Exam Code: FCSS_SASE_AD-25
Exam Name: FCSS - FortiSASE 25 Administrator
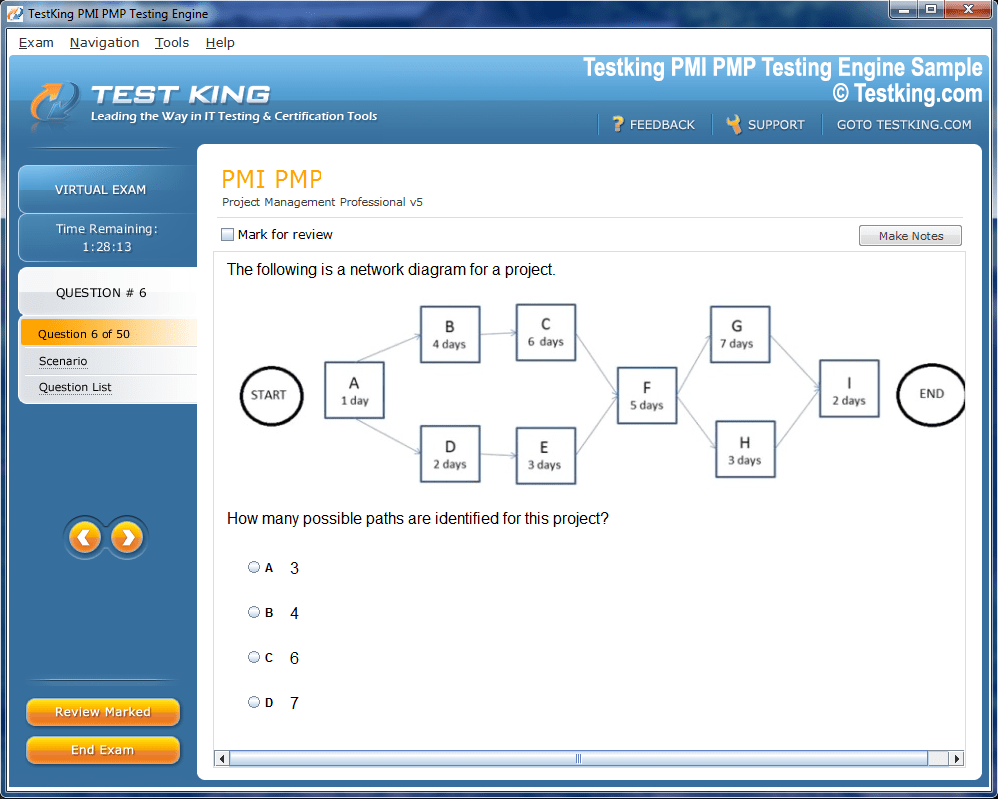
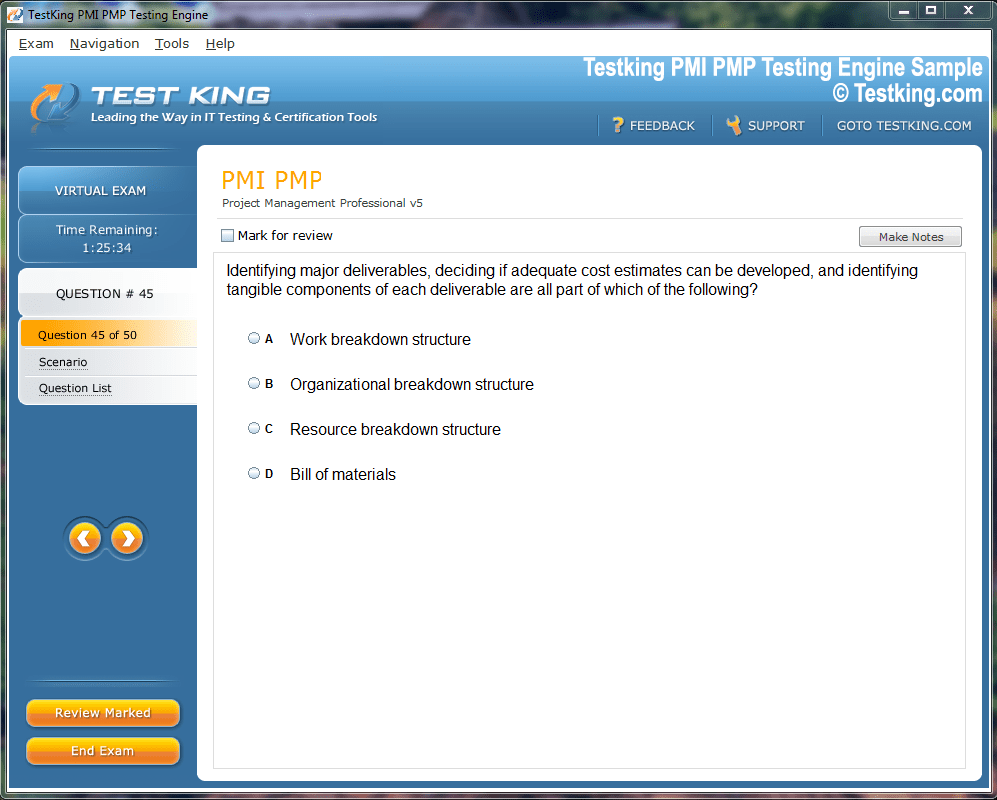
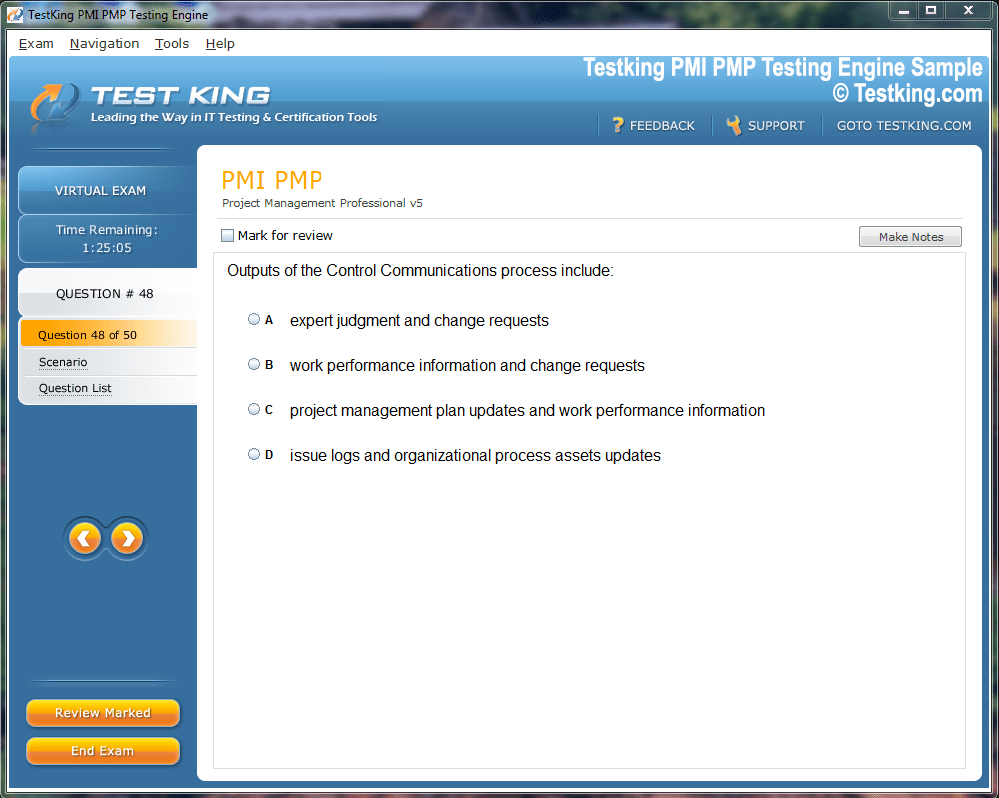
Product Screenshots
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our FCSS_SASE_AD-25 testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.
Top Fortinet Exams
- NSE4_FGT_AD-7.6 - Fortinet NSE 4 - FortiOS 7.6 Administrator
- FCSS_EFW_AD-7.6 - NSE 7 - Enterprise Firewall 7.6 Administrator
- FCP_FMG_AD-7.6 - Fortinet NSE 5 - FortiManager 7.6 Administrator
- FCSS_NST_SE-7.6 - Fortinet NSE 6 - Network Security 7.6 Support Engineer
- FCP_FGT_AD-7.6 - FCP - FortiGate 7.6 Administrator
- FCSS_LED_AR-7.6 - Fortinet NSE 6 - LAN Edge 7.6 Architect
- FCP_FAZ_AN-7.6 - Fortinet NSE 5 - FortiAnalyzer 7.6 Analyst
- NSE5_SSE_AD-7.6 - Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator
- NSE5_FSW_AD-7.6 - Fortinet NSE 5 - FortiSwitch 7.6 Administrator
- NSE6_SDW_AD-7.6 - Fortinet NSE 6 - SD-WAN 7.6 Enterprise Administrator
- NSE7_SSE_AD-25 - Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator
- FCP_FCT_AD-7.4 - Fortinet NSE 6 - FortiClient EMS 7.4 Administrator
- FCP_FWB_AD-7.4 - FCP - FortiWeb 7.4 Administrator
- NSE7_SOC_AR-7.6 - Fortinet NSE 7 - Security Operations 7.6 Architect
- FCP_FWF_AD-7.4 - FCP - Secure Wireless LAN 7.4 Administrator
- NSE6_OTS_AR-7.6 - Fortinet NSE 6 - OT Security 7.6 Architect
- FCSS_CDS_AR-7.6 - FCSS - Public Cloud Security 7.6 Architect
- NSE5_FNC_AD-7.6 - Fortinet NSE 5 - FortiNAC-F 7.6 Administrator
- NSE6_FSR-7.3 - Fortinet NSE 6 - FortiSOAR 7.3 Administrator
- FCP_FML_AD-7.4 - FCP - FortiMail 7.4 Administrator
- NSE4_FGT-7.0 - Fortinet NSE 4 - FortiOS 7.0
- FCP_FSM_AN-7.2 - FCP - FortiSIEM 7.2 Analyst
- FCSS_SASE_AD-25 - FCSS - FortiSASE 25 Administrator
- FCP_FGT_AD-7.4 - FCP - FortiGate 7.4 Administrator
- NSE7_OTS-7.2 - Fortinet NSE 7 - OT Security 7.2
- FCP_FMG_AD-7.4 - FCP - FortiManager 7.4 Administrator
- FCSS_SDW_AR-7.6 - FCSS - SD-WAN 7.6 Architect
- NSE7_NST-7.2 - Fortinet NSE 7 - Network Security 7.2 Support Engineer
- FCSS_EFW_AD-7.4 - FCSS - Enterprise Firewall 7.4 Administrator
- FCSS_NST_SE-7.4 - FCSS - Network Security 7.4 Support Engineer
- FCP_FAZ_AN-7.4 - FCP - FortiAnalyzer 7.4 Analyst
- NSE4_FGT-6.4 - Fortinet NSE 4 - FortiOS 6.4
- NSE6_EDR_AD-7.0 - Fortinet NSE 6 - FortiEDR 7.0 Administrator
- NSE6_FSW-7.2 - Fortinet NSE 6 - FortiSwitch 7.2
- FCP_FCT_AD-7.2 - FCP - Forti Client EMS 7.2 Administrator
- NSE6_FSM_AN-7.4 - Fortinet NSE 6 - FortiSIEM 7.4 Analyst
How Fortinet FCSS_SASE_AD-25 Practice Exams Help Validate Real-World SASE Deployment Skills
The networking and security industry has undergone a fundamental architectural shift over the past several years as organizations moved away from traditional perimeter-based security models toward cloud-native frameworks that can protect distributed workforces, multi-cloud environments, and increasingly complex hybrid infrastructure. Secure Access Service Edge, universally known as SASE, emerged as the definitive architectural response to these challenges by converging wide area networking capabilities with comprehensive cloud-delivered security services into a single unified platform. Fortinet, one of the most respected names in enterprise networking and cybersecurity, developed the FCSS_SASE_AD-25 certification to validate the expertise of professionals who can design, deploy, and manage SASE solutions built on the Fortinet product ecosystem.
The FCSS designation stands for Fortinet Certified Solution Specialist, and the SASE_AD-25 suffix identifies this specific credential as focused on SASE architecture and deployment for the 2025 examination cycle. For network engineers, security architects, and cloud infrastructure professionals who work with Fortinet technologies, this certification represents a meaningful validation of specialized expertise that goes significantly beyond general networking knowledge. Understanding why this certification exists, what professional problem it solves, and why practice exams play such a critical role in validating readiness helps candidates approach their preparation with the strategic clarity and focused effort that success on this demanding examination requires.
Exploring What SASE Architecture Actually Means for Modern Enterprise Networks
Before diving into the specifics of the FCSS_SASE_AD-25 examination and how practice exams contribute to preparation success, it is essential to develop a clear and accurate understanding of what SASE architecture actually entails and why it has become such a transformative force in enterprise networking and security. Gartner analyst John Burke coined the term SASE in 2019 to describe a converged framework that combines software-defined wide area networking with a comprehensive suite of cloud-delivered security services including secure web gateway, cloud access security broker, firewall as a service, and zero trust network access. This convergence addresses a fundamental tension that emerged as organizations adopted cloud applications and remote work at scale while their security architectures remained anchored to data center perimeters that no longer reflected where users, data, and applications actually resided.
The Fortinet approach to SASE, delivered primarily through the FortiSASE platform, implements this architectural vision using Fortinet's established security technologies in a cloud-delivered model that extends consistent security policies to users regardless of their location or the device they are using. Understanding the architectural principles of SASE, including the concept of identity-driven security, the role of the cloud-native service edge, and how SD-WAN capabilities integrate with security services, provides the conceptual foundation that makes the more specific technical content of the FCSS_SASE_AD-25 examination comprehensible and retainable rather than a disconnected collection of product-specific facts.
Mapping the Examination Domains That Define the Scope of Required Technical Knowledge
The FCSS_SASE_AD-25 examination is organized around a set of technical domains that collectively cover the complete lifecycle of a Fortinet SASE deployment, from initial architecture design through configuration, integration, troubleshooting, and ongoing operational management. Candidates who understand the domain structure of the exam before beginning their preparation are better positioned to allocate their study time proportionally and ensure that no significant knowledge area is neglected during the weeks of preparation that precede the examination. The domains typically cover FortiSASE architecture and components, zero trust network access configuration, secure web gateway and content inspection, SD-WAN integration with SASE, identity and authentication management, and security policy design and enforcement.
Each domain contains multiple specific technical topics that require both conceptual understanding and practical configuration knowledge, reflecting the applied nature of the FCSS_SASE_AD-25 credential as a specialist certification for working professionals rather than an entry-level awareness credential. The examination uses scenario-based questions that present realistic deployment challenges and require candidates to select the most appropriate configuration approach, troubleshooting methodology, or architectural decision from among several technically plausible options. Understanding the domain weighting, which indicates how many exam questions come from each area, allows candidates to focus their most intensive preparation on the domains that carry the greatest impact on the overall score while ensuring adequate coverage of lighter-weighted but still examinable content areas.
Recognizing Why Practice Exams Serve as the Most Effective Validation Tool
Practice exams occupy a uniquely valuable position in the certification preparation toolkit because they simultaneously serve multiple important functions that no other study resource can replicate as effectively or as efficiently. Unlike reading documentation, watching training videos, or completing lab exercises, practice exams force candidates to actively retrieve and apply knowledge under time pressure and in the face of carefully designed distractors, which is precisely the cognitive challenge that the actual examination presents. This retrieval practice effect, which is well-documented in educational psychology research, produces significantly stronger and more durable knowledge retention than passive study methods because it engages the brain's memory consolidation processes more deeply and more completely.
For the FCSS_SASE_AD-25 specifically, practice exams provide a particularly valuable function by exposing candidates to the specific ways in which Fortinet frames technical questions about SASE deployment scenarios, which differ meaningfully from how the same technical content might be presented in product documentation or training courses. The examination requires candidates to reason about trade-offs between different configuration approaches, identify the root causes of described network problems, and select the most appropriate architectural patterns for specific organizational requirements, all of which are reasoning skills that develop through practice rather than through passive consumption of information. Regular practice exam sessions throughout the preparation period provide a reliable metric of preparation progress that helps candidates make informed decisions about when they are genuinely ready to sit the actual examination.
Diagnosing Technical Knowledge Gaps Through Systematic Practice Exam Analysis
The diagnostic value of practice exams extends far beyond the simple score percentage that appears at the end of each session, and candidates who treat practice exam results as rich diagnostic data rather than simple pass-fail indicators will extract significantly more value from every practice session they complete. Every incorrect answer on a practice exam represents a specific knowledge gap that, once identified and addressed, directly improves the candidate's readiness for the actual examination. The key to extracting this diagnostic value lies in the quality of the post-session review process, where candidates examine not just which questions they got wrong but why they got them wrong and what specific knowledge or reasoning process would have led them to the correct answer.
For FCSS_SASE_AD-25 candidates, common categories of knowledge gaps revealed through practice exam analysis include confusion between similar FortiSASE configuration options that have subtly different effects, incomplete understanding of the sequence in which SASE policy components are evaluated, and gaps in knowledge about how FortiSASE integrates with other Fortinet products such as FortiManager, FortiAnalyzer, and FortiClient. Tracking the specific topics associated with incorrect answers across multiple practice sessions reveals patterns that indicate which curriculum areas require the most intensive review and helps candidates prioritize their remaining study time as the examination date approaches. This data-driven approach to preparation is far more efficient than reviewing all material equally regardless of the candidate's demonstrated proficiency level in each area.
Building Genuine Configuration Proficiency Through Scenario-Based Practice Questions
The FCSS_SASE_AD-25 examination does not primarily test the ability to recall isolated facts about Fortinet SASE products; it tests the ability to apply technical knowledge to realistic deployment scenarios that reflect the kinds of challenges working network and security engineers encounter in their professional roles. This scenario-based examination design means that candidates who develop genuine configuration proficiency through hands-on practice will consistently outperform those who rely solely on memorization, because scenario questions require the integration of multiple knowledge areas and the application of sound technical reasoning rather than simple fact retrieval.
High-quality practice exams for the FCSS_SASE_AD-25 present scenarios that describe specific organizational requirements, network architectures, or operational problems and ask candidates to identify the correct configuration approach, the most appropriate policy design, or the likely root cause of the described issue. Working through these scenarios during preparation builds the pattern recognition skills that allow experienced practitioners to quickly identify the relevant technical principles and apply them correctly within the constraints of the examination time limit. Candidates should approach practice scenarios with the same methodical reasoning they would apply to real deployment challenges, reading the scenario carefully to identify the key requirements and constraints before evaluating the available answer options against those criteria rather than simply selecting the answer that sounds most familiar.
Mastering FortiSASE Zero Trust Network Access Configuration and Policy Design
Zero trust network access represents one of the most important and most heavily tested components of the FCSS_SASE_AD-25 examination because it embodies the fundamental security principle that drives SASE adoption in the first place. Traditional network security models granted broad access to users who authenticated successfully at the network perimeter, trusting that anyone inside the network was authorized to access resources freely. Zero trust inverts this model by requiring continuous verification of every access request regardless of the user's location, device, or previous authentication status, granting only the minimum access required for the specific task at hand rather than broad network-level access.
FortiSASE implements zero trust network access through a combination of identity verification, device posture assessment, and granular application access policies that together ensure only the right users with compliant devices can access specific authorized applications. Candidates must understand how to configure ZTNA tags that classify devices based on their security posture, how to create ZTNA access proxy rules that control which users can reach which applications, and how to integrate FortiSASE ZTNA with identity providers such as Azure Active Directory or on-premises LDAP directories. Practice exam questions in this domain often present scenarios where a described access control requirement must be translated into a specific ZTNA configuration, requiring candidates to understand both the desired security outcome and the specific FortiSASE mechanisms that achieve it effectively.
Understanding Secure Web Gateway Functions Within the FortiSASE Platform
The secure web gateway component of FortiSASE provides cloud-delivered web filtering, SSL inspection, application control, and threat prevention for users accessing the internet regardless of their physical location or the network they are connected to. This capability is particularly important for organizations with large remote workforces whose internet traffic previously bypassed corporate security controls when working outside the office environment, creating significant blind spots in the organization's threat visibility and policy enforcement capabilities. Candidates preparing for the FCSS_SASE_AD-25 examination must develop thorough understanding of how to configure and optimize the secure web gateway features within FortiSASE to meet specific organizational security and compliance requirements.
SSL deep inspection is one of the most technically complex aspects of secure web gateway configuration because it requires FortiSASE to act as a trusted intermediary for encrypted HTTPS traffic, decrypting content for inspection before re-encrypting it for delivery to the user. Understanding the certificate trust requirements, the categories of traffic that should be excluded from deep inspection for privacy or technical compatibility reasons, and the performance implications of different inspection configurations prepares candidates for the nuanced practice exam questions that test this knowledge area. Web filtering profile design, application control policy creation, and the integration of FortiSASE web security features with FortiGuard intelligence services are additional configuration topics that practice exam questions regularly address in the context of realistic organizational deployment scenarios.
Integrating SD-WAN Capabilities With SASE Security Services for Unified Branch Connectivity
One of Fortinet's most significant competitive differentiators in the SASE market is its ability to deliver tightly integrated SD-WAN and security capabilities within a unified architecture that spans both branch office infrastructure and cloud-delivered security services. The FCSS_SASE_AD-25 examination reflects this integration by testing candidates on their ability to design and configure solutions that combine FortiGate SD-WAN functionality at branch locations with FortiSASE cloud security services in ways that provide optimal performance, consistent policy enforcement, and simplified management across distributed enterprise environments.
Understanding how FortiGate branch devices connect to FortiSASE points of presence to create secure tunnels that carry branch user traffic through cloud-delivered security inspection is a fundamental architectural concept that candidates must master. SD-WAN application steering policies that intelligently route different types of traffic to appropriate paths, whether directly to cloud applications, through FortiSASE for security inspection, or back to the corporate data center for legacy application access, represent the kind of nuanced configuration knowledge that the examination tests through scenario-based questions. Practice exams that include SD-WAN and SASE integration scenarios help candidates develop the ability to reason about connectivity architecture holistically rather than treating networking and security as separate concerns that happen to coexist within the same platform.
Analyzing Identity and Authentication Architecture Within Enterprise SASE Deployments
Identity has become the new perimeter in modern security architectures, and the FCSS_SASE_AD-25 examination reflects this reality by testing candidates extensively on their ability to design and implement identity and authentication solutions that integrate seamlessly with FortiSASE to provide strong, user-centric access control across the entire enterprise environment. The shift from network-location-based trust to identity-based trust requires that SASE deployments maintain tight integration with enterprise identity providers, single sign-on platforms, and multi-factor authentication systems that collectively verify the claimed identity of every user requesting access to protected resources.
FortiSASE supports integration with major identity providers through standard protocols including SAML, OAuth, and LDAP, and candidates must understand how to configure these integrations correctly to ensure that authentication events in the identity provider are properly reflected in FortiSASE access control decisions. Multi-factor authentication enforcement policies, conditional access rules that adjust authentication requirements based on risk signals such as device posture or unusual access patterns, and user group mappings that translate identity provider group memberships into FortiSASE policy assignments are configuration areas that practice exam questions regularly explore. Understanding how identity information flows through the SASE architecture to inform logging, reporting, and incident response capabilities is equally important for candidates who want to demonstrate comprehensive expertise rather than narrow configuration knowledge.
Troubleshooting Common FortiSASE Deployment Issues Using Systematic Diagnostic Approaches
The ability to troubleshoot problems effectively in a live FortiSASE deployment is a practical skill that the FCSS_SASE_AD-25 examination tests through scenario questions that describe symptoms and require candidates to identify the most likely root cause and the most appropriate diagnostic or remediation steps. Troubleshooting questions are particularly valuable indicators of genuine expertise because they require candidates to reason backward from observed symptoms to underlying causes using their understanding of how FortiSASE components interact, rather than simply recalling configuration procedures from memory.
Common troubleshooting scenarios that appear in practice exams include users unable to authenticate through the FortiSASE portal due to identity provider integration misconfigurations, SSL inspection failures caused by certificate trust issues on client devices, ZTNA access policy mismatches that prevent authorized users from reaching specific applications, and performance degradation caused by suboptimal traffic steering decisions in SD-WAN integration scenarios. Developing systematic troubleshooting methodologies that begin with the most likely causes and progress logically through diagnostic steps is a professional skill that practice exams help cultivate by repeatedly presenting candidates with diagnostic challenges that require structured reasoning. Candidates who build strong troubleshooting capabilities through practice exam preparation will find that this skill transfers directly into their professional work, making the preparation investment valuable beyond the certification outcome.
Developing an Optimal Study Schedule That Balances Theory and Hands-On Practice
Creating a realistic and well-structured study schedule for the FCSS_SASE_AD-25 examination requires honest assessment of the candidate's existing knowledge and experience with Fortinet SASE technologies, as the appropriate preparation timeline and emphasis will vary significantly between candidates with extensive FortiSASE deployment experience and those approaching the material primarily from a theoretical foundation. Most candidates find that a preparation period of eight to twelve weeks provides sufficient time to cover all examination domains thoroughly, complete meaningful hands-on practice in a FortiSASE lab environment, and work through multiple rounds of practice exams with thorough review of results.
The preparation timeline should be organized into three distinct phases that build progressively toward examination readiness. The first phase should focus on conceptual understanding of SASE architecture and FortiSASE platform components using official Fortinet training materials and documentation as the primary resources. The second phase should emphasize hands-on configuration practice, working through common deployment scenarios in a FortiSASE trial environment or Fortinet's online lab platform to build the practical familiarity that scenario-based exam questions demand. The third phase should shift emphasis toward intensive practice exam sessions with thorough diagnostic review, targeted remediation of identified knowledge gaps, and consolidation of understanding across all domains in preparation for the actual examination date.
Selecting High-Quality Practice Exam Resources That Accurately Reflect Examination Standards
The quality of practice exam resources varies considerably across providers, and candidates who invest time in identifying and using high-quality materials will experience significantly better preparation outcomes than those who rely on low-quality question banks that misrepresent the examination's difficulty, style, or technical accuracy. High-quality practice exams for the FCSS_SASE_AD-25 are characterized by technically accurate content that reflects current FortiSASE platform capabilities, scenario-based questions that require applied reasoning rather than simple recall, detailed explanations that teach the correct answer rather than simply identifying it, and regular updates that reflect changes to the examination objectives and the underlying Fortinet technology platform.
Fortinet's official training materials and the NSE Institute certification preparation resources represent the most authoritative sources of examination-aligned content and should be considered essential rather than optional components of any preparation strategy. Third-party practice exam providers that specialize in Fortinet certifications and maintain close alignment with official examination objectives can provide valuable supplementary practice that exposes candidates to a wider variety of question styles and scenarios than any single resource alone can offer. Community resources such as the Fortinet Community forums and professional networking groups where certified practitioners share study tips and examination experiences provide additional context and support that enriches the preparation journey and helps candidates develop the confidence they need to perform at their best on examination day.
Conclusion
The Fortinet FCSS_SASE_AD-25 certification represents a rigorous and professionally meaningful validation of expertise for network and security professionals who deploy and manage SASE solutions built on the Fortinet platform, and practice exams play an irreplaceable role in preparing candidates to succeed on both the theoretical and applied dimensions of this challenging examination. By diagnosing knowledge gaps systematically, building scenario reasoning skills through repeated practice, developing troubleshooting capabilities that mirror real deployment challenges, and providing reliable metrics of preparation progress, high-quality practice exams transform the certification preparation process from a passive information consumption exercise into an active skill development journey that produces genuine professional competence alongside examination readiness. Candidates who integrate practice exams strategically throughout their preparation timeline, using results as diagnostic data that guides targeted review rather than simply as score generators, will find themselves not only better prepared for the examination but more capable and confident practitioners in their daily professional work with Fortinet SASE technologies.