Certification: IBM Certified BPM System Administration - Business Process Manager Advanced V8.5
Certification Full Name: IBM Certified BPM System Administration - Business Process Manager Advanced V8.5
Certification Provider: IBM
Exam Code: C9510-401
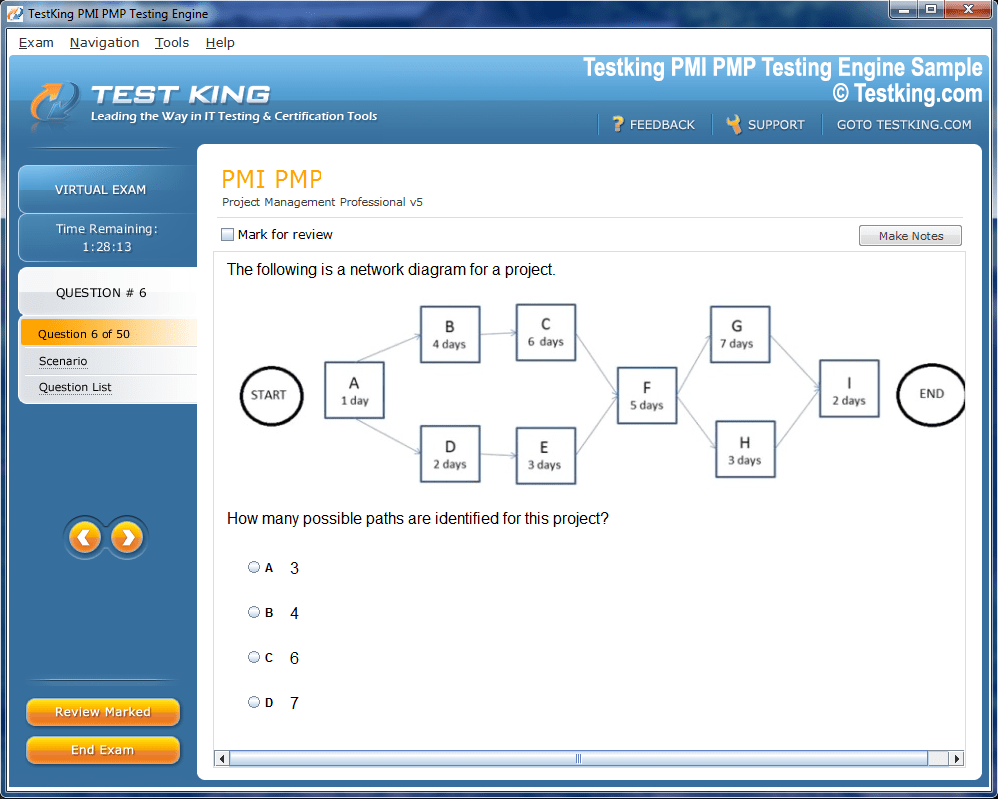
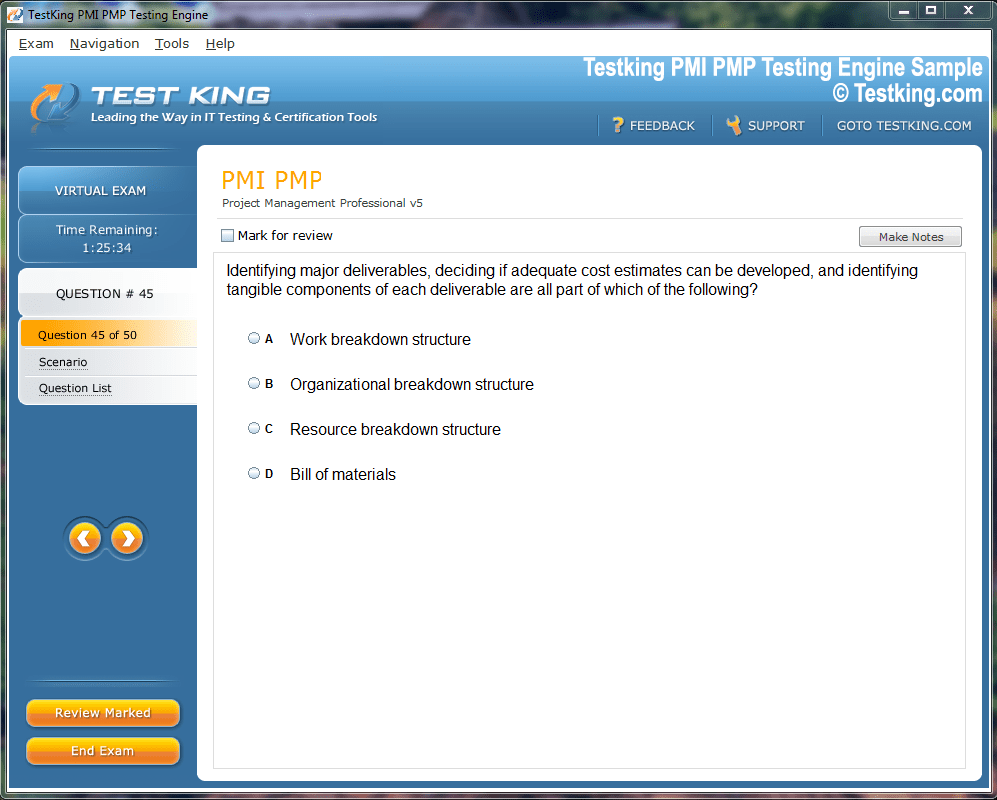
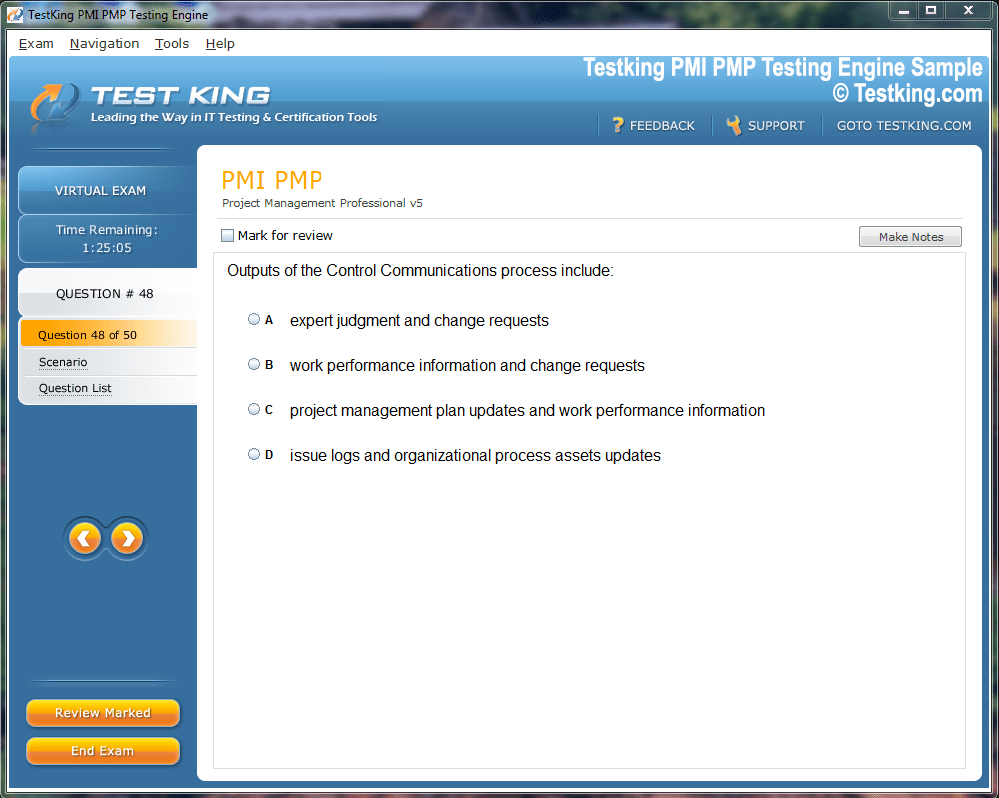
Product Screenshots
nop-1e =1
Mastering IBM Certified BPM System Administration - Business Process Manager Advanced V8.5 Certification for Enterprise Administrators
The IBM Certified BPM System Administration - Business Process Manager Advanced V8.5 certification was formally withdrawn on September 30, 2020, and is scheduled to expire on March 31, 2025. This certification was designed to validate the skills and competencies of individuals responsible for the meticulous orchestration, deployment, and administration of complex enterprise environments. Specifically, it caters to system administrators, system integrators, infrastructure architects, application architects, and solutions architects who are entrusted with ensuring the seamless operation of WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 ecosystems.
The primary focus of this certification is on the administration of IBM Process Center and IBM Process Server. Candidates are expected to possess a keen understanding of the intricate interconnections between business process management systems and application servers. The certification framework emphasizes practical capabilities such as installation, configuration, monitoring, troubleshooting, and optimization. Individuals in these roles must also exhibit an aptitude for resource management, deployment strategies, and secure operational practices.
Target Audience and Role Responsibilities
The target demographic for this certification encompasses professionals who routinely interact with enterprise-level software and process automation tools. System administrators are typically the custodians of server environments, ensuring uptime, stability, and scalability. In addition, system integrators and architects often contribute to designing, implementing, and maintaining infrastructural frameworks that support business process management.
In their daily responsibilities, certified individuals are expected to perform installation and configuration tasks for WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5. They are also responsible for selecting appropriate topologies, deploying business processes, and establishing connections to back-end resources. Furthermore, they must troubleshoot performance bottlenecks, monitor system health, and implement load-balancing strategies to maintain operational efficiency. This role requires not only technical proficiency but also an analytical mindset to anticipate potential challenges and implement proactive solutions.
The breadth of expertise required encompasses both infrastructure-level knowledge and application-level administration. For instance, administrators need to comprehend the nuances of clustering, scaling, and load distribution while also understanding how business processes interact with external services and databases. These responsibilities demand an intricate balance of technical dexterity, methodical problem-solving, and strategic foresight.
IBM Business Process Manager Advanced V8.5 Administration
At the core of this certification is the administration of IBM Business Process Manager Advanced V8.5. Professionals must be adept at installing and configuring the product, selecting optimal topologies, deploying processes, and integrating with back-end systems. Effective administration involves meticulous planning, such as determining resource allocation for optimal performance and ensuring that deployment environments align with business objectives.
Tuning the system for resource utilization is a critical aspect of administration. Candidates are expected to understand the performance implications of various configurations, including clustering, thread pools, and database connections. Clustering ensures high availability and fault tolerance, while load balancing distributes workloads to prevent system overload. Proper tuning is essential to maintain responsiveness and scalability, particularly in environments where complex business processes are executed concurrently.
Security is another paramount consideration. Administrators must implement measures to safeguard sensitive business process data, ensure secure communications between components, and manage user access permissions. Knowledge of network and operating system security concepts is crucial, as vulnerabilities at these layers can compromise the entire enterprise ecosystem. The ability to identify potential security risks, remediate vulnerabilities, and enforce best practices distinguishes proficient administrators from those with superficial knowledge.
Core Installation and Configuration Skills
Installation and configuration form the foundational pillars of the certification. Professionals must be capable of performing comprehensive installations of both WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5. Installation involves selecting the appropriate deployment topology, configuring databases and application servers, and establishing initial connectivity with essential back-end services.
Configuration extends beyond installation and encompasses the fine-tuning of system parameters, environment variables, and server settings. This includes setting JVM options, configuring data sources, establishing clustering parameters, and integrating with messaging systems. Administrators must also be proficient in command-line interfaces and scripting languages such as Jython and Jacl, which are used to automate repetitive tasks, streamline deployments, and maintain consistency across environments.
The ability to perform installation and configuration with minimal errors is essential. Misconfigurations can result in suboptimal performance, security vulnerabilities, and operational disruptions. Therefore, candidates must develop meticulous attention to detail, rigorous testing protocols, and a structured approach to documenting configurations and changes.
Topology Selection and Deployment Strategies
Topology selection is a critical decision that influences the performance, scalability, and reliability of the deployed environment. Administrators must evaluate business requirements, anticipated workloads, and system constraints to determine whether a single-server, multi-server, or clustered deployment is most appropriate. Each topology presents unique advantages and challenges, and the ability to discern which architecture aligns with organizational goals is a defining skill.
Deployment of business processes involves more than simply copying files to a server. Administrators must ensure that deployment units are correctly configured, dependencies are satisfied, and connections to back-end systems are properly established. They must also validate that processes perform as expected under varying workloads, identifying potential bottlenecks or failures before they impact end-users. This proactive approach to deployment helps maintain operational stability and supports continuous business operations.
Integration with Back-End Systems
IBM Business Process Manager Advanced V8.5 environments often rely on integration with a variety of back-end systems, including databases, messaging queues, enterprise resource planning systems, and web services. Administrators must have the ability to establish, monitor, and troubleshoot these connections. Misconfigured integrations can lead to transaction failures, performance degradation, or data inconsistencies, highlighting the need for meticulous attention to detail.
Troubleshooting integration issues requires a comprehensive understanding of both the process management environment and the back-end systems it interacts with. Professionals must be adept at analyzing logs, identifying root causes, and implementing corrective measures. This may involve modifying connection settings, adjusting performance parameters, or coordinating with other system owners to resolve underlying issues.
Performance Tuning and Resource Optimization
Ensuring optimal system performance is a continual responsibility for administrators. This includes monitoring resource utilization, such as CPU, memory, disk I/O, and network bandwidth, and making adjustments to maintain system responsiveness. Clustering and load balancing strategies are particularly important in high-traffic environments, where uneven distribution of workloads can lead to service degradation.
Administrators must also consider long-term scalability, anticipating future growth and adjusting configurations accordingly. This may involve adding additional nodes to a cluster, reconfiguring thread pools, or optimizing database connections. Effective performance tuning requires a combination of analytical skills, technical expertise, and practical experience, allowing administrators to maintain high availability and reliable service levels.
Security and Compliance Considerations
Security is a paramount concern for any enterprise environment. Administrators must implement measures to safeguard sensitive data, enforce user access controls, and ensure secure communication between system components. This includes configuring authentication and authorization mechanisms, encrypting data in transit and at rest, and monitoring for unauthorized access attempts.
Compliance with organizational policies and industry regulations is also a critical aspect of system administration. Administrators must ensure that all configurations, processes, and integrations adhere to established standards. This involves maintaining detailed documentation, conducting regular audits, and implementing corrective actions as needed. By maintaining a secure and compliant environment, administrators protect the organization from potential legal, financial, and reputational risks.
Self-Sufficiency and Problem-Solving
Certified administrators are expected to operate with a high degree of self-sufficiency. While access to product documentation and vendor support is available, professionals must rely on their knowledge and experience to perform most tasks independently. This includes troubleshooting complex issues, optimizing performance, and implementing configuration changes.
Problem-solving skills are essential in this context. Administrators must be able to analyze logs, trace errors, and develop solutions under time constraints. They must also be able to anticipate potential issues and implement preventive measures. This proactive approach ensures the smooth operation of enterprise environments and reduces the likelihood of unexpected downtime or service disruptions.
Examination Requirements and Structure
Attaining the IBM Certified BPM System Administration - Business Process Manager Advanced V8.5 certification requires successful completion of two examinations. These exams assess candidates’ abilities in installation, configuration, administration, troubleshooting, and performance optimization of both WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 environments.
The first examination, C2180-401, focuses on WebSphere Application Server Network Deployment V8.5.5 system administration. Candidates are expected to demonstrate knowledge of Java Enterprise Edition 6, web application architecture and deployment, command-line interfaces, scripting languages such as Jython and Jacl, network and operating system security concepts, and problem determination techniques.
The second examination, C2180-402, addresses IBM Business Process Manager Advanced V8.5 system administration. Candidates must demonstrate general knowledge of Java Enterprise Edition, Service-Oriented Architecture, and business process management administration. The exams are designed to validate practical skills and theoretical knowledge required for effective system administration in enterprise environments.
Recommended Foundational Skills
Prior to pursuing this certification, candidates are encouraged to develop foundational skills that support success in the exams and in practical administration roles. These skills include understanding Java Enterprise Edition, web application architecture, command-line interfaces, network and operating system fundamentals, and security principles. While these foundational skills are not directly assessed on the examinations, they provide the essential groundwork for advanced topics and practical tasks.
Developing proficiency in these areas ensures that candidates can approach the certification process with confidence and are prepared to handle the complex responsibilities associated with managing enterprise-level process management environments.
Advanced Administration of WebSphere Application Server Network Deployment
Administrators responsible for WebSphere Application Server Network Deployment V8.5.5 must exhibit an intricate understanding of system architecture, resource orchestration, and service provisioning. The certification emphasizes the capacity to configure and maintain complex server environments that support enterprise-scale applications. A significant portion of these responsibilities involves ensuring high availability, fault tolerance, and optimal performance across distributed nodes.
System administrators are tasked with configuring deployment managers, node agents, and server instances to create a resilient, scalable environment. They must also develop and implement strategies for clustering, which allows multiple server instances to operate as a cohesive unit, ensuring that workloads are efficiently distributed and services remain uninterrupted during node failures or maintenance activities. Clustering demands a comprehensive knowledge of replication domains, session persistence, and failover mechanisms.
Command-line proficiency is indispensable for administrators, as scripting provides automation capabilities that reduce human error and enhance operational efficiency. Languages such as Jython and Jacl are used extensively to automate repetitive tasks, configure environments consistently, and execute maintenance routines. Mastery of these tools allows administrators to deploy updates, manage configuration changes, and troubleshoot issues with minimal manual intervention.
Integration of IBM Business Process Manager Advanced V8.5 with Enterprise Systems
Effective administration of IBM Business Process Manager Advanced V8.5 entails seamless integration with enterprise back-end systems, including databases, web services, and messaging platforms. Administrators must possess the acumen to establish, configure, and monitor these integrations to ensure smooth workflow execution and transactional integrity.
Integration challenges often manifest as performance bottlenecks, communication failures, or data inconsistencies. Administrators must be adept at dissecting logs, tracing transaction flows, and resolving integration anomalies. Solutions may include adjusting connection pool parameters, refining service endpoints, or reconfiguring message brokers. In addition, proactive monitoring and alerting mechanisms are critical to anticipate issues and prevent disruptions before they affect end-users.
The ability to understand interdependencies among business processes and external systems is vital. For instance, administrators must recognize how database performance affects process execution or how messaging latency impacts transaction throughput. This holistic perspective allows them to optimize system configurations and maintain operational continuity.
Deployment and Topology Optimization
Deployment in IBM Business Process Manager Advanced V8.5 extends beyond the mere placement of artifacts on a server. Administrators must strategize the deployment to align with workload expectations, redundancy requirements, and scalability goals. Topology selection is central to this endeavor, requiring evaluation of various architectural options, including single-server, multi-server, and clustered deployments.
The chosen topology directly influences system performance, resource utilization, and maintenance complexity. Single-server deployments offer simplicity but lack redundancy, whereas clustered architectures provide resilience and load balancing capabilities. Multi-server topologies facilitate modular deployment, isolating workloads and simplifying fault isolation. Administrators must weigh these considerations against organizational requirements to select an optimal configuration.
In addition to topology, administrators must implement deployment strategies that ensure consistency across environments. This involves version control, automated deployment scripts, and rigorous testing procedures. Consistent deployments reduce the likelihood of configuration drift, which can introduce errors, security vulnerabilities, and performance degradation.
Performance Tuning and Load Management
Performance optimization is an ongoing responsibility for administrators. Continuous monitoring of resource utilization, including CPU, memory, disk I/O, and network throughput, is essential to maintain system responsiveness. Administrators employ metrics collection, profiling, and load testing to identify bottlenecks and implement corrective measures.
Load balancing is a critical component of performance management. Administrators must configure servers to distribute workloads evenly, preventing individual nodes from becoming overwhelmed. This may involve tuning thread pools, adjusting connection limits, or rebalancing workloads across clustered nodes. Clustering configurations must also account for session replication and state persistence to ensure uninterrupted service during failovers.
Resource optimization extends to database connections, messaging queues, and external service calls. Administrators must identify inefficient queries, optimize transaction flows, and fine-tune connection pools. These measures not only enhance system performance but also improve scalability, allowing the environment to accommodate increased workloads without degradation in service quality.
Security Administration and Compliance
Security considerations permeate every aspect of system administration. Professionals must implement measures to protect sensitive process data, enforce access control policies, and secure communication channels between components. This includes configuring authentication protocols, establishing authorization rules, and encrypting data in transit and at rest.
Administrators must also remain vigilant regarding compliance with organizational policies and regulatory mandates. Routine audits, security reviews, and log analysis are essential to detect anomalies and prevent breaches. Any modifications to configuration, deployment, or access must adhere to established standards to maintain integrity and regulatory compliance.
Additionally, administrators should incorporate intrusion detection, vulnerability scanning, and monitoring tools to fortify the environment against potential attacks. By establishing proactive security measures, they mitigate risks, protect sensitive information, and ensure continuous operational reliability.
Troubleshooting and Problem Resolution
Troubleshooting is a core competency for administrators. They must diagnose and resolve issues ranging from server failures and performance degradation to process execution errors and integration anomalies. Effective troubleshooting requires a combination of analytical skills, domain knowledge, and methodical problem-solving techniques.
Administrators often rely on log analysis, monitoring dashboards, and diagnostic tools to identify the root cause of problems. Understanding error codes, system events, and transactional traces enables them to pinpoint failures efficiently. Solutions may involve modifying configurations, restarting services, or applying patches. The ability to resolve issues quickly minimizes downtime and maintains user satisfaction.
Proactive problem management is equally important. Administrators should anticipate potential failure points, implement preventive measures, and continuously refine monitoring and alerting systems. This foresight ensures that issues are detected and mitigated before they escalate into significant disruptions.
System Optimization and Resource Management
Optimizing system resources is a multifaceted responsibility. Administrators must ensure that CPU cycles, memory allocation, storage, and network bandwidth are utilized effectively. Mismanagement of resources can lead to suboptimal performance, system instability, or service interruptions.
Effective resource management involves load forecasting, capacity planning, and performance tuning. Administrators may employ techniques such as dynamic resource allocation, memory tuning, and thread pool optimization to enhance system efficiency. Understanding the interaction between different system components allows administrators to make informed decisions about resource distribution and utilization.
Additionally, administrators must consider long-term scalability. Anticipating future growth and adjusting configurations accordingly ensures that the system can handle increased workloads without compromising performance. This foresight reduces the likelihood of costly system upgrades or emergency interventions.
Scripting and Automation
Scripting is a powerful tool for system administrators, enabling the automation of repetitive tasks, consistent deployment, and efficient troubleshooting. Languages such as Jython and Jacl allow administrators to create scripts for configuration, deployment, monitoring, and maintenance tasks.
Automation reduces human error, accelerates operational processes, and ensures consistency across environments. For instance, scripts can be used to deploy updates across multiple nodes simultaneously, apply configuration changes uniformly, or execute diagnostic routines on a schedule. This capability is particularly valuable in large-scale deployments where manual intervention would be inefficient and error-prone.
Proficiency in scripting also allows administrators to develop custom tools and utilities tailored to their specific environment. These tools enhance operational efficiency, provide additional monitoring capabilities, and facilitate rapid response to issues.
Exam Preparation and Knowledge Integration
Achieving certification requires mastery of both practical skills and theoretical knowledge. The examinations assess the candidate's ability to perform installations, configure environments, administer systems, troubleshoot issues, and optimize performance in enterprise contexts.
Candidates should focus on understanding the principles of Java Enterprise Edition, Service-Oriented Architecture, web application deployment, system security, and network administration. Integrating these concepts with hands-on experience in WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 environments is critical for exam success.
Preparation strategies include hands-on practice, simulation of deployment scenarios, and comprehensive review of system administration tasks. Familiarity with monitoring tools, performance metrics, log analysis, and troubleshooting methodologies provides a strong foundation for addressing exam scenarios and real-world challenges.
Foundational Knowledge and Skill Building
Before attempting the certification, candidates should cultivate foundational knowledge in key areas such as web application architecture, Java Enterprise Edition, network and operating system security, and command-line interface proficiency. These skills, while not directly tested, underpin the more advanced concepts assessed in the certification exams.
Understanding these foundational principles enables candidates to approach complex administration tasks with confidence and competence. Knowledge of operating system fundamentals, network protocols, security best practices, and scripting languages ensures that administrators can navigate the challenges of enterprise environments effectively.
System Architecture and Component Interaction
In the administration of IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment V8.5.5, a thorough understanding of system architecture is indispensable. Administrators must grasp how individual components—servers, nodes, clusters, databases, and messaging systems—interact to provide seamless process execution. This knowledge enables them to design environments that are resilient, scalable, and optimized for performance.
The architecture is composed of multiple layers, each with specific responsibilities. At the infrastructure layer, operating systems and network configurations provide the foundation for higher-level services. The middleware layer, which includes WebSphere Application Server, manages application deployment, transaction handling, and service orchestration. The business process layer, powered by IBM Business Process Manager Advanced V8.5, facilitates the modeling, execution, and monitoring of workflows. Understanding the dependencies between these layers allows administrators to predict potential points of failure and implement strategies to mitigate risks.
Installation and Configuration Best Practices
Installation of WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 requires meticulous attention to detail. Administrators must select installation paths, configure databases, and determine deployment topologies that align with enterprise objectives. The process often involves setting environment variables, defining JVM parameters, and establishing secure connections to back-end systems.
Configuration extends the installation phase, involving adjustments to server settings, connection pools, thread management, and clustering parameters. Administrators employ scripting languages such as Jython and Jacl to automate repetitive tasks, ensuring consistency and reducing the likelihood of human error. Automated scripts are also invaluable for applying patches, deploying updates, and maintaining synchronized configurations across multiple nodes.
Best practices in configuration emphasize maintainability, scalability, and security. For example, defining clear naming conventions for servers and clusters, documenting all changes, and employing version control systems ensures that environments remain manageable as they grow in complexity.
Clustering and High Availability
Clustering is a critical aspect of enterprise administration, providing high availability and load distribution for deployed applications. Administrators configure clusters to ensure that workloads are evenly distributed among server instances, reducing the risk of bottlenecks and single points of failure. Clustering also facilitates failover, allowing applications to remain operational when individual nodes experience downtime.
Effective clustering requires an understanding of session persistence, replication domains, and load-balancing algorithms. Administrators must ensure that cluster members share state information correctly, that session failover mechanisms are operational, and that communication between nodes is secure and efficient. Additionally, monitoring tools are employed to assess cluster performance, identify imbalances, and make real-time adjustments to resource allocation.
Deployment of Business Processes
Deploying business processes in IBM Business Process Manager Advanced V8.5 demands careful planning and validation. Administrators must ensure that deployment units are correctly structured, dependencies are satisfied, and connections to external systems are properly established. Failure to address these factors can lead to process execution errors, data inconsistencies, or degraded performance.
Deployment strategies often involve staging environments, where processes are tested under simulated workloads before being promoted to production. This practice allows administrators to identify configuration issues, performance bottlenecks, and integration challenges without impacting live operations. Deployment automation, using scripts and orchestration tools, ensures consistency and reduces manual intervention, thereby minimizing the risk of errors during rollouts.
Integration with Back-End Resources
Enterprise environments rely on the integration of IBM Business Process Manager Advanced V8.5 with various back-end systems such as databases, messaging platforms, ERP systems, and web services. Administrators must configure these integrations, monitor their performance, and troubleshoot issues to maintain transactional integrity and process continuity.
Integration challenges can arise from misconfigured connections, service latency, or incompatible protocols. Administrators employ diagnostic tools to trace transaction paths, identify anomalies, and implement corrective measures. This may include adjusting connection parameters, modifying service endpoints, or optimizing query performance. A deep understanding of both the business process environment and the underlying back-end systems is essential for effective problem resolution.
Performance Monitoring and Optimization
Continuous monitoring of system performance is critical for ensuring efficient operation. Administrators track metrics such as CPU utilization, memory consumption, disk I/O, and network throughput to detect potential performance issues. Profiling tools and log analysis help identify bottlenecks, inefficient processes, and resource contention.
Optimizing performance often involves tuning JVM parameters, configuring thread pools, adjusting database connection pools, and fine-tuning cluster settings. Load balancing is implemented to evenly distribute workloads, while caching and session management strategies enhance responsiveness. Administrators must balance performance optimization with resource utilization, ensuring that systems remain scalable and resilient under varying workloads.
Security and Compliance Management
Security is an integral part of system administration, encompassing authentication, authorization, data encryption, and secure communication between components. Administrators configure access controls, enforce policies, and monitor for unauthorized activity to protect sensitive business process data.
Compliance with regulatory standards and organizational policies is equally important. Administrators conduct regular audits, review logs, and implement controls to maintain adherence to these requirements. Security measures include network segmentation, intrusion detection, vulnerability assessments, and secure deployment practices. A proactive approach to security ensures that the environment remains robust against potential threats while safeguarding enterprise data integrity.
Troubleshooting and Root Cause Analysis
Administrators must possess strong troubleshooting skills to diagnose and resolve issues efficiently. Problems may manifest as server failures, process execution errors, performance degradation, or integration anomalies. Effective troubleshooting requires systematic analysis of logs, monitoring metrics, and configuration settings to identify root causes.
Root cause analysis involves examining system components, dependencies, and interconnections to pinpoint the source of issues. Once identified, corrective actions may include configuration adjustments, service restarts, patch application, or code modifications. A structured approach to problem resolution minimizes downtime and maintains operational continuity.
Resource Management and Scalability
Managing resources effectively is essential for maintaining system performance and scalability. Administrators allocate CPU, memory, storage, and network bandwidth to ensure optimal utilization and prevent resource contention. They also plan for future growth by evaluating workload trends and adjusting configurations proactively.
Scalability strategies include adding additional nodes to clusters, redistributing workloads, and tuning system parameters. Administrators must anticipate changes in demand, ensuring that the environment can accommodate increased usage without compromising performance or reliability. Efficient resource management enhances system resilience and supports sustainable growth.
Automation and Scripting Techniques
Automation is a cornerstone of modern system administration, enabling administrators to streamline tasks, reduce manual intervention, and maintain consistency across environments. Scripting languages such as Jython and Jacl are widely used to automate deployment, configuration, monitoring, and maintenance activities.
Automated scripts facilitate repetitive tasks, enforce standardized procedures, and accelerate response times during incidents. Administrators can develop custom scripts to address environment-specific requirements, such as batch deployments, configuration audits, and performance monitoring. This approach enhances operational efficiency and ensures that administrative tasks are executed accurately and consistently.
Exam Structure and Preparation
Achieving certification requires passing two examinations that assess both practical and theoretical competencies. The first exam, C2180-401, focuses on WebSphere Application Server Network Deployment V8.5.5 system administration. Topics include Java Enterprise Edition 6, web application deployment, command-line interfaces, scripting, security concepts, and troubleshooting.
The second exam, C2180-402, evaluates IBM Business Process Manager Advanced V8.5 system administration skills, covering Java Enterprise Edition, Service-Oriented Architecture, and business process administration. Candidates are expected to demonstrate their ability to configure environments, deploy processes, integrate with back-end systems, and optimize performance.
Preparation involves hands-on practice, simulation of deployment scenarios, and review of system administration concepts. Familiarity with monitoring tools, log analysis, and troubleshooting techniques enhances readiness and confidence. Combining practical experience with theoretical knowledge ensures comprehensive understanding and successful certification outcomes.
Foundational Skills and Knowledge
Prior to pursuing certification, candidates should establish foundational expertise in areas such as operating systems, network administration, Java Enterprise Edition, web application architecture, and command-line proficiency. These skills, while not directly tested, provide a necessary base for advanced administration tasks.
Understanding security principles, resource management, and scripting further equips candidates to navigate complex enterprise environments. These foundational competencies support efficient problem-solving, effective deployment, and reliable system administration, ultimately contributing to successful certification achievement.
Advanced Monitoring and System Observability
Effective administration of IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment V8.5.5 relies heavily on advanced monitoring and observability practices. Administrators must implement comprehensive monitoring frameworks to track the health, performance, and availability of all system components. This includes real-time observation of server metrics, business process execution, and integration points with back-end systems.
Observability extends beyond basic metrics, encompassing log aggregation, event correlation, and anomaly detection. Administrators employ diagnostic tools to interpret log files, trace transaction flows, and identify potential issues before they escalate into service disruptions. By establishing robust observability practices, administrators ensure proactive management, rapid problem identification, and enhanced operational resilience.
Middleware and Application Server Management
Managing WebSphere Application Server Network Deployment requires deep understanding of middleware functionality. Administrators oversee deployment managers, node agents, and server instances, ensuring consistent configuration and reliable operation. The ability to manage multiple server profiles, synchronize configuration changes, and monitor server logs is crucial for maintaining stability across distributed environments.
Server management also involves performance optimization, fault detection, and routine maintenance. Administrators must ensure that JVM parameters are tuned appropriately, thread pools are balanced, and server resources are allocated efficiently. Regular updates, patch management, and configuration audits contribute to long-term reliability and prevent degradation of service performance.
Business Process Execution and Optimization
IBM Business Process Manager Advanced V8.5 enables the orchestration of complex workflows that span multiple systems and services. Administrators must ensure that these business processes execute efficiently, reliably, and in accordance with organizational objectives. This involves monitoring process execution metrics, identifying bottlenecks, and optimizing the allocation of resources to support high-volume workloads.
Optimizing business processes may require adjusting process design, tuning execution parameters, or reconfiguring integration points with back-end systems. Administrators must maintain a balance between performance efficiency and operational reliability, ensuring that workflows meet both throughput and latency requirements. Advanced analytics and monitoring tools are leveraged to provide insight into process behavior and resource consumption patterns.
Cluster Management and Failover Strategies
Clusters are fundamental for achieving high availability and load distribution in enterprise environments. Administrators configure clusters to enable seamless failover, session persistence, and workload balancing. This requires a detailed understanding of cluster topology, replication mechanisms, and communication protocols between nodes.
Failover strategies are critical to maintaining uninterrupted service during node failures or planned maintenance. Administrators must implement health checks, monitoring alerts, and automated failover procedures. Regular testing of failover mechanisms ensures that redundancy functions correctly and that business processes continue to operate smoothly during disruptions.
Load Balancing and Resource Distribution
Load balancing is an essential practice for distributing workloads evenly across servers and clusters. Administrators configure load balancers, adjust routing rules, and optimize session handling to prevent overloading individual nodes. This not only improves system responsiveness but also enhances reliability and fault tolerance.
Resource distribution strategies extend to memory management, CPU allocation, and database connection pooling. Administrators analyze resource consumption patterns and adjust configurations to maximize efficiency. Proper resource allocation ensures that high-demand applications perform optimally without impacting other processes or services.
Security Implementation and Governance
Security administration is an ongoing responsibility that spans authentication, authorization, and data protection. Administrators must enforce robust security policies, configure access control mechanisms, and monitor for suspicious activity. Encryption of data in transit and at rest, along with secure communication protocols, is fundamental to protecting sensitive information.
Governance extends to compliance with organizational standards and regulatory requirements. Administrators conduct audits, review logs, and enforce policies to maintain adherence to security frameworks. Continuous assessment of potential vulnerabilities and proactive mitigation measures ensures that the environment remains resilient against emerging threats.
Backup, Recovery, and Business Continuity
Administrators are responsible for designing and implementing backup and recovery strategies to safeguard business process data and system configurations. This involves regular data backups, replication of critical resources, and testing of recovery procedures.
Business continuity planning ensures that enterprise operations can continue despite disruptions. Administrators develop disaster recovery scenarios, validate recovery time objectives (RTO), and coordinate failover procedures across clusters. A comprehensive continuity plan minimizes operational downtime and protects organizational assets from catastrophic failures.
Troubleshooting Complex Issues
Advanced troubleshooting involves systematic investigation of performance anomalies, integration failures, and process execution errors. Administrators leverage log analysis, diagnostic tools, and monitoring dashboards to identify root causes. Understanding error codes, transactional flows, and system interdependencies is critical for accurate problem resolution.
Effective troubleshooting also requires creativity and analytical reasoning. Administrators must consider multiple factors, including configuration changes, network issues, and process logic errors. Documenting incidents, solutions, and preventive measures contributes to organizational knowledge and improves response efficiency for future challenges.
Automation and Orchestration of Administrative Tasks
Automation reduces manual intervention, improves consistency, and accelerates administrative workflows. Administrators use Jython, Jacl, and other scripting techniques to automate configuration, deployment, monitoring, and maintenance activities. Scripts can be executed across multiple nodes to ensure uniformity and efficiency in large-scale environments.
Orchestration extends automation by coordinating complex sequences of tasks across different systems. Administrators design workflows for automated deployments, health checks, and failover procedures. By integrating orchestration with monitoring systems, they create intelligent operational routines that respond dynamically to system conditions.
Performance Tuning and Optimization Strategies
Optimizing system performance involves a combination of monitoring, analysis, and configuration adjustment. Administrators evaluate metrics such as CPU load, memory usage, response times, and transaction throughput. Based on these observations, they fine-tune JVM settings, thread pools, database connections, and cluster configurations.
Proactive optimization anticipates growth and usage fluctuations. Administrators employ techniques such as caching, query optimization, and load redistribution to maintain responsiveness under varying workloads. This ensures that enterprise applications and business processes perform efficiently without degradation during peak demand periods.
Knowledge Integration for Exam Readiness
Candidates preparing for certification exams must integrate practical experience with theoretical knowledge. Hands-on practice in installing, configuring, and administering both WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 is essential.
Exam readiness involves understanding Java Enterprise Edition, Service-Oriented Architecture principles, web application deployment, and security best practices. Familiarity with command-line interfaces, scripting, monitoring tools, and troubleshooting methodologies enhances both practical competency and exam performance. A structured study approach that combines experience, conceptual understanding, and scenario-based practice ensures comprehensive preparation.
Foundational Competencies for Certification
Prior to attempting certification, candidates should cultivate foundational skills in operating systems, network administration, security principles, and application server management. Knowledge of web application architecture, Java Enterprise Edition, and command-line scripting provides a solid base for advanced administration tasks.
These competencies enable candidates to approach complex operational challenges with confidence. A deep understanding of system interdependencies, resource management, and performance tuning prepares administrators to excel in both certification assessments and real-world enterprise environments.
Continuous Learning and Skill Enhancement
System administration is a dynamic field, requiring continuous learning to keep pace with evolving technologies. Administrators must stay informed about updates to IBM Business Process Manager Advanced V8.5, WebSphere Application Server Network Deployment, and related infrastructure components.
Engaging in ongoing skill enhancement, exploring new automation techniques, and refining troubleshooting methodologies ensures sustained operational excellence. Continuous learning enables administrators to implement best practices, adapt to emerging challenges, and maintain high standards of system performance, security, and reliability.
Advanced Integration Techniques
Integration is a pivotal aspect of administering IBM Business Process Manager Advanced V8.5 within enterprise environments. Administrators must ensure seamless connectivity between business process management components and diverse back-end systems such as databases, messaging platforms, ERP systems, and web services. Mastery of integration techniques requires understanding communication protocols, transactional integrity, and potential failure points.
Effective integration involves establishing reliable connections, validating data flow, and monitoring performance metrics. Administrators must troubleshoot issues such as message delays, failed transactions, or data inconsistencies. By employing detailed log analysis, performance monitoring, and error tracing, they can pinpoint root causes and implement corrective measures efficiently. Maintaining transactional consistency across disparate systems is crucial for operational reliability.
Advanced Troubleshooting Strategies
Troubleshooting in complex enterprise environments demands both analytical and systematic approaches. Administrators must diagnose issues spanning server failures, process execution anomalies, and integration malfunctions. This requires comprehensive understanding of both WebSphere Application Server Network Deployment and IBM Business Process Manager Advanced V8.5 environments.
Root cause analysis often begins with examining system logs, tracing transaction flows, and identifying abnormal metrics. Administrators employ diagnostic tools and monitoring dashboards to detect bottlenecks, misconfigurations, or failures in interdependent systems. Effective troubleshooting not only resolves immediate problems but also informs preventive strategies, reducing the recurrence of similar issues and improving long-term operational stability.
Load Balancing and Cluster Optimization
Clusters are essential for high availability and system scalability. Administrators must configure nodes to ensure proper workload distribution, session replication, and failover capability. Load balancing is implemented to evenly allocate resources across servers, preventing individual nodes from becoming overburdened.
Cluster optimization includes adjusting replication domains, tuning session persistence, and monitoring node health. Administrators analyze traffic patterns, resource utilization, and process execution times to refine configurations. Effective cluster management enhances system responsiveness, maintains uptime, and supports seamless business process execution even under high-load scenarios.
Resource Management and Capacity Planning
Efficient resource management is fundamental for sustaining performance in enterprise environments. Administrators monitor CPU usage, memory allocation, disk I/O, and network bandwidth to ensure optimal utilization. They also implement proactive strategies to anticipate workload increases and adjust configurations accordingly.
Capacity planning is intertwined with resource management. Administrators forecast future demands based on historical trends, business growth, and system performance metrics. Strategies may include adding cluster nodes, redistributing workloads, or adjusting thread pools. Accurate capacity planning ensures that environments can handle growth without performance degradation or operational disruption.
Performance Monitoring and Optimization
Administrators must continuously monitor system performance to maintain operational efficiency. Metrics such as transaction throughput, response times, memory consumption, and CPU utilization provide insights into system health. Advanced monitoring involves real-time dashboards, historical trend analysis, and automated alerts to identify anomalies promptly.
Optimization strategies include tuning JVM settings, adjusting database connection pools, refining cache mechanisms, and configuring thread management parameters. Administrators must balance performance enhancements with resource efficiency to avoid over-provisioning. Regular performance reviews and adjustments enable the system to maintain high responsiveness under variable workloads.
Security Management and Policy Enforcement
Security administration is multifaceted, encompassing authentication, authorization, encryption, and monitoring for unauthorized activity. Administrators configure user roles, manage access permissions, and enforce policies that protect sensitive business process data.
Policy enforcement ensures compliance with organizational standards and regulatory mandates. Regular audits, vulnerability assessments, and security reviews are conducted to maintain a robust defense posture. Administrators must also implement proactive measures such as intrusion detection, secure configuration practices, and continuous monitoring to prevent breaches and ensure operational integrity.
Automation and Scripting for Efficiency
Automation enhances consistency, reduces human error, and streamlines administrative tasks. Administrators utilize scripting languages such as Jython and Jacl to automate configurations, deployments, monitoring, and maintenance routines.
Automated scripts can perform batch deployments across multiple servers, apply configuration changes uniformly, and monitor system health in real-time. By leveraging automation, administrators improve efficiency, minimize downtime, and ensure consistent operational practices across the enterprise environment. Orchestration further enhances these capabilities by coordinating sequences of automated tasks across interconnected systems.
Backup, Recovery, and Disaster Preparedness
Data protection and disaster recovery are critical responsibilities of administrators. Regular backups of configuration data, process artifacts, and critical system information are essential to ensure recoverability in the event of failure.
Disaster recovery planning includes establishing failover environments, validating recovery time objectives, and simulating recovery scenarios. Administrators ensure that both business continuity and system integrity are maintained during unplanned outages. The ability to recover quickly and reliably is a key differentiator for effective enterprise system administration.
Deployment Management and Environment Segregation
Deployment management is a sophisticated process involving the coordination of multiple environments such as development, test, staging, and production. Administrators ensure that each environment reflects consistent configurations, security policies, and integration points.
Segregation of environments allows administrators to validate processes, conduct performance testing, and identify potential issues without affecting live operations. Version control, automated deployment scripts, and environment-specific configurations are used to maintain consistency and traceability across deployments. This approach minimizes errors, reduces deployment risk, and supports smooth promotion of business processes through different stages.
Monitoring Business Process Performance
Administrators must closely observe business process execution to ensure efficiency and reliability. Key metrics include transaction throughput, process latency, error rates, and resource consumption. Monitoring dashboards provide real-time visibility into process behavior, enabling prompt intervention when anomalies occur.
Analysis of process performance helps administrators optimize execution, balance workloads, and enhance overall system efficiency. Proactive monitoring also supports predictive maintenance, allowing administrators to anticipate and mitigate potential performance issues before they impact business operations.
Advanced Troubleshooting and Diagnostic Techniques
In complex environments, troubleshooting extends beyond standard procedures. Administrators employ advanced techniques such as dependency tracing, process flow analysis, and correlation of system events to identify subtle issues.
Diagnostic tools enable deep inspection of server logs, transaction paths, and resource utilization patterns. By combining these insights with domain expertise, administrators can resolve intricate problems, optimize system behavior, and prevent recurring failures. Documentation of findings and corrective actions contributes to institutional knowledge and supports continuous improvement.
Exam Preparation and Skill Consolidation
Certification examinations test both practical skills and theoretical understanding. Candidates must demonstrate proficiency in installing, configuring, administering, and troubleshooting IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment.
Hands-on experience is essential for mastering deployment strategies, cluster management, resource optimization, and integration techniques. Preparation also involves understanding Java Enterprise Edition, Service-Oriented Architecture principles, security best practices, and monitoring strategies. Scenario-based practice enhances decision-making, problem-solving, and operational readiness.
Foundational Knowledge Reinforcement
Prior knowledge in operating systems, networking, web application architecture, and Java Enterprise Edition forms the foundation for advanced administration tasks. Understanding these concepts allows candidates to approach complex scenarios with confidence and competence.
Familiarity with scripting, security practices, and system monitoring complements foundational skills. Administrators can leverage these competencies to implement efficient deployments, optimize performance, and maintain robust, secure environments. Strengthening foundational knowledge supports both exam success and effective enterprise administration.
Continuous Improvement and Learning
The field of enterprise system administration is dynamic, with constant updates to software, infrastructure, and security requirements. Administrators must engage in continuous learning to stay abreast of technological advancements and evolving best practices.
Ongoing education involves exploring new automation techniques, performance optimization strategies, and advanced troubleshooting methodologies. Continuous skill enhancement ensures administrators maintain high operational standards, adapt to emerging challenges, and implement innovative solutions for complex enterprise environments.
Holistic System Administration
Holistic system administration requires administrators to maintain a comprehensive perspective on the interconnected components of enterprise environments. IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment V8.5.5 function as integrated ecosystems, and effective administration involves understanding dependencies between servers, processes, databases, and external services.
Administrators must balance operational efficiency, performance optimization, and security compliance simultaneously. By adopting a holistic approach, they can anticipate potential disruptions, streamline workflows, and maintain service continuity. This perspective ensures that all components function synergistically, enabling scalable and resilient enterprise operations.
Advanced Performance Tuning
Performance tuning in complex environments demands a nuanced understanding of both application behavior and system architecture. Administrators analyze CPU utilization, memory allocation, disk I/O, and network throughput to identify inefficiencies and optimize resource usage.
Tuning strategies include refining JVM configurations, adjusting thread pools, optimizing database connections, and implementing caching mechanisms. Administrators must also consider workload patterns, peak usage periods, and process execution characteristics to enhance responsiveness. Proactive performance tuning ensures that business processes execute efficiently while maintaining overall system stability.
Scalability and Capacity Planning
Scalability planning ensures that enterprise environments can accommodate growth in workloads, users, and process complexity. Administrators evaluate historical performance data, forecast future demands, and implement strategies to scale infrastructure effectively.
This may involve expanding cluster nodes, redistributing workloads, or refining load-balancing mechanisms. Capacity planning also considers storage, memory, and network resources to ensure sustained performance. By anticipating growth and scaling proactively, administrators prevent bottlenecks and maintain service reliability under fluctuating demand.
Cluster Health and High Availability
Clusters are central to high availability in enterprise deployments. Administrators configure cluster members to ensure session replication, failover capabilities, and balanced workloads. Regular health checks, monitoring alerts, and stress testing help maintain cluster integrity.
High availability strategies include redundancy planning, load distribution, and automated failover mechanisms. Administrators must verify that cluster nodes synchronize correctly and that transactional consistency is maintained during node failures or maintenance activities. This ensures uninterrupted service for critical business processes.
Security Hardening and Governance
Security hardening involves implementing measures beyond basic authentication and authorization. Administrators configure encryption protocols, enforce role-based access controls, and monitor system activities for anomalies. Regular vulnerability assessments and audits identify weaknesses before they can be exploited.
Governance practices ensure compliance with organizational policies and regulatory requirements. Administrators document configurations, enforce security standards, and maintain logs for audit purposes. Proactive security hardening protects sensitive data, mitigates risks, and preserves the integrity of enterprise systems.
Automation and Orchestration for Efficiency
Automation reduces human error, accelerates operations, and ensures consistency across environments. Administrators use Jython, Jacl, and other scripting tools to automate tasks such as configuration, deployment, monitoring, and maintenance.
Orchestration extends automation by coordinating multi-step processes across systems. Administrators design workflows to manage deployments, failovers, health checks, and updates systematically. By combining automation with orchestration, operational efficiency improves, downtime decreases, and administrative processes become predictable and reliable.
Advanced Troubleshooting and Incident Management
Complex environments require administrators to employ advanced troubleshooting methodologies. Incident management involves identifying, diagnosing, and resolving issues ranging from server errors and integration failures to performance degradation and security breaches.
Administrators utilize diagnostic tools, transaction tracing, log correlation, and monitoring dashboards to determine root causes. Structured documentation of incidents and solutions enhances organizational knowledge and prepares teams for future challenges. Proactive incident management minimizes downtime and ensures the continuous availability of critical business processes.
Integration Optimization
Administrators optimize integrations between IBM Business Process Manager Advanced V8.5 and back-end systems to enhance performance and reliability. This includes fine-tuning database connections, message queues, and web service endpoints.
Optimization requires analyzing transactional patterns, identifying latency bottlenecks, and ensuring data consistency across systems. Administrators may also implement caching strategies, query optimization, and resource throttling to maintain smooth communication between integrated components. Efficient integration reduces errors, accelerates process execution, and supports scalability.
Monitoring and Analytics
Advanced monitoring and analytics provide administrators with actionable insights into system health, process performance, and resource utilization. Real-time dashboards, historical trend analysis, and anomaly detection tools help identify deviations from expected behavior.
Administrators use analytics to optimize workload distribution, refine configurations, and anticipate potential failures. Proactive monitoring enables predictive maintenance, allowing administrators to resolve issues before they impact operations. Integrating analytics into administration enhances decision-making, operational efficiency, and business process reliability.
Deployment Lifecycle Management
Managing the deployment lifecycle requires administrators to oversee the promotion of business processes through development, test, staging, and production environments. Each stage must maintain configuration consistency, integration integrity, and security compliance.
Version control, automated deployment scripts, and validation procedures reduce errors and streamline transitions. Administrators ensure that processes are fully tested, dependencies are resolved, and performance criteria are met before promotion. Lifecycle management supports reliable process execution and minimizes operational risks.
Disaster Recovery and Business Continuity
Disaster recovery planning is essential for protecting enterprise operations from unexpected failures. Administrators implement backup strategies, redundant environments, and failover mechanisms to safeguard critical business data and system configurations.
Business continuity plans define recovery procedures, establish recovery time objectives (RTO), and ensure seamless resumption of services. Regular testing of recovery scenarios validates effectiveness, while continuous refinement addresses emerging risks. Effective disaster recovery safeguards organizational assets and maintains operational resilience under adverse conditions.
Exam Readiness and Skill Consolidation
Certification examinations assess both practical competencies and theoretical knowledge. Candidates must demonstrate proficiency in installation, configuration, administration, troubleshooting, performance optimization, and security management for IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment.
Preparation involves hands-on practice, scenario simulations, and comprehensive review of system administration principles. Candidates should focus on deployment strategies, cluster management, integration, automation, monitoring, and troubleshooting. Consolidating skills across these domains ensures readiness for certification and effective real-world administration.
Foundational Knowledge and Continuous Learning
Candidates should reinforce foundational knowledge in operating systems, network administration, Java Enterprise Edition, and web application architecture. Mastery of these concepts underpins advanced administrative tasks and problem-solving capabilities.
Continuous learning is essential for administrators to remain current with evolving technologies, emerging best practices, and software updates. Engaging in professional development, exploring new tools, and refining operational strategies supports sustained excellence and adaptability in dynamic enterprise environments.
Advanced Security and Compliance
Administrators implement comprehensive security measures to protect sensitive information and maintain compliance with industry standards. This includes configuring encryption, role-based access control, network segmentation, and auditing procedures.
Compliance activities involve monitoring adherence to regulatory requirements, maintaining detailed documentation, and conducting periodic reviews. Administrators proactively address vulnerabilities, ensuring that security policies remain effective and aligned with organizational objectives. Strong security and compliance practices preserve system integrity and support operational resilience.
Holistic Enterprise Management
Holistic management encompasses the full spectrum of administrative responsibilities, integrating performance, security, availability, scalability, and operational efficiency. Administrators must coordinate processes, resources, and monitoring mechanisms to achieve optimal enterprise performance.
This approach involves balancing competing priorities, anticipating system demands, and proactively mitigating risks. Holistic management ensures that IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment environments operate harmoniously, supporting organizational goals and business continuity.
Performance Benchmarking and Optimization
Administrators conduct performance benchmarking to establish baseline metrics for system throughput, response times, and resource utilization. These benchmarks guide optimization efforts and provide a reference for evaluating the impact of configuration changes, software updates, or workload increases.
Optimization efforts include refining process execution, adjusting resource allocations, and tuning infrastructure components. Continuous benchmarking enables administrators to identify trends, detect anomalies, and implement improvements that sustain high levels of system performance.
The administration of IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment V8.5.5 demands a sophisticated combination of technical expertise, analytical reasoning, and strategic foresight. Administrators must manage installation, configuration, integration, performance tuning, security, automation, monitoring, troubleshooting, scalability, and disaster recovery effectively.
Certification validates that candidates possess the knowledge, skills, and practical experience required to maintain resilient, secure, and high-performing enterprise environments. Mastery of these competencies ensures operational continuity, business process efficiency, and alignment with organizational objectives, establishing administrators as indispensable contributors to enterprise technology success.
Conclusion
The administration of IBM Business Process Manager Advanced V8.5 and WebSphere Application Server Network Deployment V8.5.5 represents a multifaceted discipline requiring both deep technical expertise and strategic foresight. The comprehensive coverage highlighted the full spectrum of responsibilities that system administrators, architects, and integrators undertake to ensure enterprise environments remain efficient, resilient, and secure. Key areas of focus included installation, configuration, deployment, and topology selection, emphasizing the critical importance of well-structured environments and thoughtful planning. Administrators must skillfully integrate business process management systems with diverse back-end resources, maintain high availability through clustering and load balancing, and optimize system performance to accommodate fluctuating workloads. Advanced troubleshooting, diagnostic analysis, and performance tuning are vital for sustaining operational continuity, while rigorous security measures and governance practices protect sensitive data and ensure regulatory compliance. Automation and scripting, alongside orchestration, enhance efficiency, reduce human error, and standardize administrative processes across complex environments.
Foundational knowledge in operating systems, network administration, Java Enterprise Edition, and web application architecture forms the backbone of effective administration, while continuous learning ensures adaptability to evolving technologies and enterprise demands. Ultimately, certification validates that professionals possess the practical skills, theoretical knowledge, and problem-solving capabilities required to administer large-scale, enterprise-grade systems. Mastery of these competencies not only maintains operational stability but also enhances business process efficiency, scalability, and security, positioning certified administrators as indispensable contributors to organizational success in complex technological landscapes.
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How often do you update the questions?
Testking strives to provide you with the latest questions in every exam pool. Therefore, updates in our exams/questions will depend on the changes provided by original vendors. We update our products as soon as we know of the change introduced, and have it confirmed by our team of experts.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.


