Certification: CCAK
Certification Full Name: Certificate of Cloud Auditing Knowledge
Certification Provider: Isaca
Exam Code: CCAK
Exam Name: Certificate of Cloud Auditing Knowledge
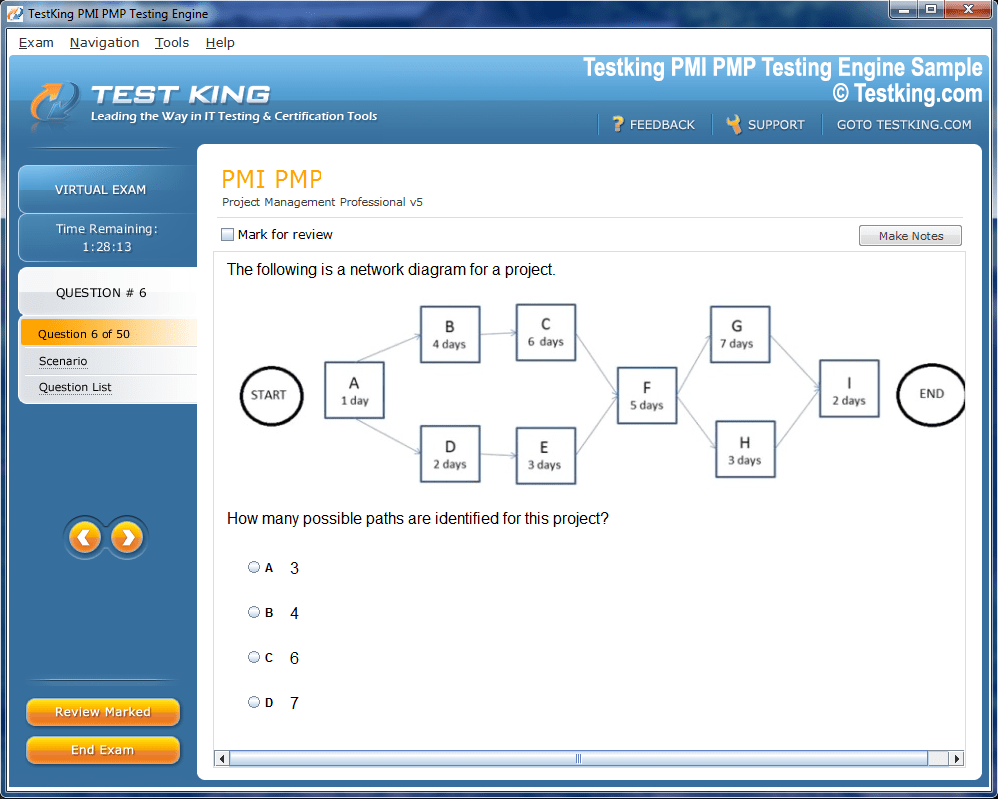
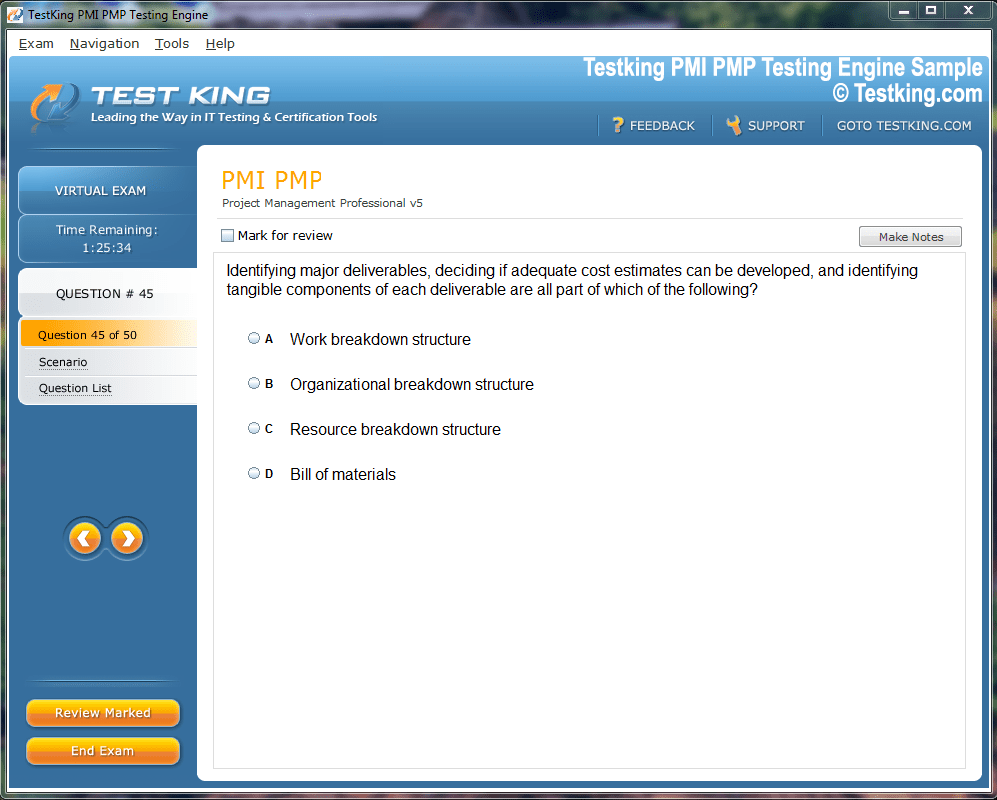
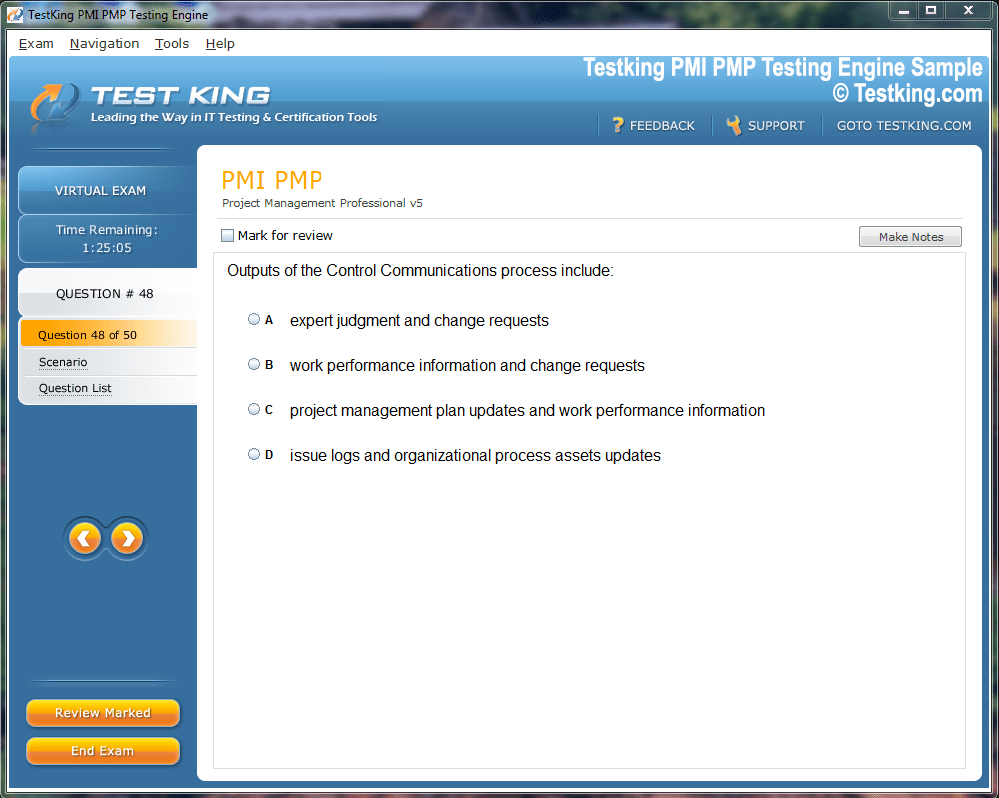
Product Screenshots
nop-1e =1
CCAK Certification: Your Strategic Path to Cloud Security Auditing Excellence
The digital transformation era has fundamentally reshaped how organizations approach information security, with cloud computing emerging as the dominant infrastructure paradigm. As enterprises increasingly migrate their critical assets and operations to cloud environments, the demand for professionals who can effectively audit and assess cloud security controls has reached unprecedented levels. The Certificate of Cloud Auditing Knowledge represents a distinguished credential specifically designed to validate expertise in examining cloud-based systems, evaluating compliance frameworks, and ensuring robust security postures across multi-cloud architectures.
This comprehensive certification journey equips aspiring cloud auditors with specialized knowledge spanning governance structures, risk management methodologies, compliance requirements, and technical security controls unique to cloud environments. Unlike traditional information security certifications that focus broadly on cybersecurity principles, this credential concentrates exclusively on the nuances of auditing cloud infrastructure, platforms, and software services. Professionals pursuing this qualification develop sophisticated capabilities in assessing vendor security claims, evaluating shared responsibility models, examining data protection mechanisms, and verifying compliance with industry-specific regulations across diverse cloud deployment scenarios.
The certification curriculum addresses critical competencies required for modern cloud auditing professionals, including understanding various service models, deployment architectures, virtualization technologies, orchestration platforms, and emerging technologies like containers and serverless computing. Candidates explore methodologies for conducting comprehensive cloud audits, developing risk-based audit programs, executing effective audit procedures, documenting findings systematically, and communicating results to technical and executive stakeholders. This specialized knowledge becomes increasingly valuable as organizations grapple with complex challenges surrounding data sovereignty, regulatory compliance, vendor lock-in risks, and the evolving threat landscape targeting cloud environments.
The Strategic Importance of Cloud Auditing Expertise
Organizations worldwide continue accelerating their cloud adoption strategies, driven by compelling advantages including scalability, cost optimization, operational agility, and access to innovative services. However, this migration introduces substantial security and compliance challenges that traditional audit approaches inadequately address. Cloud environments operate fundamentally differently from conventional on-premises infrastructure, featuring dynamic resource allocation, shared multi-tenant architectures, distributed data storage, complex access control models, and intricate supply chain relationships with cloud service providers.
These distinctive characteristics necessitate specialized audit methodologies and technical competencies that conventional information technology auditors may lack. Cloud auditing professionals must navigate complex shared responsibility frameworks where security obligations distribute between cloud providers and customer organizations based on specific service models. They evaluate whether organizations properly configure cloud-native security controls, implement appropriate identity and access management policies, maintain visibility across distributed environments, and establish effective governance structures for cloud operations.
The proliferation of regulatory requirements specifically addressing cloud computing further amplifies the need for specialized auditing expertise. Frameworks like the General Data Protection Regulation, Health Insurance Portability and Accountability Act, Payment Card Industry Data Security Standard, Federal Risk and Authorization Management Program, and numerous industry-specific compliance mandates impose stringent requirements on organizations leveraging cloud services. Auditors must possess detailed knowledge of these regulatory landscapes, understand how requirements apply across different cloud service models, and develop effective testing procedures to verify compliance in dynamic cloud environments.
Financial institutions, healthcare organizations, government agencies, retail enterprises, technology companies, and virtually every industry sector now depend heavily on cloud infrastructure to deliver critical services. These organizations require assurance that their cloud implementations maintain appropriate security controls, comply with applicable regulations, protect sensitive data, and align with organizational risk tolerances. Professionals holding specialized cloud auditing credentials provide this essential assurance, helping organizations identify vulnerabilities, address compliance gaps, optimize security investments, and build stakeholder confidence in cloud operations.
The strategic value of cloud auditing expertise extends beyond compliance verification. Skilled cloud auditors contribute significantly to organizational resilience by identifying architectural weaknesses, recommending security enhancements, evaluating disaster recovery capabilities, assessing business continuity preparedness, and providing insights that strengthen overall security postures. Their specialized knowledge helps organizations make informed decisions about cloud adoption strategies, vendor selections, security tool investments, and risk mitigation approaches that protect critical assets while enabling business innovation.
Comprehensive Examination of Certification Domains
The certification framework encompasses multiple interconnected knowledge domains that collectively prepare professionals for the multifaceted challenges of cloud auditing. Each domain addresses specific competencies essential for conducting thorough, effective audits of cloud environments while maintaining professional standards and delivering actionable insights to stakeholder communities.
Cloud Governance and Risk Management Principles
Effective cloud governance establishes the foundational structures, policies, and processes that guide organizational cloud adoption and ongoing operations. This domain explores frameworks for developing comprehensive cloud governance programs that align cloud strategies with business objectives, establish clear accountability structures, define decision-making authorities, and implement oversight mechanisms ensuring responsible cloud utilization. Auditors examine how organizations establish cloud governance committees, develop cloud adoption policies, create architectural standards, implement change management processes, and maintain continuous governance effectiveness as cloud environments evolve.
Risk management methodologies specific to cloud computing form another critical component within this domain. Cloud environments introduce unique risks including data residency concerns, vendor dependency vulnerabilities, multi-tenancy security implications, service availability dependencies, and potential compliance violations stemming from inadequate cloud configurations. Auditors learn systematic approaches for identifying these cloud-specific risks, assessing their potential impacts and likelihoods, evaluating existing risk mitigation controls, and recommending additional measures to maintain risks within acceptable tolerances.
The shared responsibility model represents a fundamental concept that auditors must thoroughly understand and evaluate during cloud assessments. This model delineates security responsibilities between cloud service providers and customer organizations, with specific boundaries varying based on whether organizations consume infrastructure, platform, or software services. Auditors examine whether organizations clearly understand their specific responsibilities under applicable shared responsibility frameworks, implement appropriate controls addressing their obligations, and maintain effective coordination with cloud providers regarding shared security concerns.
Cloud service agreements and contractual provisions receive significant attention within governance and risk management auditing. These legally binding documents establish performance expectations, security commitments, compliance responsibilities, data handling obligations, incident response procedures, and liability limitations governing provider-customer relationships. Auditors evaluate whether organizations negotiate appropriate contractual protections, verify provider compliance with contractual security commitments, monitor service level agreement performance, and maintain documentation supporting contractual compliance during regulatory examinations.
Third-party risk management becomes particularly complex in cloud environments where organizations often engage multiple service providers, each potentially utilizing additional subcontractors, creating intricate supply chain relationships. Auditors assess how organizations identify all parties within their cloud supply chains, evaluate security capabilities of each provider, monitor ongoing provider performance and security postures, respond to provider security incidents, and maintain appropriate oversight ensuring supply chain integrity throughout provider lifecycles.
Cloud Compliance and Regulatory Framework Navigation
The compliance landscape surrounding cloud computing encompasses numerous overlapping regulatory requirements, industry standards, contractual obligations, and internal policies that organizations must simultaneously satisfy. This certification domain equips auditors with detailed knowledge of major compliance frameworks specifically relevant to cloud environments, including how these frameworks apply differently across various cloud service and deployment models.
Data protection regulations fundamentally shape cloud compliance requirements, particularly for organizations handling personal information subject to privacy laws across multiple jurisdictions. Auditors examine provisions within regulations like the General Data Protection Regulation that specifically address cloud processing, including requirements for data processing agreements, limitations on international data transfers, obligations for security breach notifications, rights regarding data portability, and provisions governing automated decision-making systems. They assess whether organizations implement technical and organizational measures satisfying these regulatory requirements within their specific cloud environments.
Healthcare organizations leveraging cloud services must navigate complex requirements established by regulations protecting medical information confidentiality and integrity. Auditors familiar with healthcare compliance frameworks understand specific provisions addressing cloud service provider relationships, requirements for business associate agreements, technical safeguard specifications, audit control requirements, and breach notification obligations that apply when protected health information resides in cloud environments. They evaluate whether cloud implementations satisfy these stringent healthcare-specific requirements through appropriate contractual provisions, technical controls, and ongoing monitoring practices.
Financial services organizations face similarly rigorous compliance requirements when adopting cloud technologies. Banking regulations, securities laws, payment card industry standards, and anti-money laundering provisions all impose specific obligations regarding data security, operational resilience, outsourcing governance, and regulatory reporting that directly impact cloud implementations. Auditors assess whether financial institutions implement appropriate due diligence processes when selecting cloud providers, maintain sufficient operational control over outsourced functions, ensure data availability and integrity supporting regulatory reporting, and protect customer financial information according to applicable standards.
Government cloud implementations must satisfy specialized security and compliance frameworks designed to protect sensitive government information and critical national security systems. Auditors working with government clients understand authorization processes, continuous monitoring requirements, security control baselines, and specialized provisions addressing government data handling, clearance requirements, and physical location restrictions that apply to cloud services supporting government operations. They evaluate provider compliance with these government-specific frameworks and assess whether agencies properly implement security controls addressing their specific authorization requirements.
Industry-specific compliance standards beyond government, healthcare, and financial services also influence cloud implementations across numerous sectors. Auditors develop familiarity with standards addressing manufacturing, retail, education, telecommunications, energy, and other industries, understanding how sector-specific requirements apply to cloud environments serving these industries. This broad compliance knowledge enables auditors to provide valuable guidance regardless of the industries their audit clients serve.
Technical Security Controls in Cloud Architectures
Cloud computing platforms implement sophisticated technical security controls operating at infrastructure, platform, and application layers that auditors must thoroughly understand to conduct effective security assessments. This certification domain explores the technical architecture of cloud environments, security technologies protecting cloud resources, and methodologies for testing control effectiveness across various cloud service models.
Identity and access management systems form the cornerstone of cloud security architectures, controlling who can access cloud resources and what actions authorized users can perform. Auditors examine how organizations implement strong authentication mechanisms including multi-factor authentication, single sign-on systems, and privileged access management tools controlling administrative access to cloud environments. They evaluate access control policies ensuring least privilege principles, assess role-based access control implementations, verify separation of duties for sensitive operations, and examine logging and monitoring systems tracking authentication attempts and user activities.
Network security controls in cloud environments differ significantly from traditional perimeter-based approaches, requiring auditors to understand virtual networking concepts, software-defined networking capabilities, and cloud-native security tools. They assess implementations of virtual private clouds creating network isolation, evaluate network segmentation strategies limiting lateral movement between workloads, examine firewall rules controlling traffic flows, and verify proper configuration of network security groups, access control lists, and web application firewalls protecting cloud-hosted applications from external threats.
Data protection mechanisms receive intensive focus during cloud security audits given the criticality of maintaining data confidentiality, integrity, and availability across distributed cloud storage systems. Auditors evaluate encryption implementations protecting data at rest within cloud storage services, examine encryption key management practices ensuring cryptographic key security, assess transport encryption protecting data moving between cloud services and end users, and verify data classification schemes ensuring appropriate protection levels based on information sensitivity.
Virtualization security controls address risks specific to multi-tenant cloud environments where multiple customer workloads execute on shared physical infrastructure. Auditors examine hypervisor security configurations preventing virtual machine escape vulnerabilities, assess network isolation between tenant environments, evaluate resource allocation controls preventing denial of service conditions, and verify proper implementation of secure virtualization technologies ensuring workload isolation despite resource sharing.
Container security introduces additional considerations as organizations increasingly adopt containerized applications and orchestration platforms for cloud deployments. Auditors evaluate container image security including vulnerability scanning processes, assess runtime security controls protecting executing containers, examine orchestration platform security configurations, verify network policies controlling container communication, and evaluate secrets management approaches protecting sensitive configuration data consumed by containerized applications.
Serverless computing architectures present unique security considerations as organizations adopt function-as-a-service platforms eliminating traditional server management responsibilities. Auditors assess function-level access controls, examine event source security configurations, evaluate secrets management for serverless functions, verify logging and monitoring capabilities providing visibility into function executions, and assess dependency management practices addressing third-party library vulnerabilities in serverless applications.
Cloud Audit Methodologies and Execution Frameworks
Conducting effective cloud audits requires systematic methodologies adapted to address the unique characteristics of cloud environments while maintaining professional audit standards. This certification domain develops competencies in planning cloud audits, executing audit procedures, gathering appropriate evidence, documenting findings systematically, and communicating results effectively to diverse stakeholder audiences.
Audit planning for cloud environments begins with comprehensive risk assessments identifying significant risks warranting audit attention. Auditors learn to evaluate cloud-specific risk factors including data residency concerns, provider dependency risks, configuration complexity vulnerabilities, and regulatory compliance uncertainties. These risk assessments inform audit scope decisions, determine audit objectives, guide resource allocation, and establish testing priorities ensuring audit efforts focus on areas presenting greatest organizational risk.
Developing cloud audit programs requires specialized knowledge of available testing procedures appropriate for various cloud service models and deployment architectures. Auditors construct detailed audit programs specifying testing steps for evaluating governance structures, examining compliance documentation, testing technical security controls, reviewing vendor management processes, and assessing incident response capabilities. These audit programs must remain flexible to accommodate the dynamic nature of cloud environments while ensuring comprehensive coverage of relevant control objectives.
Evidence gathering in cloud environments often relies heavily on provider-supplied documentation, third-party attestation reports, automated configuration assessments, and continuous monitoring data rather than traditional manual testing procedures. Auditors learn to effectively leverage Service Organization Control reports providing assurance over cloud provider controls, evaluate the sufficiency and appropriateness of these attestations for specific audit objectives, supplement provider reports with additional testing where necessary, and maintain appropriate professional skepticism when relying on provider-supplied assurance.
Testing methodologies must account for the programmatic nature of cloud environments where infrastructure deploys through code, security controls implement through policy-as-code frameworks, and configurations change dynamically based on workload demands. Auditors develop skills in reviewing infrastructure-as-code templates, examining configuration management repositories, evaluating automated compliance checking tools, and assessing continuous monitoring systems providing ongoing visibility into control effectiveness.
Sampling strategies require careful consideration in cloud environments where organizations may operate thousands of resources across multiple regions and accounts. Auditors learn statistical sampling techniques appropriate for large cloud populations, develop risk-based sampling approaches focusing on critical resources and high-risk configurations, and leverage automated scanning tools enabling population testing rather than sampling where technically feasible.
Documentation standards ensure audit findings receive appropriate support through sufficient, appropriate evidence enabling audit conclusions. Auditors learn to document cloud audit evidence effectively, maintain audit working papers supporting audit opinions, prepare findings communicating control deficiencies clearly, and develop recommendations providing practical guidance for addressing identified weaknesses within cloud environments.
Communication skills become particularly critical as auditors present cloud audit results to stakeholders ranging from technical engineering teams to executive leadership and audit committees. Auditors develop capabilities for translating complex technical findings into business terms, explaining cloud-specific risks to non-technical audiences, presenting recommendations addressing both immediate vulnerabilities and strategic security enhancements, and facilitating productive discussions addressing audit findings constructively.
Candidate Eligibility and Prerequisites
The certification program establishes specific prerequisites ensuring candidates possess foundational knowledge appropriate for advanced cloud auditing studies. While these requirements aim to maintain certification quality and professional standards, the program remains accessible to professionals from diverse backgrounds who demonstrate relevant experience and knowledge combinations.
Professional experience requirements typically emphasize practical exposure to information technology auditing, cloud technologies, information security, or related disciplines. Candidates may satisfy experience requirements through various pathways including work as information technology auditors, security analysts, compliance professionals, cloud engineers, risk management specialists, or consultants advising organizations on cloud implementations. This flexible approach recognizes that valuable cloud auditing expertise develops through multiple career trajectories rather than singular prescribed paths.
Educational background considerations may include formal degrees in information technology, computer science, accounting, business administration, or related fields that provide conceptual foundations supporting advanced certification studies. However, practical experience often substitutes for formal education, acknowledging that many accomplished technology professionals develop expertise through self-directed learning, professional certifications, and hands-on experience rather than traditional academic pathways.
Foundational knowledge expectations span multiple domains including basic information technology concepts, fundamental security principles, elementary cloud computing concepts, introduction to auditing methodologies, and general understanding of regulatory compliance frameworks. Candidates lacking specific background areas may address knowledge gaps through preparatory studies using recommended resources, introductory courses, or foundational certifications before attempting advanced cloud auditing certification examinations.
Examination Structure and Content Distribution
The certification examination employs comprehensive assessments evaluating candidate mastery across all knowledge domains essential for effective cloud auditing practice. Examination design balances breadth and depth, ensuring candidates demonstrate both comprehensive understanding of cloud auditing concepts and detailed knowledge of specific technical and procedural elements.
Question formats typically include multiple-choice items presenting scenarios requiring candidates to identify appropriate audit procedures, evaluate control effectiveness, interpret compliance requirements, or recommend security enhancements. Scenario-based questions predominate, presenting realistic situations that candidates might encounter during actual cloud audit engagements and requiring application of learned concepts to practical circumstances rather than mere recall of memorized information.
Content distribution across knowledge domains receives careful calibration ensuring proportional coverage reflecting the relative importance of each domain to successful cloud auditing practice. Governance and risk management concepts typically receive substantial examination emphasis given their foundational importance to effective cloud auditing. Compliance frameworks similarly receive significant coverage reflecting the compliance-driven nature of many cloud audit engagements. Technical security controls and audit methodologies each receive appropriate attention ensuring candidates demonstrate comprehensive capabilities across all essential competency areas.
Examination difficulty calibration aims to differentiate candidates possessing thorough cloud auditing expertise from those with superficial knowledge. Question development processes involve subject matter experts establishing appropriate difficulty levels, conducting question reviews ensuring technical accuracy, eliminating ambiguous or poorly constructed items, and validating that examinations effectively measure intended competencies. Statistical analysis of examination results informs ongoing refinement ensuring examinations maintain consistent difficulty and reliably identify qualified candidates.
Time allocation provides sufficient opportunity for thoughtful consideration of examination questions while maintaining appropriate pressure reflecting real-world decision-making constraints. Candidates receive clear guidance regarding examination duration, number of questions, question format distribution, and scoring methodologies enabling effective time management throughout examination sessions.
Strategic Preparation Approaches for Examination Success
Successful certification attainment requires deliberate preparation strategies addressing all examination domains through diverse learning modalities suited to individual learning preferences and constraints. Candidates benefit from developing comprehensive study plans allocating sufficient time for thorough content mastery while maintaining sustainable pacing avoiding burnout during intensive preparation periods.
Official study materials provided by certification bodies represent primary preparation resources, offering authoritative content aligned precisely with examination objectives. These materials typically include comprehensive study guides detailing required knowledge across all domains, practice questions illustrating examination formats and difficulty levels, and supplementary resources addressing specific technical topics in greater depth. Candidates should prioritize official materials ensuring preparation efforts focus on examination-relevant content rather than tangential topics.
Supplementary preparation resources expand learning beyond official materials, providing alternative explanations, additional practice opportunities, and deeper technical exploration of specific topics. Published study guides from reputable authors offer structured approaches to examination preparation, often including practice examinations, study tips, and memory aids facilitating content retention. Online courses provide interactive learning experiences combining video instruction, hands-on laboratories, practice assessments, and instructor support addressing learner questions.
Hands-on experience with cloud platforms substantially enhances preparation effectiveness by transforming abstract concepts into concrete understanding through practical application. Candidates benefit enormously from establishing personal cloud accounts enabling direct experimentation with cloud services, security configurations, access controls, monitoring tools, and other technologies covered in examination content. Many cloud providers offer free tier access or limited-time credits supporting learning activities without significant financial investment.
Laboratory environments specifically designed for cloud security learning provide structured hands-on experiences covering examination-relevant scenarios. These environments present realistic cloud configurations, security challenges, compliance scenarios, and audit situations enabling candidates to practice applying learned concepts in controlled settings closely resembling actual audit engagements. Candidates develop deeper understanding and greater confidence through repeated practical application of audit methodologies, security assessments, and compliance evaluations in these laboratory contexts.
Study groups facilitate collaborative learning through peer interaction, knowledge sharing, mutual support, and collective problem-solving. Participants benefit from exposure to diverse perspectives, explanations of difficult concepts from multiple viewpoints, opportunities to teach others reinforcing personal understanding, and motivational support maintaining preparation momentum through challenging study periods. Online communities, local professional associations, and workplace colleagues all provide potential study group participants.
Practice examinations serve critical roles in preparation by familiarizing candidates with question formats, identifying knowledge gaps requiring additional study, building examination-taking stamina, and reducing test anxiety through repeated exposure to examination-like conditions. Candidates should attempt multiple practice examinations throughout preparation, carefully reviewing incorrect answers to understand underlying concepts, and using performance feedback to guide subsequent study priorities.
Time management strategies during both preparation and examination require careful attention. During preparation, candidates benefit from creating structured study schedules allocating specific time blocks to each knowledge domain, establishing regular study routines maintaining consistent progress, and setting milestone objectives providing motivation and progress indicators. During examinations, effective time management involves reading questions carefully, allocating appropriate time per question based on total examination duration, answering confidently known questions first, and returning to challenging items with remaining time.
Career Advantages and Professional Opportunities
Professionals holding specialized cloud auditing credentials enjoy substantial career advantages stemming from the credential's validation of scarce, highly valued expertise. Organizations across industries actively seek professionals capable of effectively auditing cloud environments, creating strong demand for qualified cloud auditing specialists and favorable career prospects for credential holders.
Compensation advantages frequently accompany specialized cloud auditing certifications as organizations recognize the value of verified expertise and willingly invest in attracting and retaining qualified professionals. Salary surveys consistently demonstrate compensation premiums associated with relevant certifications, with cloud auditing specialists often commanding premium compensation compared to general information technology auditors lacking specialized cloud credentials.
Career advancement opportunities expand significantly as cloud auditing expertise becomes increasingly essential for senior audit positions, management roles, and specialized consulting engagements. Professionals holding cloud auditing credentials position themselves favorably for promotion to audit manager positions, senior consultant roles, practice leadership opportunities, and executive positions overseeing comprehensive audit programs encompassing cloud environments alongside traditional infrastructure.
Role diversity enables cloud auditing professionals to pursue various career paths aligned with personal interests and strengths. Internal audit departments within large enterprises employ cloud auditing specialists conducting assessments of corporate cloud implementations. External audit firms engage cloud auditing professionals supporting financial statement audits, regulatory compliance examinations, and advisory services for audit clients. Consulting organizations employ cloud security auditors delivering specialized assessments, security program development, compliance gap analyses, and vendor evaluation services. Cloud service providers themselves employ auditing professionals managing compliance programs, supporting customer audits, and conducting internal security assessments.
Industry mobility benefits from the broadly applicable nature of cloud auditing expertise relevant across virtually all industry sectors adopting cloud technologies. Professionals can transition between industries while leveraging specialized cloud auditing capabilities, accessing opportunities in financial services, healthcare, government, technology, retail, manufacturing, and numerous other sectors. This industry flexibility provides career resilience and diverse opportunities throughout professional careers.
Geographic flexibility emerges from the globally recognized nature of cloud auditing certifications and the universal challenges organizations face securing cloud environments regardless of location. Professionals can pursue opportunities across regions, countries, and continents, with cloud auditing expertise remaining relevant despite varying regional regulatory frameworks and industry focuses. Remote work opportunities particularly suit cloud auditing professionals whose work often focuses on cloud-based systems accessible from any location.
Professional networking opportunities expand through certification attainment as credential holders join professional communities connecting thousands of cloud security and auditing professionals worldwide. These networks facilitate knowledge sharing, career mentoring, job opportunity awareness, and collaborative problem-solving around common challenges. Active participation in professional communities enhances career prospects through increased visibility, relationship development, and access to unadvertised opportunities.
Continuing relevance throughout careers stems from the enduring importance of cloud computing in modern enterprise architectures. Unlike certifications focused on specific technology products that may become obsolete as technologies evolve, cloud auditing expertise addresses fundamental challenges that persist regardless of specific cloud platform selections. This enduring relevance provides confidence that certification investments deliver long-term career value.
Credential Maintenance and Ongoing Professional Development
Professional certifications require ongoing maintenance ensuring credential holders maintain current knowledge as cloud technologies, security threats, compliance requirements, and auditing methodologies evolve. Certification maintenance programs establish requirements for continuing education, professional practice, and periodic recertification validating ongoing expertise throughout professional careers.
Continuing education requirements typically mandate credential holders complete specified numbers of professional development hours annually or within defined certification periods. These requirements ensure professionals regularly engage with evolving knowledge, new technologies, emerging threats, updated compliance frameworks, and advancing audit methodologies maintaining professional currency. Acceptable continuing education activities often include attending professional conferences, completing training courses, participating in webinars, publishing articles, delivering presentations, and engaging in other learning activities advancing professional knowledge.
Professional practice requirements may mandate credential holders maintain active involvement in cloud auditing activities ensuring certifications reflect current practical expertise rather than historical knowledge becoming stale through disuse. These requirements acknowledge that effective auditing demands ongoing practical application maintaining and advancing capabilities through regular engagement with auditing challenges.
Recertification processes periodically validate ongoing credential holder expertise through various mechanisms potentially including renewal examinations, portfolio submissions demonstrating professional achievements, documentation of continuing education completion, or combinations of these approaches. Recertification intervals typically extend multiple years providing reasonable periods for accumulating required professional development while ensuring periodic validation of ongoing expertise.
Continuing education opportunities abound for cloud auditing professionals committed to ongoing development. Professional associations regularly conduct conferences featuring presentations on emerging technologies, evolving threats, new regulatory requirements, and innovative audit approaches. These conferences provide concentrated learning opportunities, networking experiences, and exposure to leading practitioners sharing insights and experiences. Training providers offer courses addressing specific cloud technologies, security tools, compliance frameworks, and audit methodologies enabling targeted skill development in particular areas.
Industry publications, research reports, white papers, and technical blogs provide ongoing access to evolving knowledge without requiring formal course enrollment. Cloud service providers publish extensive documentation, security guidance, compliance frameworks, and architectural best practices supporting effective utilization of their platforms. Industry analysts produce research examining cloud adoption trends, security challenges, emerging technologies, and strategic considerations. Following these information sources enables continuous learning integrated naturally into professional routines.
Professional communities including online forums, social media groups, professional association chapters, and local meetups facilitate ongoing knowledge exchange through peer interaction. Participants share experiences, discuss challenges, exchange solutions, and collectively advance understanding of cloud auditing topics. Active community engagement provides continuous informal learning supplementing formal education activities.
Examination Registration and Administrative Procedures
Candidates pursuing certification must navigate administrative processes including examination registration, scheduling, fee payment, accommodation requests, and examination day procedures. Understanding these administrative aspects ensures smooth progression through certification attainment without unnecessary complications or delays.
Registration processes typically begin through official certification body websites providing comprehensive information about certification requirements, examination details, pricing, scheduling options, and candidate resources. Candidates create accounts enabling examination registration, access to preparatory materials, examination scheduling, and score reporting. Account establishment requires providing accurate personal information, contact details, and relevant demographic data supporting program administration.
Examination scheduling systems enable candidates to select examination dates, times, and locations convenient for their circumstances. Testing availability varies based on delivery methods potentially including computer-based testing at authorized testing centers, online proctored examinations administered remotely, or paper-based examinations at specified locations. Candidates should schedule examinations allowing sufficient preparation time while maintaining momentum and motivation through commitment to specific examination dates.
Fee structures cover examination administration costs, score processing, initial certification conferral, and various administrative services. Fee amounts vary across certification programs, geographic regions, and candidate categories with potential discounts for professional association members, students, groups, or early registration. Candidates should understand fee structures, payment methods, refund policies, and rescheduling options before completing registration.
Accommodation procedures support candidates requiring testing modifications due to disabilities, medical conditions, or other circumstances necessitating special arrangements. Candidates needing accommodations typically submit formal requests accompanied by supporting documentation from qualified professionals, allowing certification bodies to evaluate needs and arrange appropriate modifications ensuring fair, accessible testing experiences. Common accommodations include extended time allocations, alternate question formats, assistive technologies, or modified testing environments.
Examination day procedures establish expectations regarding arrival times, required identification, prohibited items, examination rules, and testing environment conditions. Candidates must arrive sufficiently early to complete check-in procedures, present valid government-issued identification matching registration information, and secure personal belongings. Testing centers typically prohibit electronic devices, study materials, bags, outerwear, and other items that could facilitate cheating or disrupt testing. Understanding and preparing for these procedures reduces examination day stress enabling focused performance.
Examination Results and Score Interpretation
Examination completion initiates scoring processes determining candidate success or failure based on demonstrated knowledge across examination domains. Understanding score reporting, passing standards, result interpretation, and subsequent steps ensures candidates appropriately respond to examination outcomes.
Score reporting timelines vary based on examination delivery methods and scoring procedures. Computer-based examinations often provide immediate preliminary results upon examination completion, offering rapid feedback regarding examination outcomes. Official score reports typically follow within specified periods providing detailed performance information, domain-level feedback, and certification conferral documentation for successful candidates.
Passing standards establish minimum performance thresholds candidates must exceed to demonstrate adequate expertise for certification. These standards typically reflect criterion-referenced approaches establishing absolute performance requirements rather than norm-referenced standards comparing candidates against peer performance. Criterion-referenced standards ensure consistent expertise levels among credential holders regardless of examination cohort difficulty variations.
Score interpretation requires understanding scoring methodologies, scale meanings, and performance feedback. Candidates receive overall scores indicating examination performance alongside domain-level scores providing granular feedback regarding strengths and weaknesses. Domain scores help unsuccessful candidates identify specific areas requiring additional study before retaking examinations.
Successful candidates receive official certification conferral following examination passage, gaining authorization to use certification designations, receiving digital certificates documenting achievement, and obtaining access to credential holder resources. Certification conferral transforms examination success into professionally recognized credentials enhancing career prospects and validating expertise to employers, clients, and professional peers.
Unsuccessful candidates must evaluate domain performance feedback, identify knowledge gaps, adjust preparation strategies, and schedule subsequent examination attempts. Most certification programs permit multiple examination attempts enabling candidates to ultimately achieve certification despite initial setbacks. Candidates should approach unsuccessful attempts as learning opportunities, carefully analyzing performance patterns, addressing identified weaknesses, and returning to examinations better prepared for success.
Integration with Complementary Professional Certifications
Cloud auditing expertise synergizes effectively with numerous complementary certifications creating powerful credential combinations expanding professional capabilities and career opportunities. Strategic certification portfolios demonstrate breadth and depth of expertise appealing to employers seeking versatile professionals capable of addressing diverse organizational needs.
General auditing certifications including Certified Internal Auditor credentials provide foundational auditing knowledge, professional standards understanding, and audit methodology expertise complementing specialized cloud auditing technical knowledge. Professionals holding both general auditing and specialized cloud auditing credentials demonstrate comprehensive auditing capabilities spanning traditional and cloud environments.
Information security certifications including Certified Information Systems Security Professional credentials validate broad cybersecurity knowledge spanning security domains, risk management principles, and security program development. Combining information security and cloud auditing certifications creates powerful expertise spanning security architecture, control implementation, and audit validation.
Cloud platform certifications offered by major cloud service providers validate technical proficiency with specific cloud environments, services, and architectural patterns. Professionals combining cloud auditing credentials with platform-specific certifications demonstrate both auditing expertise and deep technical knowledge of particular cloud environments, creating unique capabilities for conducting thorough, technically sophisticated cloud audits.
Governance and compliance certifications focusing on specific regulatory frameworks, industry standards, or governance methodologies complement cloud auditing expertise by deepening knowledge of particular compliance contexts. Healthcare compliance certifications, privacy certifications, and governance framework certifications all enhance cloud auditing capabilities within specific contexts.
Risk management certifications validate capabilities in enterprise risk management, risk assessment methodologies, and risk governance frameworks. Combining risk management and cloud auditing credentials positions professionals as strategic advisors capable of integrating cloud security considerations into broader enterprise risk management programs.
Global Recognition and Regional Variations
Cloud auditing certifications generally achieve broad international recognition given the globally distributed nature of cloud computing and universal challenges organizations face securing cloud environments. However, regional variations in regulatory frameworks, industry practices, and professional development ecosystems create considerations for professionals pursuing credentials and practicing across different geographic contexts.
Professional recognition spans numerous countries as organizations worldwide adopt cloud technologies and require qualified auditing professionals. Credential holders can leverage certifications supporting career opportunities across continents, though specific demand patterns, compensation levels, and role expectations vary based on regional cloud adoption maturity, industry concentrations, and local professional development cultures.
Regulatory framework variations create regional specialization opportunities as specific compliance requirements shape cloud auditing practices differently across jurisdictions. European professionals navigate General Data Protection Regulation requirements extensively, while American counterparts focus heavily on frameworks like HIPAA and state-specific privacy laws. Understanding regional regulatory variations enables professionals to develop specialized expertise valuable within particular geographic markets.
Language availability for certification materials, examinations, and professional resources affects accessibility across regions. Major certifications typically offer examinations in multiple languages supporting global accessibility, though English often predominates in certification materials given the language's dominance in technology sectors. Candidates should verify language availability when considering certifications ensuring adequate linguistic support for successful preparation and examination.
Professional community development varies regionally with some areas featuring robust local chapters, regular professional events, and active networking opportunities while other regions offer fewer localized professional development resources. Regional community participation enables professionals to connect with local practitioners, understand regional practice variations, and access geographically relevant career opportunities.
Emerging Trends Shaping Cloud Auditing Futures
Cloud computing technologies continue evolving rapidly, introducing new architectures, services, deployment models, and security paradigms that shape future cloud auditing practices. Professionals maintaining career relevance must anticipate emerging trends, adapt methodologies accordingly, and continuously expand capabilities addressing novel auditing challenges.
Multi-cloud and hybrid cloud architectures increasingly dominate enterprise cloud strategies as organizations distribute workloads across multiple cloud providers, combine cloud and on-premises infrastructure, and adopt best-of-breed service selections. This architectural complexity requires auditors to develop capabilities spanning multiple cloud platforms, understand integration security challenges, evaluate consistency of security controls across heterogeneous environments, and assess governance structures maintaining unified oversight despite distributed architectures.
Containerization and microservices architectures transform application development and deployment patterns, introducing new security considerations and audit challenges. Auditors must understand container security models, orchestration platform configurations, service mesh architectures, and continuous deployment pipelines enabling rapid application updates. Traditional audit approaches focusing on static configurations become inadequate as containerized environments implement dynamic, ephemeral infrastructure where resources continuously deploy and terminate based on application demands.
Artificial intelligence and machine learning adoption within cloud environments creates new audit considerations regarding model security, training data protection, algorithmic fairness, and automated decision-making accountability. Auditors need developing capabilities in assessing machine learning model security, evaluating training data quality and protection, understanding explainability requirements, and auditing automated decision systems for compliance with emerging algorithmic accountability regulations.
Edge computing architectures distributing computation closer to data sources introduce additional security and audit considerations. Auditors must understand edge infrastructure security models, evaluate connectivity security between edge locations and central cloud environments, assess data protection across distributed edge deployments, and examine governance structures maintaining oversight across geographically dispersed edge installations.
Quantum computing developments, though currently nascent, present long-term implications for cloud security and cryptography. Forward-thinking auditors monitor quantum computing advances, understand post-quantum cryptographic developments, and anticipate future audit considerations regarding quantum-resistant security implementations protecting cloud data against future quantum cryptanalysis capabilities.
Zero-trust architecture adoption transforms cloud security models from perimeter-based approaches to continuous verification models assuming no inherent trust. Auditors must understand zero-trust principles, evaluate identity-centric security implementations, assess continuous authentication and authorization mechanisms, and examine micro-segmentation approaches limiting lateral movement across cloud resources.
Infrastructure-as-code and policy-as-code approaches enable programmatic infrastructure deployment and automated security control implementation. These approaches require auditors to develop capabilities reviewing code repositories, evaluating automated deployment pipelines, assessing version control practices, and understanding continuous compliance monitoring systems automatically enforcing security policies across cloud environments.
Ethical Considerations and Professional Responsibilities
Cloud auditing professionals play a pivotal role in ensuring that organizations maintain secure, compliant, and trustworthy cloud environments. However, with such responsibilities comes the need for a high degree of ethical accountability. These professionals are entrusted with sensitive information, and their judgments and decisions directly influence the security, compliance, and financial integrity of their clients. Maintaining ethical standards is not only a legal and professional requirement but also essential for preserving the trust that stakeholders place in auditors and their work. Cloud auditors must recognize and navigate the ethical challenges that come with access to proprietary data and sensitive security information, while always striving to maintain professionalism in their practice.
This article outlines the ethical obligations and responsibilities of cloud auditing professionals, emphasizing confidentiality, objectivity, competence, and professional care. By upholding these principles, auditors can ensure that their work remains credible, valuable, and aligned with industry standards.
Confidentiality: Protecting Sensitive Information
One of the most fundamental ethical responsibilities that cloud auditors must adhere to is confidentiality. Given the sensitive nature of the information auditors handle, ensuring that this data is protected from unauthorized disclosure is paramount. Cloud auditors routinely access a wide range of confidential materials, including business intelligence, internal security protocols, vulnerability assessments, and compliance documentation. If such data is leaked or mishandled, it can have far-reaching consequences for both the auditing organization and its clients, including reputational damage, financial losses, or even legal ramifications.
Confidentiality obligations go beyond simply preventing the unauthorized disclosure of information. Auditors are required to implement robust procedures for data handling and storage to mitigate the risk of accidental leaks. This includes using secure communication channels, ensuring data encryption, and restricting access to sensitive materials only to authorized individuals. Moreover, auditors must exercise caution when sharing any information related to an engagement. This includes sharing information with other professionals, such as colleagues or third-party consultants, or even within the context of internal audits. Clear guidelines should always govern how and when information is disclosed to ensure that only the necessary parties are privy to confidential data.
It is also crucial for auditors to recognize the importance of informed consent when dealing with client data. When auditors handle data, they must ensure that clients have granted explicit permission for the audit engagement, particularly when sensitive or proprietary data is involved. Transparency regarding what data will be accessed and how it will be used is critical in maintaining the trust and ethical integrity of the engagement.
Objectivity and Independence: Ensuring Unbiased Professional Judgment
Objectivity and independence are foundational principles that underpin the integrity of the auditing profession. Cloud auditors are expected to maintain an impartial and unbiased perspective while performing their duties. This ensures that their findings and recommendations are based purely on facts and evidence, not influenced by personal interests or external pressures. If auditors fail to maintain objectivity, the credibility of their work can be compromised, leading to flawed audit conclusions that may harm clients, stakeholders, or even the broader industry.
Auditors must be especially mindful of any potential conflicts of interest that may arise during an engagement. For instance, auditors who have a financial interest in a particular company or vendor may be influenced, consciously or unconsciously, to present favorable findings, even if those findings do not accurately reflect the state of the client’s cloud infrastructure. In such cases, auditors are ethically obligated to disclose their conflicts of interest and recuse themselves from the engagement to ensure the results are free from bias.
Independence goes beyond merely avoiding conflicts of interest. Cloud auditors should also avoid situations where their professional judgment may be influenced by external factors, such as pressure from clients to overlook certain vulnerabilities or risks. Auditors must have the courage and integrity to voice concerns when they discover security weaknesses, compliance violations, or other areas of concern, even when these findings may be unfavorable to the client.
Maintaining independence is not only a professional obligation but also a legal requirement in many jurisdictions. Ethical guidelines and regulatory frameworks, such as the International Standards for the Professional Practice of Internal Auditing (IPPF) and the International Auditing and Assurance Standards Board (IAASB), emphasize the importance of auditors’ independence to safeguard their findings' credibility.
Competence: Conducting Audits Within One’s Area of Expertise
Competence is another cornerstone of ethical auditing. Professionals must only take on engagements where they possess the requisite knowledge, skills, and expertise to conduct a thorough, accurate, and effective audit. The ability to assess complex cloud systems and security architectures requires deep technical understanding and ongoing learning to stay abreast of evolving technologies, vulnerabilities, and regulatory changes.
Cloud auditing is an intricate and specialized field, and auditors must be transparent about their competencies. Accepting assignments that exceed one’s expertise not only risks providing subpar audits but also violates ethical standards. For example, a cloud auditor who lacks expertise in a particular cloud platform or regulatory framework may struggle to provide accurate assessments, thereby compromising the value of the audit.
Ethical competence also involves knowing when to seek help. When auditors encounter areas that fall outside their knowledge or skill set, they should consult specialists or refer clients to other qualified professionals who can provide more in-depth expertise. The ethical imperative is to maintain the quality of the audit by ensuring the auditor’s work is always accurate and well-informed.
Furthermore, maintaining competence is not a one-time achievement. It is an ongoing process that requires auditors to engage in continuous professional development. This could include obtaining additional certifications, attending workshops or conferences, or staying up-to-date with the latest advancements in cloud technologies and cybersecurity. Without continuous education, auditors risk becoming outdated in a rapidly changing technological landscape, which undermines the quality of their audits and their professional credibility.
Professional Care: Exercising Diligence and Attention to Detail
Due professional care is an ethical requirement that mandates auditors approach their work with the necessary diligence, thoroughness, and attention to professional standards. A cloud audit is only as good as the effort and care invested into it. Auditors are expected to adopt systematic methodologies and best practices to ensure they deliver reliable, high-quality results. This includes performing comprehensive testing, gathering sufficient evidence, and documenting their findings thoroughly.
Negligence or shortcuts in an audit engagement can have serious repercussions, not just for the client but also for the auditor. For instance, if an auditor fails to conduct sufficient testing or overlook key areas of risk, they may miss critical security vulnerabilities that could expose the client to cyber threats. Similarly, inadequate documentation or failure to support audit conclusions with strong evidence can lead to challenges regarding the validity of the audit.
Ethical auditors understand that their work has significant consequences, and they must take all necessary steps to ensure the accuracy and completeness of their findings. They must never compromise the quality of their work to meet tight deadlines or to please clients, even if it means putting in extra time and effort to ensure a thorough audit process.
A commitment to due professional care also means that auditors are willing to raise concerns when they identify issues that may not be popular with the client, such as compliance gaps or security deficiencies. Ethical auditors must be willing to act in the best interests of the organization, even if their findings are not well received.
Accountability: Upholding Integrity in the Face of Pressure
Accountability is a key principle that runs through every aspect of ethical auditing. Auditors are held accountable not only to their clients but also to their professional organizations, regulatory bodies, and society at large. In a world where financial, reputational, and legal risks are constantly in play, auditors are often under pressure to deliver favorable outcomes. However, ethical auditors must resist any temptation to compromise their professional standards in the face of such pressures.
For example, a cloud auditor might face pressure from a client to overlook certain vulnerabilities, particularly if addressing them would be costly or time-consuming. However, an ethical auditor must prioritize the integrity of the audit process and deliver findings that reflect the true security and compliance posture of the client, regardless of how those findings may affect the client’s bottom line.
Accountability also involves transparency in communication. Auditors must ensure that their conclusions and recommendations are clearly articulated and supported by evidence. Any ambiguity in audit reports could undermine the audit’s value and the client’s ability to act on the findings. Ethical auditors take full responsibility for their work, standing behind their audit results even when facing criticism.
Conclusion
Cloud auditors often encounter situations where they must make difficult ethical decisions. For instance, if an auditor uncovers significant risks or breaches that could expose a client to major compliance violations or cyberattacks, they must decide how to present this information. The ethical responsibility is clear: auditors must report their findings honestly, even if doing so might create tension with clients or colleagues. However, the manner in which auditors communicate these findings is equally important. Ethical auditors are skilled in conflict resolution and know how to convey difficult messages diplomatically, ensuring that their recommendations are understood and acted upon.
Ethical decision-making also extends to how auditors handle potential conflicts of interest. If auditors find themselves in situations where personal interests, financial gain, or other external factors could compromise their objectivity, they must take appropriate actions to avoid conflicts. This includes disclosing potential conflicts to relevant stakeholders and recusing themselves from engagements where their impartiality cannot be maintained.
Cloud auditors hold significant ethical responsibilities that influence not only the security and compliance of the organizations they audit but also the trustworthiness of the auditing profession itself. By adhering to principles of confidentiality, objectivity, competence, and professional care, auditors ensure the integrity of their work and safeguard the interests of stakeholders. Maintaining ethical standards is crucial for building and preserving the trust that clients and the broader industry place in auditors. Cloud auditing professionals must always strive for the highest ethical standards to navigate the complexities of the cloud landscape and contribute positively to their organizations and society.
Frequently Asked Questions
Where can I download my products after I have completed the purchase?
Your products are available immediately after you have made the payment. You can download them from your Member's Area. Right after your purchase has been confirmed, the website will transfer you to Member's Area. All you will have to do is login and download the products you have purchased to your computer.
How long will my product be valid?
All Testking products are valid for 90 days from the date of purchase. These 90 days also cover updates that may come in during this time. This includes new questions, updates and changes by our editing team and more. These updates will be automatically downloaded to computer to make sure that you get the most updated version of your exam preparation materials.
How can I renew my products after the expiry date? Or do I need to purchase it again?
When your product expires after the 90 days, you don't need to purchase it again. Instead, you should head to your Member's Area, where there is an option of renewing your products with a 30% discount.
Please keep in mind that you need to renew your product to continue using it after the expiry date.
How often do you update the questions?
Testking strives to provide you with the latest questions in every exam pool. Therefore, updates in our exams/questions will depend on the changes provided by original vendors. We update our products as soon as we know of the change introduced, and have it confirmed by our team of experts.
How many computers I can download Testking software on?
You can download your Testking products on the maximum number of 2 (two) computers/devices. To use the software on more than 2 machines, you need to purchase an additional subscription which can be easily done on the website. Please email support@testking.com if you need to use more than 5 (five) computers.
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by all modern Windows editions, Android and iPhone/iPad versions. Mac and IOS versions of the software are now being developed. Please stay tuned for updates if you're interested in Mac and IOS versions of Testking software.


