Exam Code: 2V0-13.25
Exam Name: VMware Cloud Foundation 9.0 Architect
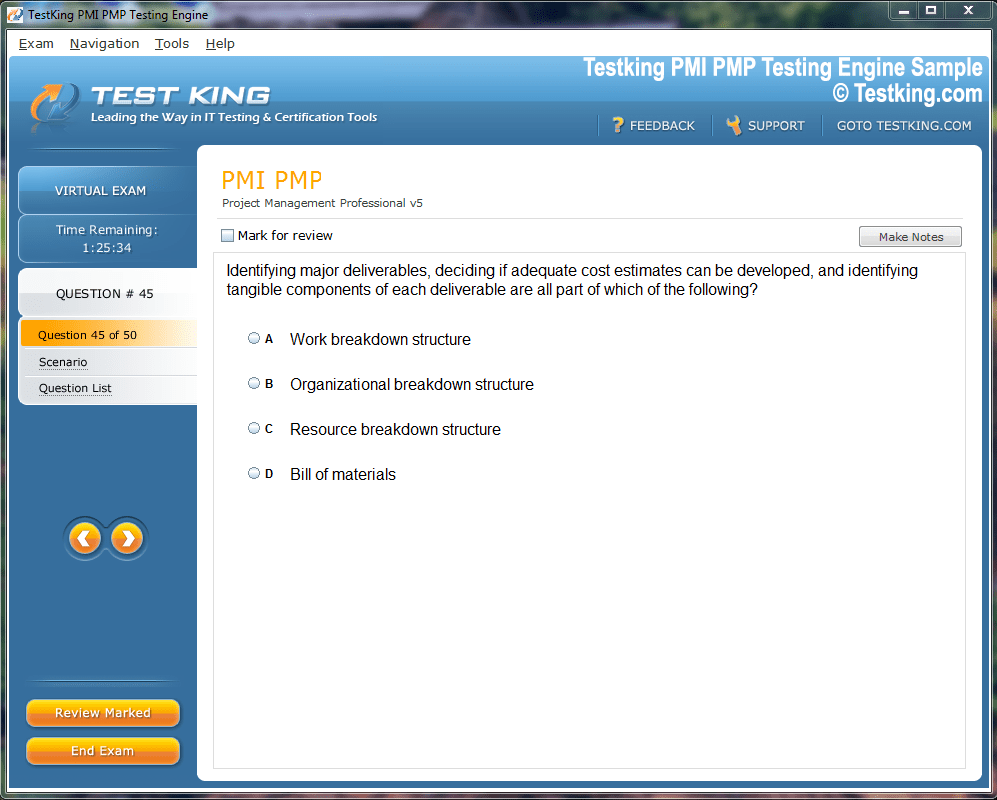
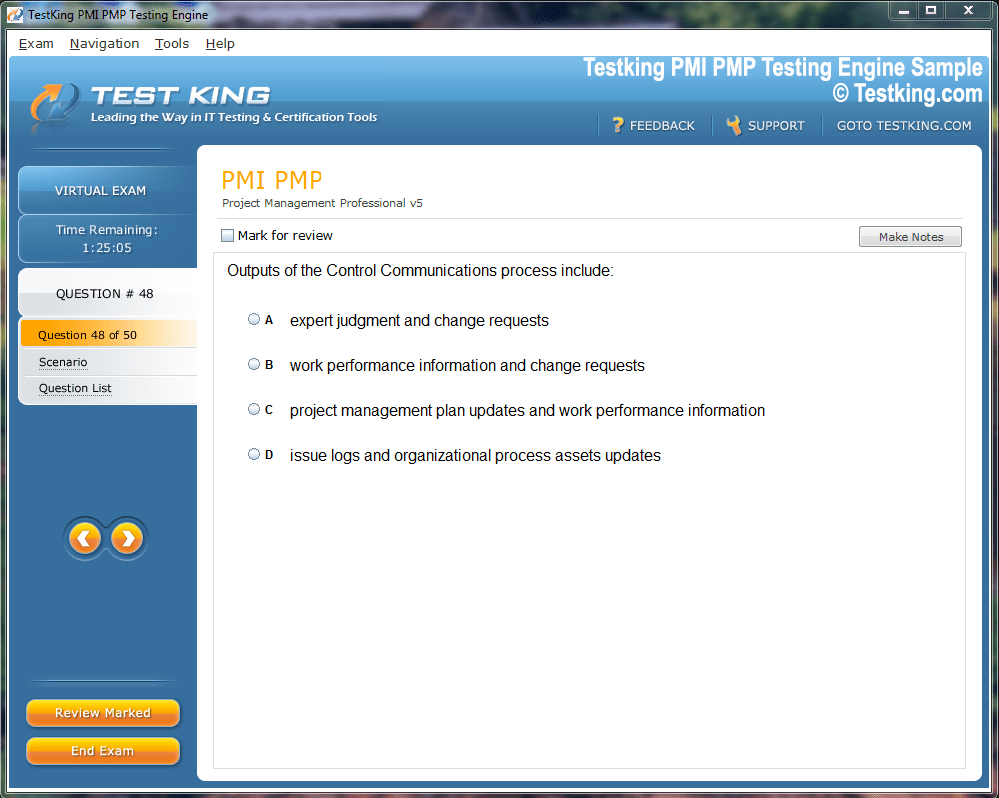
Product Screenshots
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our 2V0-13.25 testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.
Top VMware Exams
- 2V0-17.25 - VMware Cloud Foundation 9.0 Administrator
- 2V0-13.25 - VMware Cloud Foundation 9.0 Architect
- 2V0-21.23 - VMware vSphere 8.x Professional
- 2V0-16.25 - VMware vSphere Foundation 9.0 Administrator
- 2V0-15.25 - VMware Cloud Foundation 9.0 Support
- 3V0-21.25 - Advanced VMware Cloud Foundation 9.0 Automation
- 2V0-41.24 - VMware NSX 4.X Professional V2
- 3V0-21.23 - VMware vSphere 8.x Advanced Design
- 2V0-11.25 - VMware Cloud Foundation 5.2 Administrator
- 1V0-21.20 - Associate VMware Data Center Virtualization
- 2V0-72.22 - Professional Develop VMware Spring
- 2V0-51.23 - VMware Horizon 8.x Professional
- 2V0-32.24 - VMware Cloud Operations 8.x Professional
Mastering vCenter Server Deployment and Management for VMware 2V0-13.25 Certification
The virtualization industry continues to evolve at a remarkable pace, and professionals who hold recognized credentials validating their expertise in enterprise virtualization platforms consistently find themselves at a distinct advantage in competitive job markets. The VMware 2V0-13.25 certification, which focuses on vCenter Server deployment and management, represents one of the most practically valuable credentials available to infrastructure engineers, systems administrators, and virtualization architects working in modern enterprise environments. VMware's virtualization platform underpins the data center operations of organizations across virtually every industry, and professionals who can demonstrate certified expertise in managing this platform are in consistently high demand.
vCenter Server sits at the heart of VMware's virtualization ecosystem as the centralized management platform through which administrators oversee virtual machine lifecycle, resource allocation, high availability configurations, and security policy enforcement across entire virtualized infrastructure environments. The depth of knowledge required to deploy, configure, and manage vCenter Server effectively in production enterprise environments is substantial, and the 2V0-13.25 certification validates that a professional has achieved this depth of understanding through a rigorous examination process. For professionals committed to building careers in enterprise infrastructure, virtualization, and cloud management, this certification provides the credential that transforms demonstrated competence into recognized professional qualification that employers trust and reward.
Exploring the Foundational Architecture of vCenter Server and Its Role Within VMware Infrastructure Ecosystems
Before diving into examination-specific preparation, candidates must develop a thorough understanding of what vCenter Server is, how it fits within the broader VMware infrastructure ecosystem, and why its architecture is designed the way it is. vCenter Server provides centralized management for ESXi hosts and the virtual machines running on them, enabling administrators to manage resources across multiple physical hosts as a unified pool rather than managing each host independently. This centralized management capability is what transforms individual ESXi hosts from standalone virtualization platforms into a coordinated, enterprise-grade infrastructure that can support sophisticated workload management, high availability, and disaster recovery capabilities.
The vCenter Server Appliance represents the current deployment model for vCenter Server, replacing the older Windows-based installation with a purpose-built Linux-based virtual appliance that provides improved performance, simplified deployment, and reduced dependency on external infrastructure components. Understanding the VCSA architecture including its embedded Platform Services Controller, integrated PostgreSQL database, and built-in update mechanisms is foundational knowledge that the 2V0-13.25 examination tests extensively. Candidates must understand not just how to deploy the VCSA but why its architecture is designed the way it is, what trade-offs different deployment configurations involve, and how architectural decisions made during initial deployment affect operational capabilities and scalability over the long-term lifecycle of the vCenter Server installation.
Examining the Detailed Domain Structure and Topic Coverage of the 2V0-13.25 Examination Blueprint
The 2V0-13.25 examination blueprint defines the specific topics and competencies that candidates must master to pass the certification examination, and studying this blueprint carefully before beginning preparation is one of the most strategically important steps any candidate can take. The examination covers several major domain areas including vCenter Server architecture and deployment, configuration and administration of vCenter Server components, virtual machine management, resource management and optimization, high availability and fault tolerance configurations, security and compliance implementations, and monitoring and troubleshooting methodologies. Each domain represents a genuine area of operational expertise that vCenter administrators encounter in their daily professional practice.
The examination blueprint not only identifies topics but also indicates the depth of knowledge expected in each area, distinguishing between topics requiring awareness-level familiarity and those requiring the ability to configure, troubleshoot, and optimize in complex scenarios. Candidates who align their study efforts with the blueprint's emphasis on different topic areas avoid the common preparation mistake of spending disproportionate time on comfortable topics while neglecting challenging areas that carry significant examination weight. Downloading the official examination blueprint from VMware's education portal and using it as the master outline for your study plan is an essential foundation of effective preparation that separates strategically prepared candidates from those who study without clear directional guidance.
Mastering vCenter Server Appliance Deployment Processes Including Installation Configuration and Initial Setup
The deployment of vCenter Server Appliance is a multi-stage process that requires careful planning, prerequisite verification, and methodical execution to produce a stable and fully functional management platform. The VCSA installation process uses a graphical installer that guides administrators through deployment configuration including target ESXi host selection, virtual machine sizing based on expected environment scale, network configuration, and SSO domain setup. Candidates must understand each stage of this installation process in detail, including the specific parameters that must be configured, the common errors that occur when prerequisites are not met, and the validation steps that confirm a successful deployment before the vCenter Server is placed into production service.
Network configuration during VCSA deployment deserves particular attention because errors in network setup during installation can prevent the vCenter Server from being reachable or functioning correctly after deployment completes. Candidates must understand the network requirements for VCSA including the distinction between the management network and other network interfaces, the DNS resolution requirements that must be satisfied before deployment begins, and the firewall port requirements that must be addressed in the network environment surrounding the deployed appliance. The vCenter Server management interface, accessible through the VAMI on port 5480, provides post-deployment configuration and management capabilities that candidates must also understand thoroughly as part of the complete VCSA deployment and management knowledge domain.
Developing Deep Expertise in vSphere Single Sign-On Configuration and Identity Source Management
VMware vSphere Single Sign-On represents one of the most architecturally significant components of the vCenter Server platform, providing the authentication infrastructure through which all administrative access to vCenter and its connected services is managed. SSO eliminates the need for separate authentication to each component of the vSphere environment by providing a centralized token-based authentication service that validates user identities once and then issues tokens that grant access to connected services throughout the authenticated session. The 2V0-13.25 examination tests SSO knowledge extensively because misconfigurations in this component can affect the security and accessibility of the entire vSphere management infrastructure.
Identity source configuration within SSO determines where vCenter Server looks for user accounts and groups that can be granted access to vSphere resources. The default vsphere.local domain provides a built-in identity source for local vSphere-specific accounts, but most enterprise deployments integrate SSO with Active Directory or LDAP identity sources to allow existing organizational user accounts to authenticate to vCenter. Candidates must understand the process of adding identity sources, the difference between Active Directory integrated authentication and Active Directory over LDAP, and the troubleshooting approaches for resolving authentication failures that stem from identity source configuration problems. Password policies, lockout policies, and token lifetime configurations within SSO represent additional topics that the examination addresses and that candidates must understand from both a security and operational perspective.
Understanding vCenter Server Permission Model and Role Based Access Control Implementation
Access control in vCenter Server is implemented through a permission model that combines roles, which define what actions can be performed, with objects in the vSphere inventory hierarchy, which define where those actions can be performed. A permission is the combination of a user or group, a role, and an inventory object, and it grants the specified principal the ability to perform the actions defined by the role on the specified object and, optionally, all objects contained within it through propagation. This hierarchical permission model provides tremendous flexibility for implementing least-privilege access control across complex vSphere environments with multiple administrators having different scopes of responsibility.
VMware provides a comprehensive set of predefined system roles that cover the most common administrative access requirements, ranging from the Administrator role that grants full access to read-only roles that permit viewing without modification. Custom roles allow organizations to create precisely tailored permission sets that grant only the specific privileges required for particular administrative functions. Candidates must understand not just how to create and assign roles and permissions but also the inheritance behavior that propagates permissions down the inventory hierarchy, the override behavior that allows child object permissions to differ from parent permissions, and the global permissions mechanism that grants access across all inventory objects regardless of hierarchy position. These nuances of the permission model are frequently tested through scenario-based examination questions that require candidates to determine the correct permission configuration for a described access control requirement.
Configuring and Managing vCenter Server High Availability to Ensure Continuous Management Platform Availability
vCenter Server High Availability provides a native mechanism for protecting the vCenter Server management platform itself against failures that would otherwise result in a complete loss of centralized management capability. vCenter HA creates a cluster of three vCenter Server nodes — an active node that handles all management traffic under normal conditions, a passive node that maintains a continuously synchronized copy of the active node's state and takes over management functions within seconds of an active node failure, and a witness node that participates in the cluster quorum to prevent split-brain scenarios when network partitions occur between the active and passive nodes.
Configuring vCenter HA requires careful network planning because the HA cluster uses a dedicated HA network for replication traffic between nodes that must be separate from the management network used by administrators and other vSphere components. Candidates must understand the network requirements, the configuration process for enabling and joining vCenter HA nodes, the monitoring capabilities that indicate cluster health, and the procedures for performing planned failovers when maintenance on the active node is required. The examination also tests understanding of the limitations of vCenter HA, including the types of failures it protects against versus the failure scenarios where other recovery approaches are required. Understanding vCenter HA in the context of the broader business continuity and disaster recovery strategy for the management infrastructure is important for answering scenario-based examination questions correctly.
Learning Virtual Machine Lifecycle Management Including Creation Configuration Migration and Snapshot Operations
Virtual machine lifecycle management represents one of the most operationally significant areas of vCenter Server administration and receives substantial coverage in the 2V0-13.25 examination. The complete virtual machine lifecycle encompasses creation from templates or from scratch, configuration of hardware resources and advanced settings, operational management including power operations and guest OS customization, migration between hosts and datastores using vMotion and Storage vMotion, and eventual decommissioning through archival or deletion. Candidates must understand each phase of this lifecycle and the vCenter Server capabilities that support efficient management of virtual machines through each stage.
Virtual machine templates and content libraries provide the mechanisms through which organizations standardize virtual machine deployment and maintain libraries of approved configuration baselines. Candidates must understand how to create and manage templates, how content libraries enable sharing of template resources across vCenter Server instances and locations, and how customization specifications automate the guest operating system configuration that occurs when virtual machines are deployed from templates. Snapshot management is another operationally important area that the examination tests thoroughly, including the performance and storage implications of snapshot chains, the proper use cases for snapshots versus other backup mechanisms, and the procedures for creating, reverting, and deleting snapshots safely in production environments.
Implementing Resource Management Capabilities Including Resource Pools DRS and Storage Policies
Effective resource management is one of the primary value propositions of vCenter Server as a centralized management platform, and the 2V0-13.25 examination tests resource management knowledge extensively. Resource pools provide a mechanism for organizing virtual machines into logical groups that share a defined allocation of CPU and memory resources from the underlying ESXi host or cluster. Understanding how resource pool reservations, limits, and shares interact to determine how resources are allocated during contention is essential knowledge that the examination tests through computational and scenario-based questions.
vSphere Distributed Resource Scheduler automates the placement and migration of virtual machines across ESXi hosts within a cluster to optimize resource utilization and balance workload distribution. Candidates must understand DRS automation levels from fully automated through manual, the migration threshold settings that determine how aggressively DRS migrates virtual machines in response to imbalances, and the DRS rules that can pin virtual machines to specific hosts or require that certain virtual machines run on separate hosts for availability or licensing reasons. Storage policy based management provides the framework through which storage requirements for virtual machines are expressed as policies rather than direct datastore assignments, enabling vCenter to automatically place and migrate virtual machines to datastores that satisfy their defined storage requirements. Understanding SPBM in conjunction with vSAN and other storage platforms reflects an important area of modern vSphere storage management that the examination addresses.
Mastering vSphere Networking Concepts Including Distributed Switches and Advanced Network Configurations
Networking within a vSphere environment managed by vCenter Server involves concepts and capabilities that extend well beyond basic virtual switch configuration. vSphere Distributed Switches provide a centralized networking management model where the network configuration is defined once at the vCenter Server level and then applied consistently across all ESXi hosts that are members of the distributed switch. This centralized model dramatically simplifies network management in large environments and enables advanced capabilities including network I/O control, port mirroring, and NetFlow that are not available with standard virtual switches managed at the individual host level.
Candidates must understand the architecture of vSphere Distributed Switches including the distinction between the distributed switch object managed in vCenter and the hidden proxy switches that exist on each participating ESXi host. Port groups on distributed switches define the network configuration that virtual machines and VMkernel adapters connect to, and candidates must understand how to configure VLAN settings, traffic shaping policies, security policies, and teaming and failover configurations on distributed port groups. The migration process for moving ESXi hosts and their networking from standard switches to distributed switches is a common operational task that the examination tests through procedural questions. Network I/O control represents an advanced distributed switch capability that candidates must understand for managing network bandwidth allocation across different traffic types in environments where network saturation could affect the performance of critical workloads.
Understanding vCenter Server Backup Recovery and Database Maintenance Operations
Protecting the vCenter Server configuration and database through regular backup operations is a fundamental operational responsibility that the 2V0-13.25 examination addresses as an important management knowledge area. The VCSA includes a built-in backup capability accessible through the VAMI that creates file-based backups of the vCenter Server configuration and database, which can be stored on a variety of network-accessible destinations including FTP, FTPS, HTTP, HTTPS, and SCP targets. Candidates must understand how to configure scheduled backups, what is included and excluded from VCSA file-based backups, and how to perform a restoration from backup when vCenter Server recovery is required.
Database maintenance considerations for vCenter Server include understanding how the embedded PostgreSQL database grows over time as historical performance data, events, and tasks accumulate, and how database size affects vCenter Server performance and backup duration. The vCenter Server statistics collection levels determine how much performance history data is retained and at what granularity, and candidates must understand the trade-offs between retaining detailed historical performance data and the database growth and performance implications of higher statistics collection levels. Restoration procedures for vCenter Server from file-based backups require candidates to understand the complete process from deploying a fresh VCSA through the restoration of backed-up configuration data, a process that the examination may test through procedural scenario questions that require knowledge of each step in the correct sequence.
Implementing Security Hardening and Compliance Configurations Across the vSphere Management Environment
Security hardening of vCenter Server and the broader vSphere environment is an increasingly important operational discipline as organizations face growing regulatory requirements and sophisticated threat landscapes targeting virtualization infrastructure. VMware publishes official security hardening guides for each version of vSphere that provide specific configuration recommendations for reducing the attack surface of ESXi hosts, vCenter Server, and virtual machines. Candidates preparing for the 2V0-13.25 examination must be familiar with the categories of hardening recommendations and understand the technical rationale behind the most important configuration changes recommended in these guides.
Certificate management represents a particularly important security topic within the vCenter Server domain. vCenter Server uses TLS certificates to secure communications between its components and between clients and the management platform, and the default behavior is to issue certificates from the VMware Certificate Authority built into vCenter. Candidates must understand the VMCA certificate model, the options for replacing VMCA-issued certificates with certificates from an external enterprise or public certificate authority, and the procedures for renewing expiring certificates before they cause service disruptions. Audit logging configuration, including the settings that determine what administrative actions are recorded in the vCenter Server event log, and the integration of vCenter logging with external security information and event management platforms, represents another security topic that examination candidates must understand from both a configuration and a compliance perspective.
Developing Comprehensive Monitoring and Troubleshooting Skills for vCenter Server and vSphere Environments
Effective monitoring and troubleshooting are among the most practically valuable skills a vCenter administrator can possess, and the 2V0-13.25 examination tests these capabilities extensively through scenario-based questions that present described symptoms and ask candidates to identify likely causes and appropriate resolution steps. vCenter Server provides multiple monitoring interfaces including the performance charts and dashboards built into the vSphere Client, the log files accessible through the VAMI and through direct access to the VCSA file system, and integration points with external monitoring platforms through APIs and log forwarding mechanisms.
Understanding the vCenter Server log file structure and knowing where to find relevant diagnostic information for different types of issues is essential troubleshooting knowledge that the examination tests. The vpxd.log file records the core vCenter Server daemon activity and is typically the first place administrators look when investigating vCenter Server behavioral problems. The VAMI provides access to service status information and allows administrators to start, stop, and restart individual vCenter Server services when troubleshooting service-specific failures. The vSphere Client health status dashboards provide at-a-glance visibility into the health of vCenter Server components and connected ESXi hosts. Candidates who develop genuine troubleshooting methodology through hands-on practice with real vCenter Server environments will consistently outperform those who study troubleshooting procedures purely through reading, because effective troubleshooting requires developing the pattern recognition and systematic elimination skills that only direct experience cultivates.
Selecting Appropriate Study Resources and Building an Effective Laboratory Environment for Hands-On Practice
The quality of study resources and the availability of hands-on laboratory practice are the two factors that most significantly influence preparation outcomes for the 2V0-13.25 examination. VMware's official documentation, including the vCenter Server installation and configuration guide and the vSphere administration documentation, represents the most authoritative reference available and should form the foundation of any candidate's study resource collection. VMware also offers official training courses delivered through its authorized training centers and through its online learning platform that provide structured instruction aligned with examination objectives.
Building a personal laboratory environment for hands-on practice is strongly recommended for candidates who do not have access to vCenter Server through their current employment. VMware provides a free trial of vCenter Server and ESXi through its evaluation program, and the hardware requirements for running a nested virtualization lab on a modern desktop or laptop computer are achievable for most candidates. VMware Hands-on Labs provides free browser-based access to pre-configured vSphere lab environments that allow candidates to practice specific administrative tasks without requiring any local hardware or software installation. Combining structured study of official documentation and training materials with regular hands-on practice in a laboratory environment produces the depth of understanding and practical familiarity that the 2V0-13.25 examination demands and that genuine professional competence in vCenter Server administration requires.
Conclusion
Mastering vCenter Server deployment and management for the VMware 2V0-13.25 certification is a substantial undertaking that rewards professionals who approach it with genuine commitment, strategic preparation, and consistent hands-on practice. The certification validates a comprehensive and practically valuable set of skills spanning vCenter Server architecture, deployment, security, resource management, high availability, and troubleshooting that organizations urgently need from the infrastructure professionals they employ and trust with their virtualized environments. Candidates who invest in official study resources, build laboratory environments where they can develop real operational familiarity with vCenter Server capabilities, and approach their preparation with the methodical discipline that complex technical subject matter demands will emerge from the process as substantially more capable and professionally credible virtualization administrators. The career benefits of earning this certification are concrete and meaningful, from qualifying for senior infrastructure roles to commanding higher compensation and building the technical credibility that positions professionals for advancement into architecture and technical leadership positions. The knowledge developed through 2V0-13.25 preparation extends well beyond examination day and continues delivering value throughout every aspect of a rewarding career in enterprise virtualization and cloud infrastructure management.