorities. Professionals developing comprehensive security architectures might reference Check Point CCTE credentials covering advanced troubleshooting and technology evaluation.
Building Security Communities of Practice
Communities of practice bring together security professionals to share knowledge, solve problems, and advance collective expertise. Internal communities within organizations facilitate knowledge transfer and establish consistent practices. External communities including industry groups and vendor user forums provide broader perspectives and networking opportunities. Engineers participate in community discussions, contribute solutions to common challenges, and mentor less experienced professionals. Knowledge sharing accelerates organizational learning and prevents repeated mistakes. Collaborative problem-solving leverages diverse experiences and perspectives. Community participation enhances professional development while building industry relationships. Successful communities balance formal structure with organic collaboration and recognize contributions from active participants.
Conclusion:
The Palo Alto Networks SSE-Engineer certification represents far more than technical validation; it signifies mastery of modern security architectures that protect organizations navigating complex digital transformation journeys. We have explored the comprehensive knowledge domains required for effective SSE implementation, from foundational zero trust principles through advanced capabilities including threat prevention, data protection, and cloud security. The SSE framework addresses fundamental security challenges created by distributed workforces, multi-cloud adoption, and sophisticated threat actors that traditional perimeter-based defenses cannot adequately counter. Security professionals who earn this certification position themselves as strategic advisors capable of designing security architectures that enable rather than impede business objectives while maintaining comprehensive threat protection.
The competencies validated through SSE-Engineer certification extend across technical implementation, architectural design, operational management, and business alignment. Engineers must master secure web gateway configuration, CASB integration, zero trust network access deployment, and advanced threat prevention while understanding how these capabilities combine to deliver comprehensive security outcomes. Beyond technical configuration skills, successful SSE engineers develop expertise in policy framework design, compliance management, incident response orchestration, and stakeholder communication that transform security from technical implementation into business enablement. The certification journey builds proficiency across identity management, data loss prevention, application control, and threat intelligence integration that collectively address the diverse security challenges facing modern organizations operating in hybrid and multi-cloud environments.
As organizations worldwide accelerate cloud adoption and embrace flexible work models, demand for qualified SSE engineers continues to expand dramatically. Certified professionals command premium compensation reflecting their specialized expertise and ability to deliver security solutions aligned with contemporary business requirements. Career opportunities span consulting firms specializing in security transformation, enterprise security teams managing complex hybrid environments, managed security service providers delivering SSE as a service, and vendor organizations supporting customer implementations. The knowledge and skills developed through SSE-Engineer certification preparation create career resilience as security architectures continue evolving toward cloud-native, identity-centric models that will dominate the next generation of enterprise security.
The journey from certification candidate to accomplished SSE engineer requires dedication to hands-on practice, continuous learning, and genuine commitment to solving complex security challenges through innovative technology application. Successful engineers view certification as a milestone rather than a destination, recognizing that emerging threats, evolving platform capabilities, and changing business requirements demand ongoing professional development. Those who embrace continuous learning build careers characterized by technical excellence, meaningful organizational impact, and professional recognition. The comprehensive exploration of SSE technologies, implementation strategies, and operational best practices throughout this series provides an extensive foundation for professionals pursuing excellence in modern security architecture through Palo Alto Networks specialization.
Organizations investing in SSE-Engineer certified professionals gain more than technical expertise; they acquire strategic advisors who understand how to balance security requirements with business enablement, operational efficiency, and user experience. These professionals design architectures that protect critical assets while supporting digital transformation initiatives including cloud migration, application modernization, and workforce mobility. Their expertise enables organizations to confidently adopt cloud services, support remote workforces, and accelerate innovation without compromising security posture. The SSE-Engineer certification validates comprehensive competencies that transform security from potential business obstacle into competitive advantage, enabling organizations to pursue opportunities with confidence that comprehensive protections safeguard their most valuable assets throughout their digital transformation journeys.